Ein neuer, extrem schädlich Kryptowährung miner Infektion wurde tatsächlich von Sicherheit Forscher fanden heraus,. die Malware, namens Service64.exe kann eine Vielzahl von Methoden Ziel Erkrankten kontaminieren Verwendung. Die Grundidee hinter dem Service64.exe Bergmann ist zu Kryptowährung miner Aktivitäten auf den Rechnern der Opfer, um Monero Symbole auf Ziele Ausgaben zu nutzen zu erhalten. Das Ergebnis dieses Bergmanns sind die erhöhten Stromkosten. Wenn Sie ihn für längere Zeit verlassen, kann Service64.exe sogar die Elemente Ihres Computers beschädigen.
Service64.exe: Verteilungsmethoden
Das Service64.exe Malware verwendet zwei bekannte Techniken, mit denen Computersystemziele kontaminiert werden:
- Payload Lieferung mit Vor-Infektionen. Wenn eine ältere Service64.exe-Malware auf den Opfersystemen bereitgestellt wird, kann sie sich sofort selbst aktualisieren oder eine neuere Variante herunterladen. Dies ist mit dem integrierten Update-Befehl möglich, mit dem die Version abgerufen wird. Dies wird durch das Anbringen an einen bestimmten vordefinierten Hacker gesteuerte-Server durchgeführt, die den Malware-Code liefert. Die heruntergeladene Infektion erhält mit Sicherheit den Namen eines Windows-Dienstes und wird in der Position positioniert “%System% temp” Bereich. Wichtige Häuser und auch laufende Systemkonfigurationsdokumente werden transformiert, um eine unerbittliche und stille Infektion zu ermöglichen.
- Software Application Vulnerability Exploits. Die neueste Version der Service64.exe-Malware wurde gefunden, um durch einige Exploits ausgelöst zu werden, weithin bekannt für in der Ransomware-Attacken verwendet werden. Die Infektionen werden durch Targeting offene Lösungen mit Hilfe des TCP-Port erfolgen. Die Streiks werden von einem Hacker gesteuerte Struktur automatisiert die oben schaut, ob der Port offen ist. Wenn diese Bedingung erfüllt ist, wird die Lösung mit Sicherheit überprüft und auch Informationen dazu abgerufen, einschließlich aller Variations- und Einrichtungsinformationen. Ventures sowie bevorzugte Kombinationen aus Benutzername und Passwort können durchgeführt werden. Wenn der Exploit im Vergleich zum anfälligen Code verursacht wird, wird der Miner mit Sicherheit zusammen mit der Hintertür freigegeben. Diese präsentiert sicherlich die eine Doppelinfektion.
Zusätzlich zu diesen Ansätzen können auch verschiedene andere Verfahren verwendet werden. Bergleute können durch Phishing-E-Mails aufgelöst werden, die in großen Mengen auf SPAM-ähnliche Weise versendet werden und von Methoden des sozialen Designs abhängen, um die Ziele zu verwirren und zu glauben, dass sie eine Nachricht von einer seriösen Lösung oder Firma erhalten haben. Die Virendokumente können entweder direkt angehängt oder in Multimedia-Inhalten oder Text-Weblinks in das Körpermaterial eingefügt werden.
Die Kriminellen können zusätzlich zerstörerische Touchdown-Seiten erstellen, die sich als Download-Webseiten von Lieferanten ausgeben können, Software-Download-Sites sowie verschiedene andere regelmäßig zugegriffen Standorte. Wenn sie vergleichbar erscheinende Domain-Namen mit legitimen Adressen sowie Sicherheitszertifikaten verwenden, können die Benutzer davon überzeugt werden, sich direkt mit ihnen zu verbinden. In einigen Fällen öffnen sie einfach die Bergmann-Infektion verursachen.
Eine zusätzliche Technik wäre sicherlich die Verwendung von Transportunternehmen, die unter Verwendung dieser Methoden oder mittels Datenaustauschnetzwerken verbreitet werden können, BitTorrent ist nur eine der am meisten bevorzugt diejenigen,. Es wird häufig verwendet, um sowohl echte Software und Dokumente als auch Pirateninhalte zu verbreiten. Zwei der beliebtesten Nutzlastanbieter sind die folgenden:
Andere Techniken, die von den Übeltätern in Betracht gezogen werden können, bestehen darin, Browser-Hijacker zu verwenden - gefährliche Plugins, die für einen der beliebtesten Internetbrowser geeignet sind. Sie werden mit falschen Benutzerreferenzen und Entwickleranmeldeinformationen in die entsprechenden Datenbanken hochgeladen. Oft könnten die Beschreibungen enthalten Screenshots, Videoclips und ausführliche Beschreibungen fördern großartige Attributverbesserungen und auch Effizienzoptimierungen. Bei der Ratenzahlung ändert sich jedoch das Verhalten der betroffenen Webbrowser- Einzelpersonen werden sicherlich feststellen, dass sie auf eine von Hackern kontrollierte Zielseite umgeleitet werden und ihre Einstellungen möglicherweise geändert werden – die Standard-Webseite, Online-Suchmaschine und neue Registerkarten Seite.

Service64.exe: Analyse
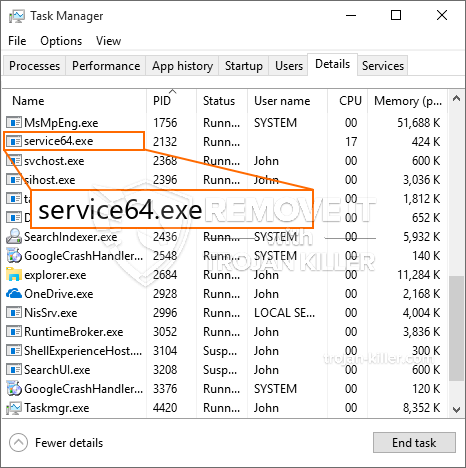
Die Malware Service64.exe ist eine zeitlose Instanz eines Cryptocurrency Miner, deren Abhängigkeit von seiner Konfiguration eine Vielzahl gefährlicher Aktionen verursachen kann. Das Hauptziel besteht darin, komplizierte mathematische Aufgaben auszuführen, die von den leicht verfügbaren Systemquellen profitieren: Zentralprozessor, GPU, Speicher- und auch Festplattenspeicher. Die Methode, mit der sie funktionieren, besteht darin, eine Verbindung zu einem speziellen Webserver namens Mining Pool herzustellen, von dem der erforderliche Code heruntergeladen wird. So schnell, wie bei den Arbeitsplätzen heruntergeladen wird es gleichzeitig wird damit begonnen,, zahlreiche Fälle können so bald verschwunden sein als. Wenn eine angebotene Aufgabe abgeschlossen ist, wird sicherlich eine andere an ihrem Speicherort heruntergeladen, und die Lücke bleibt bestehen, bis das Computersystem ausgeschaltet wird, Die Infektion wird entfernt oder eine andere vergleichbare Gelegenheit tritt auf. Kryptowährung wird sicherlich zu den kriminellen Controller kompensiert werden (Hacker-Gruppe oder ein einsames cyber) gerade auf ihren Geldbeutel.
Ein schädliches Attribut dieser Gruppe von Malware ist, dass ähnliche Beispiele alle Systemquellen nutzen und das Zielcomputersystem praktisch sinnlos machen können, bis die Bedrohung tatsächlich vollständig beseitigt ist. Viele von ihnen enthalten eine unerbittliche Installation, die es wirklich schwierig macht, sie zu entfernen. Diese Befehle werden Anpassungen vornehmen Optionen zu booten, Setup-Daten und Windows-Registrierungswerte, mit denen die Malware "Service64.exe" automatisch gestartet wird, wenn das Computersystem eingeschaltet wird. Der Zugang zur Auswahl von Wiederherstellungsnahrungsmitteln und auch zu Alternativen kann behindert sein, was zahlreiche praktische Anleitungen zum Entfernen praktisch unbrauchbar macht.
Diese spezifische Infektion Konfiguration Windows-Dienst für sich selbst, Nach der durchgeführten Schutzbewertung wurden folgende Maßnahmen beobachtet:
. Während der Miner-Prozeduren kann die verbundene Malware eine Verknüpfung zu bereits ausgeführten Windows-Lösungen und installierten Anwendungen von Drittanbietern herstellen. Auf diese Weise stellen die Systemmanager möglicherweise nicht fest, dass die Quelltonnen aus einem anderen Verfahren stammen.
| Name | Service64.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware um Service64.exe zu erkennen und zu entfernen |

Diese Art von Malware-Infektionen führt besonders effizient erweiterte Befehle aus, wenn sie so konfiguriert sind. Sie basieren auf einem modularen Aufbau, der es den kriminellen Kontrolleuren ermöglicht, alle Arten von unsicheren Gewohnheiten zu orchestrieren. Eines der bekanntesten Beispiele ist die Einstellung der Windows-Registrierung – Anpassungszeichenfolgen, die sich auf das Betriebssystem beziehen, können zu erheblichen Leistungsunterbrechungen sowie zur Unfähigkeit führen, auf Windows-Dienste zuzugreifen. Wenn man sich auf die Modifikationen stützt, kann das Computersystem zusätzlich völlig unbrauchbar werden. Auf der anderen Seite können Anpassungen der Registrierungswerte, die zu einer beliebigen Art von installierten Anwendungen von Drittanbietern gehören, diese sabotieren. Einige Anwendungen funktionieren möglicherweise nicht mehr vollständig, während andere plötzlich nicht mehr funktionieren.
Dieser spezielle Miner in seiner vorhandenen Version konzentriert sich auf das Extrahieren der Monero-Kryptowährung, die aus einer geänderten Version der XMRig-CPU-Mining-Engine besteht. Wenn sich die Projekte danach als erfolgreich erweisen, können zukünftige Variationen von Service64.exe in der Zukunft veröffentlicht werden. Da die Malware nutzt Software-Anwendung susceptabilities Ziel-Hosts verunreinigen, es kann mit Ransomware-Komponente eines unsicheren Koinfektion und Trojanern auch.
Die Eliminierung von Service64.exe wird dringend empfohlen, da Sie das Risiko haben, nicht nur hohe Stromkosten zu verursachen, wenn es auf Ihrem COMPUTER läuft, Der Bergmann kann jedoch zusätzlich andere unerwünschte Aufgaben ausführen und Ihren COMPUTER vollständig beschädigen.
Entfernungsprozess für Service64.exe
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” Schaltfläche zum Entfernen von Service64.exe
SCHRITT 5. Service64.exe entfernt!
Video Guide: Verwendung von GridinSoft Anti-Malware zum Entfernen von Service64.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Service64.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Service64.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Service64.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Service64.exe”.







