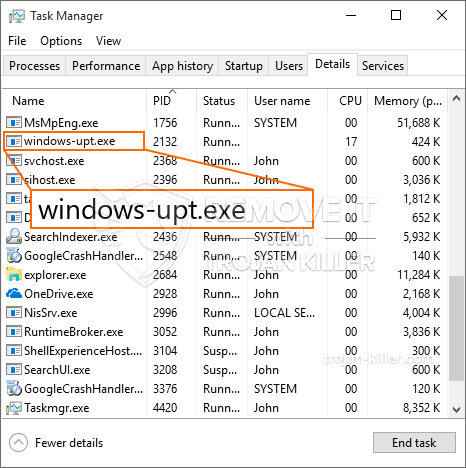
Et helt nyt, ekstremt farlig kryptovaluta-minearbejdervirus er blevet set af sikkerhedsforskere. den malware, hedder Windows-upt.exe kan forurene ofre mål ved hjælp af en række forskellige måder. Hovedpunktet bag Windows-upt.exe-minearbejderen er at anvende cryptocurrency-minearbejder på ofrenes computersystemer for at erhverve Monero-symboler til målpris. The result of this miner is the elevated electricity bills and if you leave it for longer amount of times Windows-upt.exe may also harm your computer systems elements.
Windows-upt.exe: distributionssystemer Metoder
Det Windows-upt.exe malware udnytter 2 preferred methods which are utilized to infect computer targets:
- Payload Levering gennem Prior Infektioner. If an older Windows-upt.exe malware is released on the victim systems it can instantly upgrade itself or download and install a newer version. Dette er muligt ved hjælp af den indbyggede opgraderingskommando, der får frigivelsen. This is done by linking to a specific predefined hacker-controlled server which provides the malware code. The downloaded and install infection will acquire the name of a Windows service and be put in the “%systemet% temp” areal. Vital residential properties and operating system configuration documents are changed in order to allow a relentless and also quiet infection.
- Software sårbarhed udnytter. The latest variation of the Windows-upt.exe malware have actually been found to be brought on by the some ventures, widely understood for being used in the ransomware attacks. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som ser op hvis porten er åben. If this condition is met it will certainly scan the solution as well as retrieve information regarding it, including any variation and arrangement information. Exploits and also prominent username and password combinations may be done. When the manipulate is activated versus the vulnerable code the miner will certainly be deployed along with the backdoor. Dette vil bestemt præsentere en dobbelt infektion.
Ud over disse metoder kan forskellige andre strategier også bruges. Miners can be distributed by phishing emails that are sent out in bulk in a SPAM-like way and depend upon social engineering methods in order to puzzle the victims into thinking that they have gotten a message from a legit service or company. The infection documents can be either directly affixed or placed in the body components in multimedia content or text web links.
The wrongdoers can likewise develop malicious touchdown pages that can pose vendor download and install pages, software application download sites and also other frequently accessed places. When they make use of comparable appearing domain to legit addresses and also safety and security certifications the users may be coerced right into interacting with them. Nogle gange kan blot åbning af dem forårsage minerinfektionen.
Another strategy would certainly be to make use of haul service providers that can be spread utilizing those approaches or through documents sharing networks, BitTorrent er blot en af de mest foretrukne dem. It is regularly used to disperse both genuine software program as well as documents and pirate material. 2 af de mest populære distancer tjenesteydere er følgende:
Various other methods that can be taken into consideration by the bad guys consist of the use of web browser hijackers -unsafe plugins which are made compatible with the most prominent web browsers. They are uploaded to the pertinent repositories with fake customer testimonials and developer credentials. I mange tilfælde resuméerne kan omfatte skærmbilleder, video clips as well as sophisticated descriptions promising terrific function improvements as well as performance optimizations. However upon installation the behavior of the affected web browsers will certainly alter- individuals will certainly discover that they will certainly be redirected to a hacker-controlled landing web page and their settings could be altered – standard startside, internetsøgemaskine samt splinterny faneblad side.
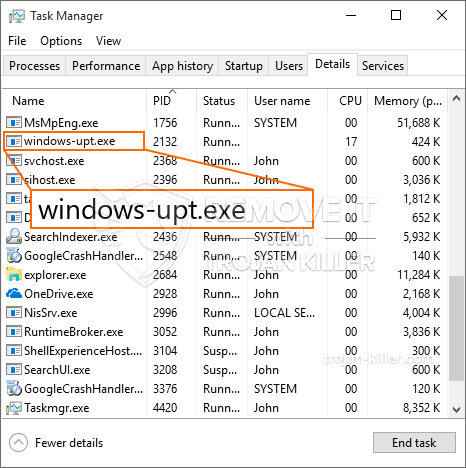
Windows-upt.exe: Analyse
The Windows-upt.exe malware is a traditional case of a cryptocurrency miner which relying on its arrangement can trigger a wide range of harmful activities. Dets hovedmål er at udføre komplicerede matematiske opgaver, der helt sikkert vil gøre brug af de let tilgængelige systemressourcer: CPU, GPU, hukommelse og harddiskplads. Midlerne, de arbejder på, er ved at knytte til en unik server kaldet mining pool, hvorfra den kaldte kode downloades. Så snart et af jobene er downloadet, startes det samtidig, adskillige tilfælde kan gå væk så snart. Når en given opgave er afsluttet, downloades en anden i sit område, og smuthullet fortsætter helt sikkert, indtil computersystemet er slukket, infektionen fjernes, eller der sker en lignende lignende lejlighed. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres tegnebøger.
Et farligt træk ved denne gruppe malware er, at eksempler, der ligner denne, kan tage alle systemkilder og næsten gøre offercomputeren ubrugelig, indtil truslen faktisk er blevet fjernet. De fleste af dem har en nådeløs opsætning, der gør dem virkelig vanskelige at fjerne. Disse kommandoer vil helt sikkert gøre ændringer til at starte valg, setup documents as well as Windows Registry values that will certainly make the Windows-upt.exe malware begin immediately when the computer system is powered on. Adgang til valg af rekreation mad og valgmuligheder kan blive blokeret, hvilket gør adskillige manuelle fjernelsesoversigter praktisk talt ubrugelige.
Denne særlige infektion vil bestemt konfigurere en Windows-tjeneste for sig selv, fastholdelsen af den gennemførte beskyttelse analyse ther overholde tiltag rent faktisk er blevet observeret:
Under gruvearbejderdriften kan den tilknyttede malware kobles op til allerede kørende Windows-tjenester og også installerede applikationer fra tredjepart. Dermed observerer systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en anden procedure.
| Navn | Windows-upt.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Windows-upt.exe |

Disse former for malware-infektioner er især pålidelige til at udføre sofistikerede kommandoer, hvis de er konfigureret. De er baseret på en modulær struktur, der gør det muligt for de kriminelle kontrollere at orkestrere alle slags farlige handlinger. One of the preferred examples is the adjustment of the Windows Registry – adjustments strings associated by the os can create severe performance interruptions and also the failure to accessibility Windows solutions. Relying on the extent of modifications it can additionally make the computer completely pointless. På de forskellige gengæld justering af Registry værdier, der kommer fra en hvilken som helst tredjepart oprettet programmer kan sabotere dem. Some applications might stop working to introduce altogether while others can suddenly quit working.
This certain miner in its current variation is concentrated on extracting the Monero cryptocurrency containing a customized variation of XMRig CPU mining engine. If the projects show successful then future versions of the Windows-upt.exe can be released in the future. Da malware bruger software program sårbarheder til at forurene mål værter, det kan være en del af en usikker co-infektion med ransomware og også trojanske heste.
Elimination of Windows-upt.exe is strongly recommended, since you take the chance of not just a huge electricity bill if it is operating on your COMPUTER, but the miner may additionally execute other unwanted tasks on it and also even damage your PC completely.
Windows-upt.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Windows-upt.exe
TRIN 5. Windows-upt.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Windows-upt.exe
Hvordan undgår din pc fra at blive inficeret med “Windows-upt.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Windows-upt.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Windows-upt.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Windows-upt.exe”.







