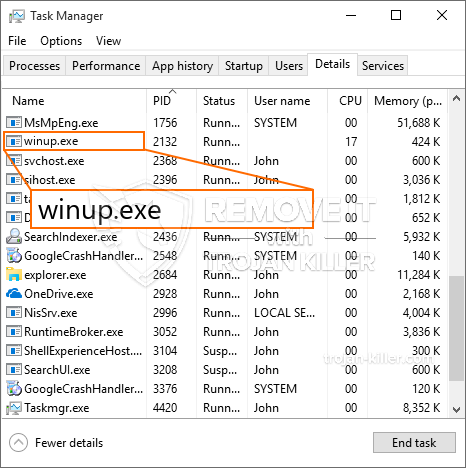
En ny, virkelig farligt cryptocurrency minearbejder infektion rent faktisk er blevet identificeret af sikkerhedseksperter. den malware, hedder Winup.exe kan inficere ofre mål udnytte et udvalg af måder. Essensen bag Winup.exe-miner er at ansætte cryptocurrency-mineraktiviteter på ofrenes computere for at få Monero-tokens til ofre. The result of this miner is the raised electrical power expenses and also if you leave it for longer periods of time Winup.exe might even damage your computer systems parts.
Winup.exe: distributionssystemer Metoder
Det Winup.exe malware gør brug af 2 preferred techniques which are used to contaminate computer targets:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older Winup.exe malware is deployed on the victim systems it can instantly update itself or download a newer variation. Dette er muligt ved hjælp af den integrerede opdatering kommando, som erhverver udgivelsen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. The downloaded and install infection will acquire the name of a Windows solution and also be positioned in the “%Systemet% temp” placere. Essential homes and running system configuration data are transformed in order to allow a relentless and silent infection.
- Software sårbarhed udnytter. The most recent version of the Winup.exe malware have actually been located to be triggered by the some exploits, populært forstået for at blive brugt i ransomware-strejker. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Strejkerne er automatiseret af en hacker-kontrollerede rammer, som ser op, hvis porten er åben. If this condition is met it will certainly scan the solution and get details concerning it, consisting of any type of variation as well as arrangement information. Ventures and also popular username as well as password mixes might be done. When the manipulate is activated against the at risk code the miner will certainly be deployed in addition to the backdoor. Dette vil danne en dobbelt infektion.
In addition to these techniques various other approaches can be used as well. Miners can be dispersed by phishing e-mails that are sent out in bulk in a SPAM-like way as well as rely on social engineering techniques in order to puzzle the targets right into believing that they have received a message from a reputable service or company. The infection documents can be either directly affixed or inserted in the body materials in multimedia web content or text links.
The lawbreakers can also create harmful touchdown pages that can impersonate supplier download and install pages, software application download portals as well as other regularly accessed places. When they utilize similar sounding domain names to legit addresses as well as safety and security certificates the customers may be pushed right into connecting with them. I mange tilfælde bare åbne dem kan modregne minearbejder infektion.
An additional approach would certainly be to utilize payload providers that can be spread using the above-mentioned approaches or via file sharing networks, BitTorrent er en af de mest populære dem. It is often utilized to distribute both legitimate software and also data as well as pirate web content. To af de mest fremtrædende nyttelast tjenesteydere er følgende:
Various other approaches that can be thought about by the wrongdoers include the use of internet browser hijackers -dangerous plugins which are made suitable with the most preferred web browsers. They are published to the pertinent databases with phony customer evaluations as well as developer credentials. I de fleste tilfælde beskrivelserne kan omfatte skærmbilleder, video clips and also fancy summaries promising great function improvements and also efficiency optimizations. Nonetheless upon setup the actions of the impacted internet browsers will certainly transform- users will locate that they will be redirected to a hacker-controlled touchdown page and also their setups may be changed – standard startside, søgemaskine og også nye faner webside.

Winup.exe: Analyse
The Winup.exe malware is a traditional situation of a cryptocurrency miner which relying on its configuration can trigger a wide array of unsafe activities. Hovedformålet er at gøre komplekse matematiske opgaver, der vil drage fordel af de tilgængelige systemkilder: CPU, GPU, hukommelse samt plads på harddisken. Metoden de fungerer, er ved at binde sig til en unik server kaldet minedrift swimmingpool, hvor den opfordrede til koden er downloadet. Så hurtigt som blandt opgaverne bliver downloadet det vil blive påbegyndt på en gang, talrige eksempler kan køre på, så snart. Når en forudsat job er udført yderligere en vil helt sikkert blive hentet på sin plads, og også løkken fortsætter indtil computeren systemet er slukket, infektionen elimineres eller en tilsvarende begivenhed finder sted. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres tegnebøger.
En farlig egenskab ved denne gruppe af malware er, at eksemplerne ligner denne kan tage alle system ressourcer og næsten gøre målet computersystem ubrugelig indtil truslen er blevet totalt elimineret. De fleste af dem omfatter en sammenhængende installation, der gør dem virkelig svært at slippe af med. Disse kommandoer vil foretage justeringer af opstartsmuligheder, configuration data and Windows Registry values that will make the Winup.exe malware beginning instantly once the computer system is powered on. Adgang til nyttiggørelse menuer og valgmuligheder kan blive blokeret som gør mange manuelle eliminering oversigter næsten meningsløse.
Denne vis infektion vil helt sikkert sætte en Windows-løsning for sig selv, overholde den gennemførte sikkerhedsanalyse ther overholde aktiviteter rent faktisk er blevet observeret:
. I løbet af minearbejder procedurer den tilhørende malware kan tilslutte op til allerede kører Windows-tjenester samt tredjepart oprettet applikationer. Ved at gøre dette systemadministratorer kan ikke opdage, at kilden masser kommer fra en særskilt procedure.
| Navn | Winup.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Winup.exe |

These sort of malware infections are specifically reliable at performing advanced commands if set up so. They are based on a modular framework permitting the criminal controllers to manage all type of hazardous behavior. Blandt de fremtrædende eksempler er justeringen af registreringsdatabasen i Windows – modifications strings related by the operating system can cause significant performance disruptions and also the failure to accessibility Windows solutions. Depending upon the extent of adjustments it can likewise make the computer system totally pointless. On the other hand control of Registry worths belonging to any third-party installed applications can undermine them. Some applications might stop working to introduce entirely while others can all of a sudden stop working.
This specific miner in its existing variation is concentrated on extracting the Monero cryptocurrency consisting of a changed variation of XMRig CPU mining engine. If the campaigns confirm successful after that future variations of the Winup.exe can be introduced in the future. Da malware bruger softwarefølsomhed til at inficere målværter, det kan være en del af et farligt co-infektion med ransomware og trojanske heste.
Elimination of Winup.exe is highly suggested, because you run the risk of not just a large electrical energy expense if it is running on your PC, however the miner might additionally execute other undesirable tasks on it as well as also harm your PC permanently.
Winup.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Winup.exe
TRIN 5. Winup.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Winup.exe
Hvordan undgår din pc fra at blive inficeret med “Winup.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Winup.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Winup.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Winup.exe”.







