
Microsoft는 월에서 열린 미디어 기업의 컴퓨터에 Windows 관리 공격의 세부 사항을 발표.
나는n 공격, 범죄자들은 최신 개월 만에 범죄 그룹 내에서 인기를 얻고 있다는 유명한 WinRAR과 취약점을 이용. 해커는 즉시 체크 포인트 회사에 의해 발행 후 그것으로 자신을 무장, 2 월 20. 당시 연구원들은 특수 구성 파일을 사용하여 이 취약점 코드를 통과하는 방법을 시연했습니다. (압축 파일 형식) 랜덤코드 적용 가능.새롭게 개선된 WinRAR 버전은 Check Point가 출판되기 한 달 전에 발행되었습니다., 하지만 3월에도 Microsoft는 여전히 CVE-2018-20250 공격을 목격했습니다..
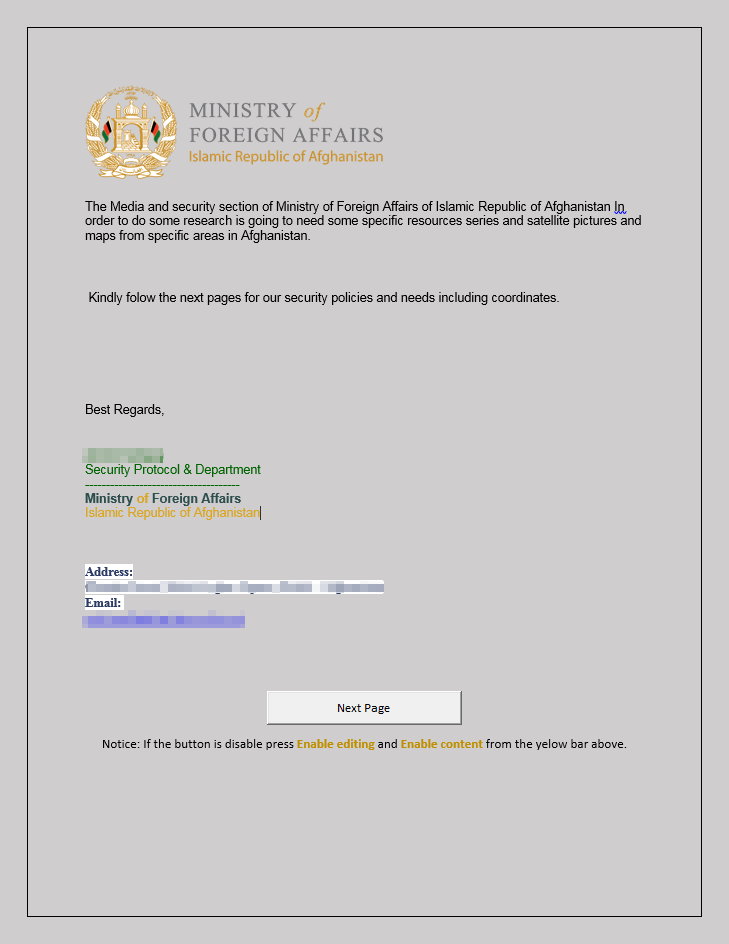
3월 캠페인에서는, 해커들이 아프가니스탄 내무부로부터 낚시 편지를 보낸 것으로 추정됨. 그들이 적용한 사회 공학 방법은 WinRAR의 제한된 취약성 프레임워크에서 완전한 원격 시스템 불신을 보장하기 위해 신중하게 계획되었습니다..
다른 OneDrive 문서의 링크와 함께 Microsoft Word 파일이 포함된 낚시 편지. 공격 감지를 방지하기 위한 악성 코드 매크로가 포함되어 있지 않습니다.. 하나, OneDrive 문서에는 맬웨어 매크로가 포함되어 있으며 활성화 후 피해자의 시스템이 새로운 해커의 소프트웨어를 받았습니다..
악성 매크로가 포함된 문서를 다운로드했습니다.
문서에는 "다음 페이지필요한 파일 DLD가 없고 컴퓨터를 다시 시작해야 한다는 가짜 알림이 포함된 버튼. 취약점으로 인해 악성 프로그램이 특정 폴더에 파일을 다운로드할 수 있지만 즉시 시작할 수는 없으므로 이 트릭이 필요했습니다.. 이를 고려하여, 이상적인 솔루션은 "Startup" 폴더에 프로그램을 넣는 것이었습니다.. 컴퓨터를 다시 시작한 후 이 폴더의 파일이 즉시 시작되었습니다..
감염된 시스템을 다시 시작한 후 해커가 시스템에 대한 전체 액세스 권한을 여는 백도어 PowerShell을 시작했습니다.. 이 백도어와 기타 기능을 사용하면 사이버 밴드가 흙탕물 공격에 대한 책임이 있습니다.
“이 PowerShell 스크립트는 과거 MuddyWater 캠페인에 사용된 스크립트와 유사합니다.”, – 마이크로소프트 전문가 확인.
