Et helt nyt, meget farlig cryptocurrency minearbejder virus er faktisk blevet opdaget af sikkerhedsmæssige forskere. den malware, hedder Lsma12.exe kan forurene ofre mål ved hjælp af en række forskellige måder. Essensen bag Lsma12.exe minearbejder er at ansætte cryptocurrency minearbejder aktiviteter på computerne af ofre for at få Monero symboler på syge udgifter. Resultatet af denne minearbejder er de forhøjede elektriske strømudgifter såvel som hvis du lader det være i længere tid Lsma12.exe kan endda skade dine computersystemelementer.
Lsma12.exe: distributionssystemer Metoder
Det Lsma12.exe malware udnytter 2 foretrukne fremgangsmåder, der anvendes til at kontaminere computersystemmål:
- Payload Levering via Prior Infektioner. Hvis en ældre Lsma12.exe malware frigives på offerets systemer, kan den øjeblikkeligt opdatere sig selv eller downloade en nyere variation. Dette er muligt gennem den integrerede opgraderingskommando, der får lanceringen. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede server, som giver malware kode. Den downloadede infektion vil helt sikkert erhverve navnet på en Windows service og også være placeret i “%systemet% temp” placere. Livsvigtige bygninger og konfigurationsfiler til operativsystemet transformeres for at muliggøre en nådeløs og stille infektion.
- Software Application sårbarhed udnytter. Den mest aktuelle variation af Lsma12.exe malware er faktisk blevet opdaget at være forårsaget af nogle ventures, populært forstået for at blive brugt i ransomware-angreb. Infektionerne er færdig ved at målrette åbne løsninger gennem TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som søger efter hvis porten er åben. Hvis denne betingelse er opfyldt, vil den scanne løsningen og hente oplysninger om den, herunder enhver form for versionen og arrangement information. Ventures og også fremtrædende brugernavn samt kodeordkombinationer kan muligvis udføres. Når udnyttelsen udløses mod den sårbare kode, minearbejder vil blive indsat sammen med bagdøren. Dette vil danne en dobbelt infektion.
Bortset fra disse tilgange kan andre metoder også anvendes. Gruvearbejdere kan spredes ved phishing-e-mails, der sendes i bulk på en SPAM-lignende måde, samt afhænge af sociale design-tricks for at forvirre de syge lige til at tro, at de har fået en besked fra en ægte løsning eller virksomhed. Infektionsfilerne kan enten direkte vedhæftes eller placeres i kropsmaterialet i multimedieindhold eller weblink til meddelelser.
Skurkerne kan på samme måde fremstille ondsindede destinationssider, der kan udgive sig for sælgeres download og installation af sider, softwareprogrammer downloader websteder og også andre områder, der regelmæssigt har adgang til. Når de bruger lignende tilsyneladende domæne til legitime adresser såvel som sikkerheds- og sikkerhedscertifikater, overtales kunderne muligvis lige til at engagere sig med dem. Undertiden blot åbne dem kan udløse minearbejder infektion.
En anden fremgangsmåde ville være at anvende nyttelastbærere, der kan spredes ved hjælp af disse teknikker eller ved hjælp af datadelingsnetværk, BitTorrent er blot en af en af de mest populære dem. Det bruges ofte til at sprede både legitim softwareapplikation og dokumenter og også piratindhold. To af en af de mest foretrukne trækholdere er følgende:
Andre metoder, der kan tages i betragtning af de forkerte, inkluderer brug af internetbrowser-kaprere - skadelige plugins, der er gjort kompatible med en af de mest foretrukne internetbrowsere. De indsendes til de relevante opbevaringssteder med falske brugeranmeldelser og også udvikleroplysninger. I de fleste tilfælde beskrivelserne kan omfatte skærmbilleder, videoer og indviklede beskrivelser, der lover fantastiske funktioner og effektivitetsoptimeringer. Imidlertid vil opførslen af de påvirkede internetbrowsere bestemt ændre sig ved installationen- enkeltpersoner vil opdage, at de vil blive omdirigeret til en hacker-kontrolleret touchdown-side, og deres opsætninger kan også ændres – standard startside, online søgemaskine og også nye faneblade.

Lsma12.exe: Analyse
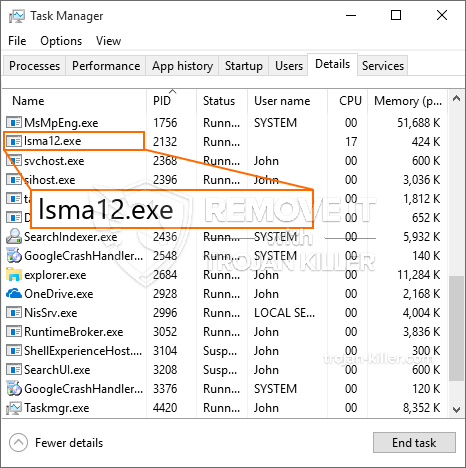
Lsma12.exe-malware er et traditionelt tilfælde af en cryptocurrency-miner, som kan stole på dens arrangement kan udløse en lang række skadelige aktiviteter. Dets hovedmål er at udføre komplicerede matematiske opgaver, der helt sikkert vil gøre brug af de let tilgængelige systemressourcer: CPU, GPU, hukommelse og harddiskplads. Midlerne, de arbejder på, er ved at knytte til en unik server kaldet mining pool, hvorfra den kaldte kode downloades. Så snart et af jobene er downloadet, startes det samtidig, adskillige tilfælde kan gå væk så snart. Når en given opgave er afsluttet, downloades en anden i sit område, og smuthullet fortsætter helt sikkert, indtil computersystemet er slukket, infektionen fjernes, eller der sker en lignende lignende lejlighed. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres tegnebøger.
Et farligt træk ved denne gruppe malware er, at eksempler, der ligner denne, kan tage alle systemkilder og næsten gøre offercomputeren ubrugelig, indtil truslen faktisk er blevet fjernet. De fleste af dem har en nådeløs opsætning, der gør dem virkelig vanskelige at fjerne. Disse kommandoer vil helt sikkert gøre ændringer til at starte valg, installationsdokumenter såvel som Windows-registerværdier, der helt sikkert får Lsma12.exe malware til at begynde med det samme, når computersystemet er tændt. Adgang til valg af rekreation mad og valgmuligheder kan blive blokeret, hvilket gør adskillige manuelle fjernelsesoversigter praktisk talt ubrugelige.
Denne særlige infektion vil bestemt konfigurere en Windows-tjeneste for sig selv, fastholdelsen af den gennemførte beskyttelse analyse ther overholde tiltag rent faktisk er blevet observeret:
. Under gruvearbejderdriften kan den tilknyttede malware kobles op til allerede kørende Windows-tjenester og også installerede applikationer fra tredjepart. Dermed observerer systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en anden procedure.
| Navn | Lsma12.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware til at registrere og fjerne Lsma12.exe |

Denne slags malware-infektioner er især effektive til at udføre sofistikerede kommandoer, hvis de er konfigureret sådan. De er baseret på en modulopbygget struktur, der tillader de kriminelle kontrollører at orkestrere alle slags skadelige vaner. En af de foretrukne tilfælde er ændringen af Registry Windows – ændringsstrenge, der er forbundet med operativsystemet, kan udløse alvorlige forstyrrelser i ydelsen såvel som den manglende evne til at få adgang til Windows-tjenester. At stole på omfanget af ændringer kan det på samme måde gøre computersystemet helt ubrugeligt. På den anden side kan manipulation af registerværdier, der kommer fra alle typer tredjepartsmonterede applikationer, underminere dem. Nogle programmer kan stoppe med at arbejde for at lancere helt, mens andre uventet kan stoppe med at arbejde.
Denne bestemte miner i sin nuværende variation er fokuseret på at udvinde Monero cryptocurrency, der har en modificeret version af XMRig CPU-minedriftmotor. Hvis projekterne viser sig at være vellykkede efter det, kan fremtidige versioner af Lsma12.exe introduceres i fremtiden. Da malware bruger sårbarheder i software til at forurene mål værter, det kan være en del af en skadelig co-infektion med ransomware og trojanere.
Fjernelse af Lsma12.exe anbefales stærkt, da du tager chancen for ikke kun store elektriske energiomkostninger, hvis det fungerer på din pc, endnu kan miner også på anden måde udføre andre uønskede opgaver på det og også skade din COMPUTER permanent.
Lsma12.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” -knap for at fjerne Lsma12.exe
TRIN 5. Lsma12.exe fjernet!
Video guide: Sådan bruges GridinSoft Anti-Malware til at fjerne Lsma12.exe
Hvordan undgår din pc fra at blive inficeret med “Lsma12.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Lsma12.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Lsma12.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Lsma12.exe”.







