
Sicherheitsexperten sprechen seit langem davon, die Aktivität von Exploit-Kits zu reduzieren, viele von ihnen bleiben noch „in service“, weiter zu verbessern und die Nutzlast zu ändern.
diene of these long-known players’ researcher ist das RIG-Exploit-Kit.Vor kurzem, Experten bemerkten, dass RIG damit begann, den Eris-Verschlüsseler zu verteilen, erstmals im Mai gesehen 2019. Forscher Michael Gillespie was first to discovere an extortionist, when the malware appeared on the ID Ransomware.
Now an independent information security specialist, known under the pseudonym nao_sec, noticed that the new campaign of RIG uses Eris as the payload.
“A malvertising campaign using the popcash ad network is redirecting users to the RIG exploit kit. The kit will attempt to exploit a Shockwave (SWF) vulnerability in the browser. If successful, it will automatically download and install the ERIS Ransomware on to the computer”, — reported nao_sec.
The extortionist encrypts files of his victims, changing their extensions to .ERIS.
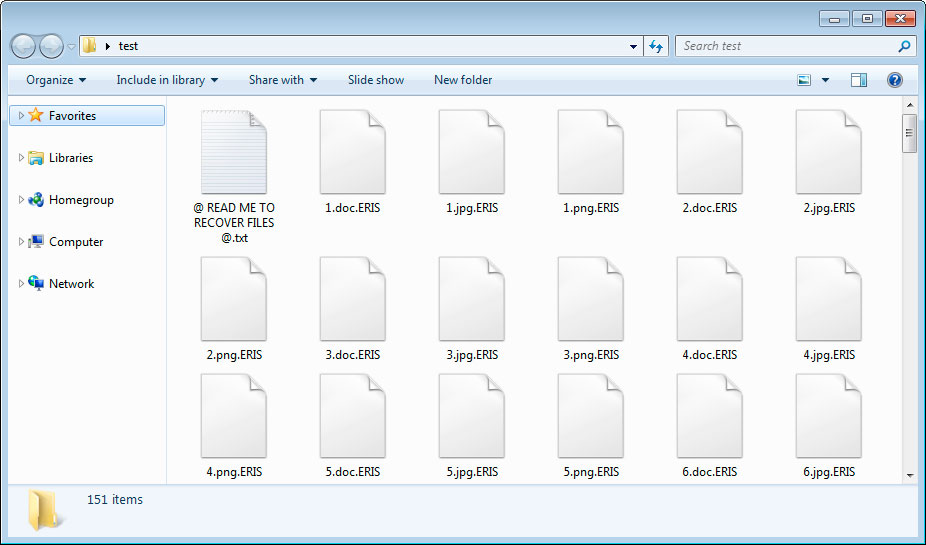
In each folder that was scanned, the extortionist also creates a redemption note with the name @ READ ME TO RECOVER FILES @ .txt, which instructs the victim to contact Limaooo@cock.li for payment instructions. A unique identifier is included in this ransom note, which the victim must send to the ransomware developer so that he can perform a free test transcript of a single file.
The researchers note that, Unglücklicherweise, there is no way to decrypt the files affected by Eris, without paying the ransom to the attackers.
