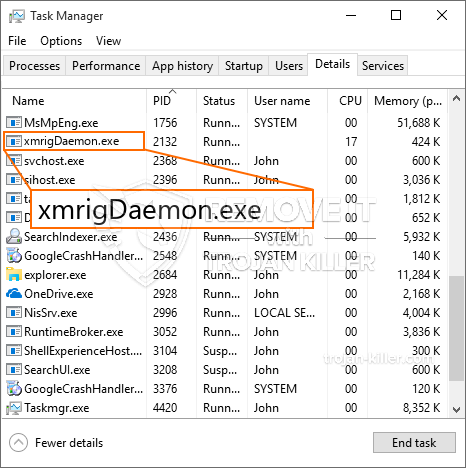
Brandneu, wirklich unsicher Kryptowährung Bergmann-Infektion wurde von Sicherheits Forscher identifiziert. die Malware, namens XmrigDaemon.exe kann Betroffene infizieren, indem sie verschiedene Möglichkeiten nutzen. Der wichtigste Punkt hinter dem XmrigDaemon.exe Bergmann ist zu Kryptowährung miner Aufgaben auf den Computersystemen der Betroffenen einsetzen, um zu erhalten Monero bei Erkrankten Ausgaben Token. Das Ergebnis dieses Bergmanns sind die erhöhten Stromrechnungen. Wenn Sie ihn längere Zeit verlassen, kann XmrigDaemon.exe auch die Komponenten Ihres Computers beschädigen.
XmrigDaemon.exe: Verteilungsmethoden
Das XmrigDaemon.exe Malware verwendet zwei populäre Techniken, die verwendet werden, Computer Ziele zu infizieren:
- Payload Lieferung mit Vor-Infektionen. Wenn eine ältere Malware von XmrigDaemon.exe auf den betroffenen Systemen bereitgestellt wird, kann sie sich automatisch aktualisieren oder eine neuere Version herunterladen und installieren. Dies ist möglich durch den Upgrade-Befehl integriert, die den Start erwirbt. Dies wird durch die Verknüpfung zu einem bestimmten vordefinierten Hacker-kontrollierten Server durchgeführt, die den Malware-Code gibt. Das heruntergeladene Virus wird den Namen eines Windows-Dienstes erhalten sowie in den platziert werden “%System% temp” Bereich. Vital Gebäude und Betriebssystem-Anordnung Dateien werden verändert, um eine unnachgiebige und stille Infektion zu ermöglichen,.
- Software-Programm Ausnutzen von Sicherheitslücken. Die aktuellste Variante der Malware XmrigDaemon.exe wurde von einigen Unternehmen entdeckt, weit verstanden in der Ransomware Streiks genutzt wird. Die Infektionen werden durchgeführt, durch offene Dienste gezielt den TCP-Port. Die Streiks werden von einem Hacker-kontrollierten Rahmen automatisiert die darauf abzielt, ob der Port offen ist. Wenn dieses Problem erfüllt ist, wird es die Lösung Scannen und Abrufen von Informationen über sie, bestehend aus irgendeiner sowie Setup Datenvariation. Exploits und beliebte Benutzernamen sowie Passwort Mixes getan werden könnte. Wenn die nutzen gegen den gefährdeten Code auf den Weg der Bergmann wird neben der Hintertür freigegeben werden. Diese präsentiert sicherlich die eine Doppelinfektion.
Neben diesen Verfahren können auch andere Verfahren ebenfalls verwendet werden. Miners kann durch Phishing-Mails verteilt werden, die in loser Schüttung in einer SPAM-ähnlichen Art und Weise gesendet werden, sowie hängen von sozialen Design-Methoden, um die Opfer richtig zu denken, zu verwirren, dass sie tatsächlich eine Nachricht von einem echten Service oder Unternehmen erhielten. Die Virendaten können entweder direkt angebracht oder in den Körpermaterialien in Multimedia-Webinhalten oder Nachrichtenverbindungen platziert.
Die Täter können ebenfalls destruktiv Landung Webseiten erzeugen, die Anbieter herunterladen imitieren können und Web-Seiten installieren, Software-Download-Sites sowie andere häufig zugegriffen Standorte. Wenn sie ähnlich klingender Domain, um einen echten Adressen sowie Sicherheitszertifizierungen verwenden könnten die Individuen in ihnen Eingriff werden dazu gezwungen. In einigen Fällen öffnen sie einfach die Bergmann-Infektion aktivieren.
Eine weitere Strategie wäre sicherlich Strecken Service-Provider zu verwenden, die verteilt werden können diese Ansätze oder durch File-Sharing-Netzwerke nutzen, BitTorrent ist nur einer der prominentesten. Es wird häufig zu zerstreuen sowohl legit Software-Programm und Daten sowie Piraten Webinhalte genutzt. Zwei der beliebtesten Streckenanbieter sind die folgenden:
Verschiedene andere Ansätze, die von den bösen Jungs daran gedacht werden kann, für die Verwendung von Internet-Browser bestehen Hijackern -unsafe Plugins, die mit einem der bekanntesten Web-Internet-Browsern kompatibel gemacht werden. Sie sind mit gefälschten Kundenrezensionen zu den entsprechenden Repositories vorgelegt und auch Entwickler-Anmeldeinformationen. In den meisten Fällen können die Zusammenfassungen Screenshots enthalten, Videos sowie komplizierte Beschreibungen ausgezeichnete Funktionserweiterungen ansprechend und auch die Effizienz-Optimierungen. Jedoch bei Raten der Aktionen des betroffenen Internet-Browser verändern werden- Einzelpersonen werden sicherlich feststellen, dass sie mit Sicherheit umgeleitet wird, um einen Hacker-gesteuerte Landung Webseite und auch geändert werden, um ihre Setups könnte – die Standard-Startseite, Suchmaschine und neue Registerkarten Webseite.

XmrigDaemon.exe: Analyse
Die Malware XmrigDaemon.exe ist eine klassische Situation eines Cryptocurrency Miner, die je nach Anordnung eine Vielzahl unsicherer Aktivitäten verursachen kann. Das Hauptziel besteht darin, komplizierte mathematische Aufgaben auszuführen, bei denen die leicht verfügbaren Systemressourcen sicherlich genutzt werden: Zentralprozessor, GPU, Speicher- und auch Festplattenbereich. Die Methode, mit der sie arbeiten, besteht darin, eine Verbindung zu einem eindeutigen Server namens Mining Pool herzustellen, von dem der angeforderte Code heruntergeladen und installiert wird. So schnell, wie bei den Aufgaben heruntergeladen wird, wird es auf einmal begonnen, mehrere Instanzen können für einmal verschwunden sein. Wenn ein bestimmter Auftrag abgeschlossen ist, wird ein weiterer an seinem Speicherort heruntergeladen, und die Schleife wird fortgesetzt, bis das Computersystem ausgeschaltet wird, die Infektion entfernt wird oder ein zusätzliches vergleichbares Ereignis eintritt. Kryptowährung wird sicherlich zu den kriminellen Controller belohnt (Hacker-Gruppe oder ein einsames cyber) direkt an ihren Geldbeutel.
Eine schädliche Eigenschaft dieser Klassifizierung von Malware ist, dass Beispiele wie dieses alle Systemquellen nutzen und das Computersystem des Opfers praktisch unbrauchbar machen können, bis die Bedrohung vollständig beseitigt ist. Viele von ihnen verfügen über eine konsistente Installation, die es wirklich schwierig macht, sie zu entfernen. Diese Befehle werden sicherlich Änderungen vornehmen Entscheidungen zu booten, Konfigurationsdaten sowie Windows-Registrierungswerte, mit denen die Malware XmrigDaemon.exe automatisch gestartet wird, sobald das Computersystem eingeschaltet wird. Der Zugang zur Auswahl und Auswahl von Heilnahrungsmitteln kann blockiert sein, was viele handbetätigte Eliminierungshilfen nahezu unwirksam macht.
Diese spezifische Infektion wird sicherlich Anordnung eine Windows-Lösung für sich, Bei Einhaltung der durchgeführten Sicherheitsanalyse wurden folgende Maßnahmen beobachtet:
. Während der miner Verfahren kann die zugehörige Malware Haken bis zu bereits Windows-Lösungen laufen und auch von Drittanbietern installierten Anwendungen. Auf diese Weise sehen die Systemadministratoren möglicherweise nicht, dass die Quelllast von einem anderen Verfahren stammt.
| Name | XmrigDaemon.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware um XmrigDaemon.exe zu erkennen und zu entfernen |

Diese Art von Malware-Infektionen führt besonders effizient innovative Befehle aus, wenn sie so eingerichtet sind. Sie basieren auf einem modularen Aufbau, der es den kriminellen Kontrolleuren ermöglicht, alle Arten gefährlicher Gewohnheiten zu verwalten. Zu den beliebten Fällen ist die Änderung der Windows-Registrierung – Mit dem Betriebssystem verknüpfte Änderungszeichenfolgen können schwerwiegende Effizienzstörungen und die Unzugänglichkeit von Windows-Diensten verursachen. Abhängig vom Umfang der Änderungen kann das Computersystem zusätzlich völlig unbrauchbar werden. Auf der anderen Seite können Manipulationen an Registrierungswerten, die von Anwendungen von Drittanbietern stammen, diese sabotieren. Einige Anwendungen können kurze fallen ganz zu starten, während andere plötzlich stoppen arbeiten.
Dieser spezielle Miner in seiner aktuellen Version konzentriert sich auf das Extrahieren der Monero-Kryptowährung, einschließlich einer geänderten Variante der XMRig-CPU-Mining-Engine. Wenn die Kampagnen danach erfolgreich sind, können zukünftige Versionen von XmrigDaemon.exe in Zukunft gestartet werden. Da die Malware nutzt Software susceptabilities Ziel-Hosts verunreinigen, es kann mit Ransomware-Komponente eines gefährlichen Koinfektion und Trojanern auch.
Die Eliminierung von XmrigDaemon.exe wird dringend empfohlen, Bedenken Sie, dass Sie nicht nur hohe elektrische Energiekosten riskieren, wenn diese auf Ihrem PC ausgeführt werden, Der Bergmann kann jedoch auch verschiedene andere unerwünschte Aktivitäten ausführen und Ihren COMPUTER dauerhaft beschädigen.
Entfernungsprozess von XmrigDaemon.exe
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” Schaltfläche zum Entfernen von XmrigDaemon.exe
SCHRITT 5. XmrigDaemon.exe entfernt!
Video Guide: Verwendung von GridinSoft Anti-Malware zum Entfernen von XmrigDaemon.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “XmrigDaemon.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “XmrigDaemon.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “XmrigDaemon.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “XmrigDaemon.exe”.







