En ny, meget usikker cryptocurrency minearbejder virus er blevet spottet af sikkerhedseksperter. den malware, hedder WUDHostServices.exe kan inficere målgrupper ved hjælp af en række forskellige metoder. Essensen bag WUDHostServices.exe-minearbejderen er at anvende cryptocurrency-mineropgaver på syges computersystemer for at få Monero-symboler til målpris. The end result of this miner is the elevated electrical energy bills and if you leave it for longer amount of times WUDHostServices.exe might even damage your computer systems components.
WUDHostServices.exe: distributionssystemer Metoder
Det WUDHostServices.exe malware udnytter 2 fremtrædende tilgange, der bruges til at forurene computermål:
- Payload Levering via Prior Infektioner. If an older WUDHostServices.exe malware is deployed on the victim systems it can immediately upgrade itself or download a newer variation. Dette er muligt ved hjælp af den integrerede opdatering kommando, som erhverver lanceringen. Dette gøres ved at binde sig til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. The downloaded and install virus will certainly obtain the name of a Windows solution and be placed in the “%systemet% temp” placere. Vital homes as well as operating system arrangement data are altered in order to allow a persistent and quiet infection.
- Software sårbarhed udnytter. The most recent version of the WUDHostServices.exe malware have actually been located to be triggered by the some exploits, bredt forstået for at blive udnyttet i de ransomware angreb. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. If this condition is fulfilled it will certainly check the service as well as recover details concerning it, including any version and configuration information. Exploits and prominent username and password mixes might be done. When the make use of is set off against the at risk code the miner will certainly be deployed in addition to the backdoor. Dette vil helt sikkert give det en dobbelt infektion.
Ud over disse teknikker andre tilgange kan gøres brug af for. Miners can be distributed by phishing emails that are sent out in bulk in a SPAM-like way and depend on social design tricks in order to puzzle the targets into thinking that they have actually gotten a message from a reputable solution or firm. The infection data can be either straight connected or placed in the body materials in multimedia content or text links.
The crooks can also create harmful landing web pages that can impersonate supplier download pages, software program download sites as well as other regularly accessed areas. When they use similar seeming domain to legitimate addresses and safety certifications the users may be coerced right into interacting with them. Nogle gange blot åbne dem kan aktivere minearbejder infektion.
An additional approach would certainly be to use haul carriers that can be spread out making use of the above-mentioned approaches or using documents sharing networks, BitTorrent er en af en af de mest foretrukne dem. It is frequently made use of to distribute both legitimate software as well as documents and also pirate material. 2 af en af de mest populære nyttelast udbydere er følgende:
Various other approaches that can be thought about by the offenders include the use of web browser hijackers -dangerous plugins which are made suitable with one of the most popular web browsers. They are uploaded to the relevant databases with phony customer evaluations and also programmer credentials. In many cases the summaries may consist of screenshots, video clips and sophisticated summaries promising fantastic attribute improvements and efficiency optimizations. Nonetheless upon installment the behavior of the affected web browsers will alter- customers will discover that they will certainly be redirected to a hacker-controlled landing page and their settings might be altered – standard webside, online søgemaskine og nye faner webside.
WUDHostServices.exe: Analyse
The WUDHostServices.exe malware is a classic case of a cryptocurrency miner which depending upon its configuration can cause a wide array of hazardous activities. Dets primære mål er at udføre indviklede matematiske job, der får mest ud af de tilbudte systemkilder: CPU, GPU, hukommelse og også harddiskplads. De midler, de fungerer, er ved at linke til en speciel webserver kaldet minedrift, hvor den kaldte kode downloades. Så snart en af opgaverne er downloadet, startes den på samme tid, adskillige tilfælde kan køres på når. Når en tilbudt opgave er afsluttet, bliver en mere downloadet og installeret i stedet, og smuthullet vil helt sikkert fortsætte, indtil computersystemet er slukket, infektionen er fjernet eller en anden lignende lejlighed finder sted. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking gruppe eller en enkelt hacker) direkte til deres budgetter.
Et usikkert træk ved denne klassificering af malware er, at prøver, der ligner denne, kan tage alle systemkilder og også praktisk talt gøre offerets computersystem meningsløst, indtil faren faktisk er helt elimineret. De fleste af dem inkluderer en vedvarende rate, der gør dem virkelig svære at slippe af med. Disse kommandoer vil bestemt også ændre indstillingerne, setup files as well as Windows Registry values that will make the WUDHostServices.exe malware beginning instantly when the computer system is powered on. Adgang til helbredende menuer og også muligheder kan blive blokeret, hvilket gør adskillige manuelle fjernelsesoversigter næsten ubrugelige.
Denne specifikke infektion vil helt sikkert konfigurationshåndtering en Windows-tjeneste for sig selv, overholdelse af den udførte sikkerhedsanalyse, hvor følgende aktiviteter faktisk er blevet observeret:
. Under minearbejdere kan den tilsluttede malware vedhæfte til aktuelt kørende Windows-løsninger og installerede applikationer fra tredjepart. Ved at gøre det ser systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en anden proces.
| Navn | WUDHostServices.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove WUDHostServices.exe |
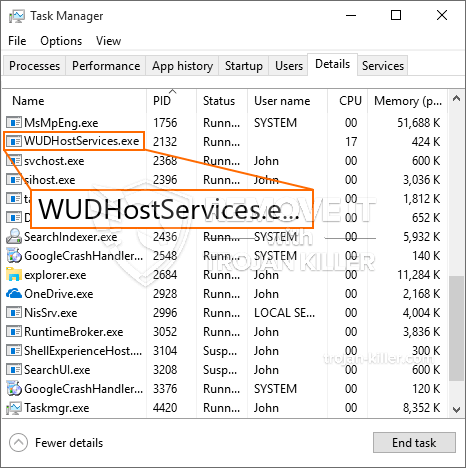
id =”82697″ align =”aligncenter” width =”600″]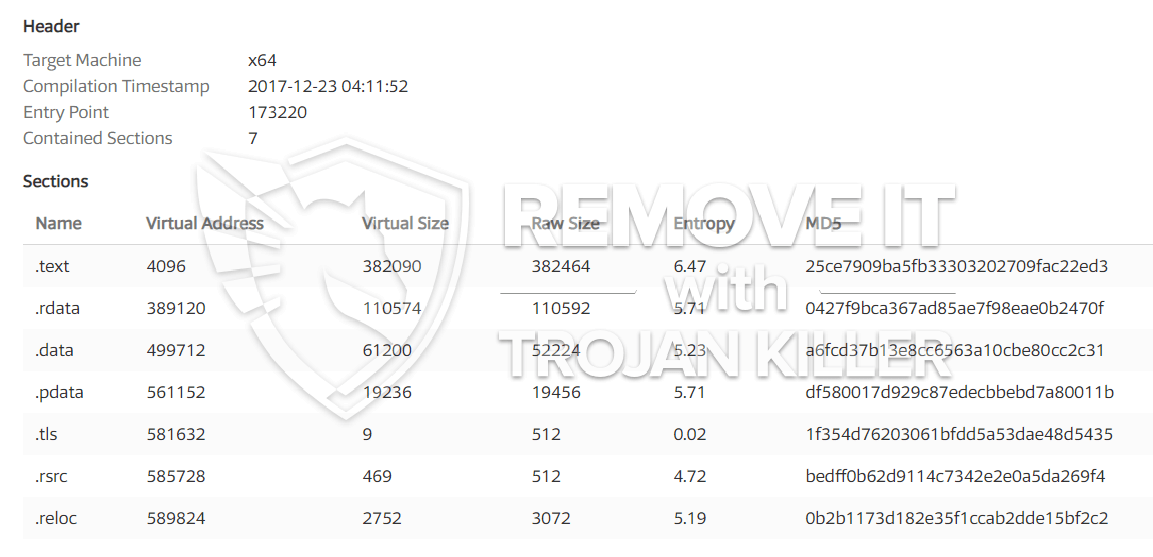 WUDHostServices.exe
WUDHostServices.exe
Disse typer af malware-infektioner er specifikt effektive til at udføre avancerede kommandoer, hvis de er konfigureret således. They are based on a modular framework permitting the criminal controllers to orchestrate all type of unsafe actions. Blandt de foretrukne eksempler er justeringen af registreringsdatabasen i Windows – modifications strings connected by the operating system can cause major efficiency interruptions as well as the lack of ability to accessibility Windows services. Depending upon the extent of adjustments it can also make the computer system completely pointless. On the various other hand control of Registry values coming from any third-party set up applications can sabotage them. Nogle applikationer holder muligvis op med at fungere for at starte helt, mens andre pludselig kan holde op med at arbejde.
This particular miner in its existing variation is focused on mining the Monero cryptocurrency consisting of a changed variation of XMRig CPU mining engine. If the projects verify effective then future versions of the WUDHostServices.exe can be introduced in the future. Da malware bruger software program susceptabilities at inficere target værter, det kan være del af en farlig co-infektion med ransomware og trojanske heste.
Elimination of WUDHostServices.exe is highly advised, given that you take the chance of not only a big electrical energy bill if it is working on your COMPUTER, yet the miner might also perform other unwanted tasks on it and also damage your PC permanently.
WUDHostServices.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove WUDHostServices.exe
TRIN 5. WUDHostServices.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove WUDHostServices.exe
Hvordan undgår din pc fra at blive inficeret med “WUDHostServices.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “WUDHostServices.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “WUDHostServices.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “WUDHostServices.exe”.