En ny, ekstremt skadeligt cryptocurrency minearbejder virus er faktisk blevet opdaget af sikkerhedsmæssige forskere. den malware, hedder Manager.exe kan inficere ofre mål at gøre brug af et udvalg af midler. Essensen bag Manager.exe minearbejder er at ansætte cryptocurrency minearbejder opgaver på edb-systemerne i syge med henblik på at opnå Monero symboler på de syge’ bekostning. The end result of this miner is the elevated electricity costs as well as if you leave it for longer time periods Manager.exe may also harm your computer’s elements.
Manager.exe: distributionssystemer Metoder
Det Manager.exe malware benytter sig af to fremtrædende tilgange, der bruges til at forurene computermål:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older Manager.exe malware is deployed on the target systems it can automatically update itself or download and install a newer variation. Dette er muligt ved hjælp af den integrerede opdateringskommando, der erhverver frigivelsen. Dette gøres ved at tilknytte en bestemt foruddefineret hacker-styret webserver, der leverer malware-koden. Den downloadede og installerede infektion får navnet på en Windows-løsning samt placeres i “%systemet% temp” areal. Vitale hjem og også kørende systemkonfigurationsdokumenter transformeres for at muliggøre en konsekvent og stille infektion.
- Software programmet sårbarhed udnytter. The most recent variation of the Manager.exe malware have actually been discovered to be caused by the some exploits, berømt anerkendt for at blive gjort brug af i de ransomware overfald. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Overgrebene er automatiseret af en hacker-kontrolleret ramme som søger efter hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert kontrollere tjenesten samt indhente oplysninger om den, bestående af enhver form for version og arrangementoplysninger. Udnytter og også fremtrædende brugernavn og også adgangskoder kan gøres. Når udnyttelsen udløses mod risikokoden, udlægges minearbejderen bestemt sammen med bagdøren. Dette vil præsentere en dobbelt infektion.
Bortset fra disse teknikker kan forskellige andre teknikker også bruges. Minearbejdere kan spredes ved phishing-e-mails, der sendes ud engros på en SPAM-lignende måde og er afhængige af social design-tricks for at forvirre de syge til at tro, at de rent faktisk har fået en besked fra en velrenommeret tjeneste eller virksomhed. Infektionsdokumenterne kan enten forbindes direkte eller indsættes i kropskomponenterne i multimedieindhold eller beskedweblink.
Lovbrydere kan også udvikle destruktive destinationswebsider, der kan udgøre websider til download af leverandører, softwareprogrammets downloadportaler og forskellige andre regelmæssigt tilgængelige steder. Når de bruger sammenlignelige klingende domænenavne til legitime adresser såvel som sikkerhedscertifikater, kan kunderne blive skubbet til at kommunikere med dem. I nogle tilfælde bare åbne dem kan forårsage minearbejder infektion.
En anden teknik ville helt sikkert være at bruge udbyttere af nyttelast, der kan spredes ved hjælp af ovennævnte tilgange eller ved hjælp af dokumenter, der deler netværk, BitTorrent er blandt de mest populære dem. Det bruges regelmæssigt til at distribuere både legitim softwareapplikation og også filer og også piratmateriale. 2 af de mest fremtrædende nyttelastudbydere er følgende:
Andre teknikker, der kan tages i betragtning af lovovertrædere, består i at gøre brug af internetbrowserkapere - farlige plugins, der er kompatible med en af de mest populære webinternetbrowsere. De offentliggøres til de relevante opbevaringssteder med falske brugeranmeldelser og også designeroplysninger. I mange tilfælde kan beskrivelserne bestå af skærmbilleder, videoklip og også sofistikerede beskrivelser, der appellerer til vidunderlige attributforbedringer samt effektivitetsoptimeringer. Imidlertid vil vanerne hos de påvirkede browsere helt sikkert ændre sig ved opsætningen- kunder vil opdage, at de omdirigeres til en hackerstyret touchdown-side, og også deres indstillinger kan blive ændret – standard startside, søgemaskine på internettet samt nye faner webside.

Manager.exe: Analyse
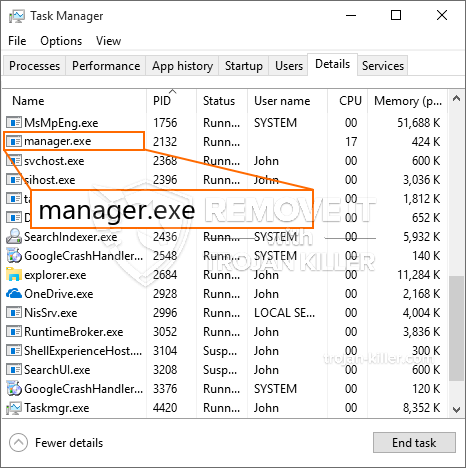
The Manager.exe malware is a timeless case of a cryptocurrency miner which relying on its configuration can cause a wide variety of harmful activities. Its primary goal is to do complex mathematical tasks that will make the most of the available system sources: CPU, GPU, hukommelse og harddisk område. The way they function is by connecting to an unique web server called mining pool from where the called for code is downloaded and install. Så hurtigt som en af opgaverne downloades, vil den helt sikkert blive startet på samme tid, flere forekomster kan være væk, så snart. When an offered task is completed an additional one will be downloaded and install in its location as well as the loophole will certainly proceed until the computer system is powered off, the infection is gotten rid of or another similar occasion happens. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking team eller en enkelt cyberpunk) direkte til deres tegnebøger.
A hazardous attribute of this category of malware is that examples like this one can take all system sources as well as virtually make the sufferer computer system pointless until the hazard has been entirely eliminated. A lot of them feature a persistent setup which makes them truly challenging to eliminate. Disse kommandoer vil foretage justeringer for at starte alternativer, configuration data and also Windows Registry values that will certainly make the Manager.exe malware start instantly as soon as the computer is powered on. Accessibility to healing food selections and alternatives may be obstructed which provides lots of hands-on removal overviews virtually ineffective.
Denne særlige infektion vil helt sikkert konfigurere en Windows-tjeneste for sig selv, complying with the carried out security analysis ther following actions have actually been observed:
. Under minearbejdsprocedurerne kan den tilsluttede malware vedhæfte Windows-løsninger, der kører i øjeblikket, samt installerede applikationer fra tredjepart. By doing so the system managers might not discover that the source load comes from a different procedure.
| Navn | Manager.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Manager.exe |

Disse former for malware-infektioner er særligt effektive til at udføre innovative kommandoer, hvis de er konfigureret sådan. They are based upon a modular framework enabling the criminal controllers to orchestrate all kinds of dangerous habits. En af de foretrukne tilfælde er ændringen af Registry Windows – modifications strings connected by the operating system can trigger significant efficiency interruptions and also the failure to access Windows solutions. Depending on the extent of changes it can likewise make the computer completely pointless. På de forskellige gengæld manipulation af Registry worths tilhører nogen form for tredjeparts monteret programmer kan sabotere dem. Some applications might stop working to introduce completely while others can unexpectedly stop working.
This certain miner in its existing variation is focused on extracting the Monero cryptocurrency including a changed version of XMRig CPU mining engine. If the projects confirm successful then future variations of the Manager.exe can be launched in the future. Da malware udnytter software program sårbarheder til at inficere target værter, det kan være del af en skadelig co-infektion med ransomware og også trojanske heste.
Elimination of Manager.exe is strongly suggested, since you take the chance of not just a huge power costs if it is working on your COMPUTER, however the miner might also perform various other undesirable activities on it and also harm your COMPUTER permanently.
Manager.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Manager.exe
TRIN 5. Manager.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Manager.exe
Hvordan undgår din pc fra at blive inficeret med “Manager.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Manager.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Manager.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Manager.exe”.







