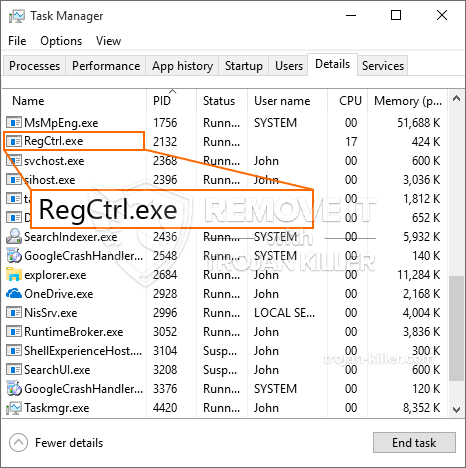
Et helt nyt, ekstremt farligt cryptocurrency minearbejder virus er blevet identificeret af forskere beskyttelse. den malware, hedder RegCtrl.exe kan forurene ofre mål ved hjælp af en række forskellige måder. Hovedidéen bag den RegCtrl.exe minearbejder er at udnytte cryptocurrency minearbejder aktiviteter på computere mål for at få Monero tokens til syge omkostninger. The end result of this miner is the raised electrical power costs and also if you leave it for longer amount of times RegCtrl.exe may also harm your computer systems components.
RegCtrl.exe: distributionssystemer Metoder
Det RegCtrl.exe malware gør brug af 2 fremtrædende teknikker, der bruges til at forurene computersystemmål:
- Payload Levering via Prior Infektioner. If an older RegCtrl.exe malware is released on the victim systems it can immediately upgrade itself or download a newer version. Dette er muligt ved hjælp af den indbyggede opdateringskommando, der opnår lanceringen. Dette gøres ved at binde sig til en bestemt foruddefineret hacker-kontrollerede server, som tilbyder den malware kode. Den downloadede infektion vil erhverve navnet på en Windows-tjeneste samt være placeret i “%systemet% temp” areal. Vigtige hjem såvel som opsætningsfiler til operativsystemet ændres for at muliggøre en vedvarende og lydløs infektion.
- Software sårbarhed udnytter. The latest variation of the RegCtrl.exe malware have actually been found to be triggered by the some exploits, populært forstået for at blive brugt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Angrebene er automatiseret af en hacker-kontrollerede rammer, som søger efter, hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert scanne tjenesten og også hente detaljer om den, inklusive enhver version samt opsætningsoplysninger. Foretagsomheder såvel som fremtrædende brugernavne og adgangskoder kan blandes. Når manipulationen er forårsaget versus risikokoden, vil minearbejderen blive frigivet sammen med bagdøren. Dette vil helt sikkert give det en dobbelt infektion.
Ud over disse teknikker kan der også gøres brug af forskellige andre strategier. Minearbejdere kan distribueres ved hjælp af phishing-e-mails, der sendes i bulk på en SPAM-lignende måde og er afhængige af socialtekniske tricks for at forvirre ofrene lige til at tro, at de faktisk har fået en besked fra en legitim løsning eller forretning. Infektionsfilerne kan enten vedhæftes direkte eller placeres i kropsmaterialerne i multimediemateriale eller meddelelseslink.
De onde kan derudover oprette destruktive websider, der kan udgøre en leverandørs download-sider, websteder til download af softwareapplikationer og forskellige andre ofte tilgængelige steder. Når de bruger lignende lydende domæne til legitime adresser og også sikkerhedscertifikater, kan kunderne tvinges lige til at kommunikere med dem. I mange tilfælde blot åbne dem kan aktivere minearbejder infektion.
En anden metode ville helt sikkert være at bruge nyttelastbærere, der kan spredes ud ved hjælp af de ovennævnte teknikker eller ved hjælp af fildelingsnetværk, BitTorrent er en af de mest foretrukne dem. Det bliver ofte brugt til at distribuere både ægte softwareprogram og også dokumenter og piratmateriale. 2 af de mest prominente haul luftfartsselskaber er følgende:
Forskellige andre teknikker, der kan tænkes på af de onde, omfatter brug af browser hijackers - skadelige plugins, som er gjort kompatible med en af de mest populære web-internetbrowsere. De sendes til de relevante databaser med falske brugerudtalelser og programmør-legitimationsoplysninger. I de fleste tilfælde kan resuméerne indeholde skærmbilleder, videoklip samt omfattende resuméer, der tilskynder til vidunderlige funktionsforbedringer og effektivitetsoptimeringer. Men efter installationen vil adfærden af de berørte browsere ændre sig- enkeltpersoner vil helt sikkert finde ud af, at de vil blive omdirigeret til en hacker-styret touchdown-side, ligesom deres opsætninger kan blive ændret – standard startside, internetsøgemaskine samt ny faneblad.

RegCtrl.exe: Analyse
The RegCtrl.exe malware is a classic instance of a cryptocurrency miner which depending on its arrangement can cause a wide variety of dangerous actions. Its major goal is to do complicated mathematical tasks that will certainly benefit from the readily available system sources: CPU, GPU, hukommelse og også harddisk værelse. The means they operate is by attaching to a special web server called mining swimming pool from where the needed code is downloaded and install. Så hurtigt som blandt de arbejdspladser er downloadet det vil blive startet samtidigt, flere tilfælde kan være væk for hvornår. When a given task is completed an additional one will certainly be downloaded and install in its place as well as the loophole will continue up until the computer system is powered off, infektionen fået fjernet eller en mere ens lejlighed sker. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres punge.
A harmful feature of this group of malware is that examples similar to this one can take all system resources and also practically make the sufferer computer system pointless up until the danger has been completely gotten rid of. The majority of them include a consistent setup which makes them actually challenging to remove. Disse kommandoer vil foretage justeringer af opstartsmuligheder, setup data as well as Windows Registry values that will certainly make the RegCtrl.exe malware begin automatically when the computer is powered on. Accessibility to recovery menus and alternatives may be obstructed which makes lots of hands-on removal guides practically pointless.
Denne vis infektion vil arrangementet en Windows-tjeneste for sig selv, overholdelse af den udførte sikkerhedsanalyse, der overholdes aktiviteter er faktisk blevet observeret:
. Under minearbejder operationer den linkede malware kan linke til i øjeblikket kører Windows løsninger og tredjeparts installerede applikationer. By doing so the system administrators may not observe that the source lots originates from a separate process.
| Navn | RegCtrl.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove RegCtrl.exe |

Denne form for malwareinfektioner er specifikt pålidelige til at udføre sofistikerede kommandoer, hvis de er konfigureret således. De er baseret på en modulær struktur, der gør det muligt for de kriminelle kontroller at koordinere alle typer farlige vaner. Blandt de foretrukne eksempler er den ændring af Windows-registreringsdatabasen – ændringsstrenge forbundet med operativsystemet kan forårsage store effektivitetsforstyrrelser såvel som manglende adgang til Windows-løsninger. Afhængigt af omfanget af ændringer kan det også gøre computersystemet totalt meningsløst. På den anden side kan manipulation af registreringsværdier, der tilhører enhver form for tredjepartsopsætningsapplikationer, underminere dem. Nogle applikationer kan komme til kort at introducere fuldstændigt, mens andre uventet kan holde op med at arbejde.
Denne visse minearbejder i sin eksisterende variation er koncentreret om at udvinde Monero-kryptovalutaen med en ændret version af XMRig CPU-minemotoren. If the campaigns verify successful then future variations of the RegCtrl.exe can be introduced in the future. Da de malware gør brug af software applikationer susceptabilities at inficere target værter, det kan være del af en farlig co-infektion med ransomware og trojanske heste.
Removal of RegCtrl.exe is highly advised, givet, at du tager chancen for ikke bare en kæmpe elregning, hvis den kører på din pc, alligevel kan minearbejderen også udføre forskellige andre uønskede aktiviteter på den og også beskadige din pc permanent.
RegCtrl.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove RegCtrl.exe
TRIN 5. RegCtrl.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove RegCtrl.exe
Hvordan undgår din pc fra at blive inficeret med “RegCtrl.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “RegCtrl.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “RegCtrl.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “RegCtrl.exe”.







