Ein neuer, Sicherheitsforscher haben eine wirklich schädliche Cryptocurrency Miner-Infektion identifiziert. die Malware, namens Brhost.exe kann Zielopfer mit einer Vielzahl von Methoden infizieren. Die Essenz hinter dem Brhost.exe-Miner besteht darin, Cryptocurrency-Miner-Aufgaben auf den Computern der Opfer einzusetzen, um Monero-Symbole auf Kosten der Opfer zu erhalten. Brhost.exe.
Brhost.exe: Verteilungsmethoden
Das Brhost.exe Malware nutzt 2 Brhost.exe:
- Payload Lieferung über Vor-Infektionen. Brhost.exe. Brhost.exe. Dies wird durch die Verbindung zu einem bestimmten vordefinierten Hacker gesteuerte Server durchgeführt, die den Malware-Code liefert. Das heruntergeladene Virus wird sicherlich den Namen einer Windows-Lösung erhalten und in der positioniert werden “%System% temp” Bereich. Brhost.exe.
- Software-Programm Ausnutzen von Sicherheitslücken. Es wurde tatsächlich festgestellt, dass die neueste Variante der Brhost.exe-Malware durch einige Exploits verursacht wurde, berühmt anerkannt in der Ransomware-Attacken genutzt wird. Die Infektionen werden durch Targeting offene Dienste über den TCP-Port erfolgen. Die Angriffe werden von einem Hacker-kontrollierten Rahmen automatisiert die oben schaut, ob der Port offen ist. Es wurde tatsächlich festgestellt, dass die neueste Variante der Brhost.exe-Malware durch einige Exploits verursacht wurde, bestehend aus irgendeiner Variation und Konfigurationsinformationen. Ventures und beliebte Benutzernamen sowie Passwort Mixes getan werden könnte. Es wurde tatsächlich festgestellt, dass die neueste Variante der Brhost.exe-Malware durch einige Exploits verursacht wurde. Dies bietet sicherlich die eine doppelte Infektion.
Es wurde tatsächlich festgestellt, dass die neueste Variante der Brhost.exe-Malware durch einige Exploits verursacht wurde. Es wurde tatsächlich festgestellt, dass die neueste Variante der Brhost.exe-Malware durch einige Exploits verursacht wurde. Die Infektionsdaten können entweder direkt verbunden oder in die Körperteile in Multimedia-Inhalte oder Nachrichten-Weblinks eingefügt werden.
Die Infektionsdaten können entweder direkt verbunden oder in die Körperteile in Multimedia-Inhalte oder Nachrichten-Weblinks eingefügt werden, Die Infektionsdaten können entweder direkt verbunden oder in die Körperteile in Multimedia-Inhalte oder Nachrichten-Weblinks eingefügt werden. Die Infektionsdaten können entweder direkt verbunden oder in die Körperteile in Multimedia-Inhalte oder Nachrichten-Weblinks eingefügt werden. Manchmal öffnen sie einfach die Bergmann-Infektion aktivieren.
Die Infektionsdaten können entweder direkt verbunden oder in die Körperteile in Multimedia-Inhalte oder Nachrichten-Weblinks eingefügt werden, BitTorrent ist ein von einem der am meisten bevorzugt denjenigen,. Die Infektionsdaten können entweder direkt verbunden oder in die Körperteile in Multimedia-Inhalte oder Nachrichten-Weblinks eingefügt werden. 2 der beliebtesten Nutzlast-Anbieter sind die folgenden:
Die Cyberpunks können Manuskripte installieren, die den Malware-Code Brhost.exe so schnell einbinden, wie sie gestartet werden. Sie werden mit gefälschten Benutzerbewertungen und auch Entwicklerqualifikationen in den einschlägigen Repositories veröffentlicht. Oft könnten die Beschreibungen enthalten Screenshots, Sie werden mit gefälschten Benutzerbewertungen und auch Entwicklerqualifikationen in den einschlägigen Repositories veröffentlicht. Sie werden mit gefälschten Benutzerbewertungen und auch Entwicklerqualifikationen in den einschlägigen Repositories veröffentlicht- Sie werden mit gefälschten Benutzerbewertungen und auch Entwicklerqualifikationen in den einschlägigen Repositories veröffentlicht – die Standard-Startseite, Internet-Suchmaschine und auch brandneue Registerkarten Seite.

Brhost.exe: Analyse
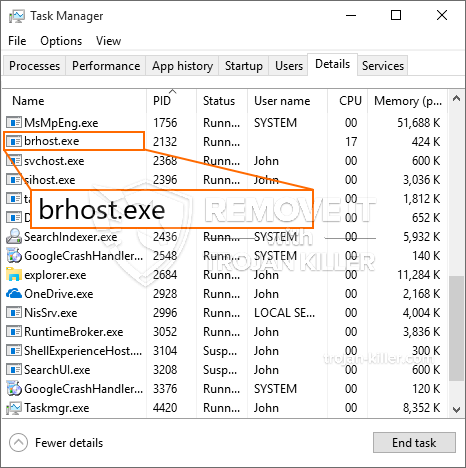
Sie werden mit gefälschten Benutzerbewertungen und auch Entwicklerqualifikationen in den einschlägigen Repositories veröffentlicht. Sie werden mit gefälschten Benutzerbewertungen und auch Entwicklerqualifikationen in den einschlägigen Repositories veröffentlicht: Zentralprozessor, GPU, Speicher und Festplatte auch Raum. Das Mittel, das sie betreiben, besteht darin, sich an einen einzigartigen Webserver namens Mining Pool anzuschließen, von dem der erforderliche Code heruntergeladen wird. Sobald eine der Aufgaben heruntergeladen ist, wird sie gleichzeitig gestartet, Es können mehrere Instanzen ausgeführt werden, sobald. Wenn eine bereitgestellte Aufgabe abgeschlossen ist, wird sicherlich eine weitere heruntergeladen und an ihrem Ort installiert, und die Schleife wird fortgesetzt, bis das Computersystem ausgeschaltet wird, die Infektion beseitigt wird oder ein weiterer vergleichbarer Anlass eintritt. Kryptowährung wird sicherlich zu den kriminellen Controller kompensiert werden (Hacker-Gruppe oder ein einsamer Hacker) gerade in ihre Geldbörsen.
Eine unsichere Eigenschaft dieser Gruppe von Malware ist, dass Proben wie diese alle Systemquellen nehmen und das Zielcomputersystem praktisch unbrauchbar machen können, bis die Bedrohung vollständig beseitigt ist. Die meisten von ihnen verfügen über eine konsistente Installation, die es wirklich schwierig macht, sie loszuwerden. Diese Befehle werden Anpassungen vornehmen Optionen zu booten, Konfigurationsdateien sowie Windows-Registrierungswerte, die die Malware Brhost.exe automatisch starten lassen, sobald der Computer eingeschaltet wird. Konfigurationsdateien sowie Windows-Registrierungswerte, die die Malware Brhost.exe automatisch starten lassen, sobald der Computer eingeschaltet wird.
Diese besondere Infektion Anordnung ein Windows-Dienst für sich, Konfigurationsdateien sowie Windows-Registrierungswerte, die die Malware Brhost.exe automatisch starten lassen, sobald der Computer eingeschaltet wird:
. Es ermöglicht den kriminellen Kontrolleuren, sich bei der Lösung anzumelden und auch alle entführten Informationen abzurufen. Es ermöglicht den kriminellen Kontrolleuren, sich bei der Lösung anzumelden und auch alle entführten Informationen abzurufen.
| Name | Brhost.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware Es ermöglicht den kriminellen Kontrolleuren, sich bei der Lösung anzumelden und auch alle entführten Informationen abzurufen |

Es ermöglicht den kriminellen Kontrolleuren, sich bei der Lösung anzumelden und auch alle entführten Informationen abzurufen. Sie basieren auf einem modularen Rahmenwerk, das es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Aktionen zu orchestrieren. Unter den prominenten Fällen ist die Änderung der Windows-Registrierung – Sie basieren auf einem modularen Rahmenwerk, das es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Aktionen zu orchestrieren. Sie basieren auf einem modularen Rahmenwerk, das es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Aktionen zu orchestrieren. Sie basieren auf einem modularen Rahmenwerk, das es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Aktionen zu orchestrieren. Sie basieren auf einem modularen Rahmenwerk, das es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Aktionen zu orchestrieren.
Sie basieren auf einem modularen Rahmenwerk, das es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Aktionen zu orchestrieren. Wenn sich die Kampagnen danach als wirksam erweisen, können zukünftige Variationen der Brhost.exe in der Zukunft gestartet werden. Da die Malware Verwendung von Software-Programm macht susceptabilities Ziel-Hosts zu infizieren, es kann Teil eines gefährlichen Koinfektion mit Ransomware sowie Trojaner sein.
Wenn sich die Kampagnen danach als wirksam erweisen, können zukünftige Variationen der Brhost.exe in der Zukunft gestartet werden, Wenn sich die Kampagnen danach als wirksam erweisen, können zukünftige Variationen der Brhost.exe in der Zukunft gestartet werden, Wenn sich die Kampagnen danach als wirksam erweisen, können zukünftige Variationen der Brhost.exe in der Zukunft gestartet werden.
Brhost.exe
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” Brhost.exe
SCHRITT 5. Brhost.exe!
Video Guide: Brhost.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Brhost.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Brhost.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Brhost.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Brhost.exe”.







