En ny, meget farlig cryptocurrency minervirus er faktisk blevet opdaget af sikkerheds- og sikkerhedsforskere. den malware, hedder NvUpdater64.exe kan forurene målofrene på en række forskellige måder. Essensen bag NvUpdater64.exe-miner er at bruge cryptocurrency-mineraktiviteter på computersystemer for mål for at få Monero-symboler til måludgifter.. Resultatet af denne miner er de forhøjede udgifter til elektrisk energi, og hvis du lader det være i længere perioder, kan NvUpdater64.exe endda skade dine computersystemer.
NvUpdater64.exe: distributionssystemer Metoder
Det NvUpdater64.exe malware benytter sig af to fremtrædende tilgange, der bruges til at forurene computermål:
- Nyttelast Levering ved hjælp af kendte Infektioner. Hvis en ældre NvUpdater64.exe malware er implementeret på målsystemerne, kan den automatisk opdatere sig selv eller downloade og installere en nyere variant. Dette er muligt ved hjælp af den integrerede opdateringskommando, der erhverver frigivelsen. Dette gøres ved at tilknytte en bestemt foruddefineret hacker-styret webserver, der leverer malware-koden. Den downloadede og installerede infektion får navnet på en Windows-løsning samt placeres i “%systemet% temp” areal. Vitale hjem og også kørende systemkonfigurationsdokumenter transformeres for at muliggøre en konsekvent og stille infektion.
- Software programmet sårbarhed udnytter. Den seneste variant af NvUpdater64.exe-malware er faktisk blevet opdaget at være forårsaget af nogle udnyttelser, berømt anerkendt for at blive gjort brug af i de ransomware overfald. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Overgrebene er automatiseret af en hacker-kontrolleret ramme som søger efter hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert kontrollere tjenesten samt indhente oplysninger om den, bestående af enhver form for version og arrangementoplysninger. Udnytter og også fremtrædende brugernavn og også adgangskoder kan gøres. Når udnyttelsen udløses mod risikokoden, udlægges minearbejderen bestemt sammen med bagdøren. Dette vil præsentere en dobbelt infektion.
Bortset fra disse teknikker kan forskellige andre teknikker også bruges. Minearbejdere kan spredes ved phishing-e-mails, der sendes ud engros på en SPAM-lignende måde og er afhængige af social design-tricks for at forvirre de syge til at tro, at de rent faktisk har fået en besked fra en velrenommeret tjeneste eller virksomhed. Infektionsdokumenterne kan enten forbindes direkte eller indsættes i kropskomponenterne i multimedieindhold eller beskedweblink.
Lovbrydere kan også udvikle destruktive destinationswebsider, der kan udgøre websider til download af leverandører, softwareprogrammets downloadportaler og forskellige andre regelmæssigt tilgængelige steder. Når de bruger sammenlignelige klingende domænenavne til legitime adresser såvel som sikkerhedscertifikater, kan kunderne blive skubbet til at kommunikere med dem. I nogle tilfælde bare åbne dem kan forårsage minearbejder infektion.
En anden teknik ville helt sikkert være at bruge udbyttere af nyttelast, der kan spredes ved hjælp af ovennævnte tilgange eller ved hjælp af dokumenter, der deler netværk, BitTorrent er blandt de mest populære dem. Det bruges regelmæssigt til at distribuere både legitim softwareapplikation og også filer og også piratmateriale. 2 af de mest fremtrædende nyttelastudbydere er følgende:
Andre teknikker, der kan tages i betragtning af lovovertrædere, består i at gøre brug af internetbrowserkapere - farlige plugins, der er kompatible med en af de mest populære webinternetbrowsere. De offentliggøres til de relevante opbevaringssteder med falske brugeranmeldelser og også designeroplysninger. I mange tilfælde kan beskrivelserne bestå af skærmbilleder, videoklip og også sofistikerede beskrivelser, der appellerer til vidunderlige attributforbedringer samt effektivitetsoptimeringer. Imidlertid vil vanerne hos de påvirkede browsere helt sikkert ændre sig ved opsætningen- kunder vil opdage, at de omdirigeres til en hackerstyret touchdown-side, og også deres indstillinger kan blive ændret – standard startside, søgemaskine på internettet samt nye faner webside.

NvUpdater64.exe: Analyse
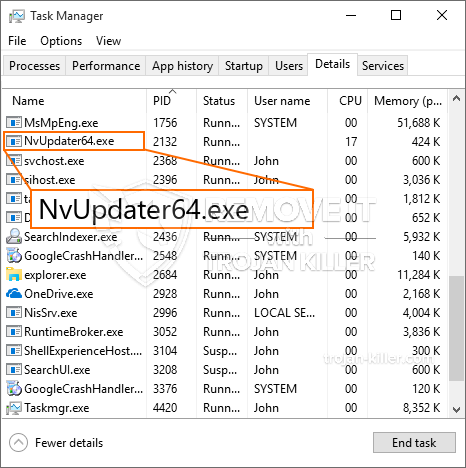
NvUpdater64.exe malware er et tidløst tilfælde af en cryptocurrency minearbejder, der afhængigt af dens opsætning kan skabe en lang række farlige aktiviteter. Dets primære mål er at udføre komplicerede matematiske job, der helt sikkert vil gøre brug af de tilbudte systemressourcer: CPU, GPU, hukommelse og også harddiskplads. Metoden, de fungerer, er ved at oprette forbindelse til en speciel webserver kaldet mining pool, hvor den krævede kode downloades og installeres. Så hurtigt som blandt job, der downloades, vil det blive startet på en gang, adskillige omstændigheder kan køres på hvornår. Når en leveret opgave er afsluttet, downloades en mere på sin plads, såvel som smuthul fortsætter, indtil computeren er slukket, infektionen elimineres eller sker anden sammenlignelig begivenhed. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking team eller en enkelt hacker) direkte til deres punge.
En usikker funktion i denne kategori malware er, at eksempler som denne kan tage alle systemkilder samt praktisk talt gøre den lidende computer ubrugelig, indtil risikoen er helt elimineret. De fleste af dem inkluderer en nådeløs installation, der gør dem virkelig udfordrende at slippe af med. Disse kommandoer vil foretage justeringer også valg, arrangement data og også Windows Registry værdier, der helt sikkert vil gøre NvUpdater64.exe malware begynder automatisk, når computersystemet er tændt. Tilgængeligheden til gendannelsesmenuer og valgmuligheder kan blive blokeret, hvilket gør masser af håndbetjente eliminationsguider næsten ineffektive.
Denne særlige infektion vil sætte en Windows-tjeneste for sig selv, efter den gennemførte sikkerheds- og sikkerhedsevaluering er der faktisk blevet observeret tilslutning til handlinger:
. I løbet af minerfunktioner kan den tilsluttede malware tilknyttes allerede kørende Windows-løsninger såvel som tredjepartsmonterede applikationer. Dermed opdager systemcheferne måske ikke, at kildetonnene stammer fra en separat procedure.
| Navn | NvUpdater64.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at opdage og fjerne NvUpdater64.exe |

Denne type malwareinfektioner er især effektive til at udføre sofistikerede kommandoer, hvis de er konfigureret således. De er baseret på en modulær struktur, der gør det muligt for de kriminelle kontrollere at styre alle slags farlige handlinger. Blandt de prominente tilfælde er ændringen af registreringsdatabasen i Windows – ændringer strenge forbundet med operativsystemet kan udløse alvorlige ydelsesforstyrrelser såvel som manglende evne til tilgængelighed Windows-tjenester. Afhængigt af omfanget af ændringer kan det desuden gøre computersystemet helt meningsløst. På den anden side kan kontrol af registreringsværdier, der kommer fra enhver form for installerede tredjepartsapplikationer, underminere dem. Nogle applikationer kan være korte til at introducere fuldstændigt, mens andre pludselig kan stoppe med at arbejde.
Denne bestemte minearbejder i sin nuværende version er fokuseret på at udvinde Monero-kryptovalutaen inklusive en tilpasset variation af XMRig CPU-minedriftmotoren. Hvis projekterne viser sig at være effektive, kan fremtidige variationer af NvUpdater64.exe frigives i fremtiden. Da malware bruger software susceptabilities forurene mål værter, det kan være en del af en skadelig co-infektion med ransomware og trojanere.
Fjernelse af NvUpdater64.exe anbefales stærkt, i betragtning af at du ikke kun risikerer store elomkostninger, hvis den fungerer på din COMPUTER, men minearbejderen kan også udføre andre uønskede opgaver på den og også endda beskadige din pc fuldstændigt.
Fjernelse af NvUpdater64.exe
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knap for at fjerne NvUpdater64.exe
TRIN 5. NvUpdater64.exe fjernet!
Video guide: Sådan bruges GridinSoft Anti-Malware til at fjerne NvUpdater64.exe
Hvordan undgår din pc fra at blive inficeret med “NvUpdater64.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “NvUpdater64.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “NvUpdater64.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “NvUpdater64.exe”.







