En ny, virkelig skadelig cryptocurrency miner infektion er faktisk blevet opdaget af beskyttelsesforskere. den malware, hedder Cmdsrvs.exe kan forurene måloffer, der bruger en række metoder. Hovedpointen bag Cmdsrvs.exe-miner er at bruge cryptocurrency miner-opgaver på computerens mål for at få Monero-tokens til måludgifter.. Resultatet af denne miner er de hævede udgifter til elektrisk energi, og også hvis du forlader det i længere perioder, kan Cmdsrvs.exe også skade dine computerdele.
Cmdsrvs.exe: distributionssystemer Metoder
Det Cmdsrvs.exe malware anvendelser 2 foretrukne teknikker, der anvendes til at inficere computersystemmål:
- Nyttelast Levering ved hjælp af kendte Infektioner. Hvis en ældre Cmdsrvs.exe malware er installeret på målsystemerne, kan den straks opgradere sig selv eller downloade en nyere variation. Dette er muligt via den indbyggede opdatering kommando, som opnår frigivelse. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. Den downloadede og installerede infektion vil helt sikkert få navnet på en Windows-løsning og også være placeret i “%systemet% temp” placere. Vigtige bygninger og også driftssystemarrangementsdokumenter transformeres for at tillade en vedvarende og også lydløs infektion.
- Software sårbarhed udnytter. Den nyeste version af Cmdsrvs.exe malware er blevet opdaget at være udløst af nogle udnyttelser, berømt anerkendt for at blive brugt i ransomware-angreb. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis dette problem er opfyldt, vil det bestemt kontrollere tjenesten og få oplysninger om det, inklusive enhver variation såvel som arrangementsdata. Ventures og populære brugernavn og også adgangskodemix kan gøres. Når udnyttelsen aktiveres mod den modtagelige kode, installeres minearbejderen sammen med bagdøren. Dette vil danne en dobbelt infektion.
Bortset fra disse metoder kan andre metoder også anvendes. Gruvearbejdere kan distribueres ved phishing-e-mails, der sendes engros på en SPAM-lignende måde, samt afhænge af social designteknikker for at pusle målene direkte i at tro, at de har modtaget en besked fra en ægte tjeneste eller virksomhed. Infektionsfilerne kan enten være direkte forbundet eller placeres i kropsindholdet i multimedie-webindhold eller meddelelseslink.
De dårlige fyre kan på samme måde oprette destruktive touchdown-websider, der kan udgive sig for sælgers download og installation af websider, software-downloadportaler samt forskellige andre ofte tilgængelige steder. Når de bruger lignende tilsyneladende domæne som legit adresser og også sikkerheds- og sikkerhedscertificeringer, kan kunderne muligvis skubbes ind i forbindelse med dem. I nogle tilfælde blot åbne dem kan udløse minearbejder infektion.
En yderligere teknik ville helt sikkert være at bruge transportudbydere, der kan spredes ved hjælp af de ovennævnte fremgangsmåder eller ved hjælp af delingsnetværk, BitTorrent er blandt de mest foretrukne. Det bruges regelmæssigt til at distribuere både ægte softwareprogram og dokumenter såvel som piratwebindhold. 2 af en af de mest foretrukne leverandører af transporttjenester er følgende:
Andre metoder, som de onde kan tænke på, inkluderer brugen af internetbrowser-kaprere - farlige plugins, der er gjort kompatible med en af de mest populære internetbrowsere.. De uploades til de relevante opbevaringssteder med falske brugeranmeldelser og designeroplysninger. I mange tilfælde resuméerne kan omfatte skærmbilleder, videoklip såvel som detaljerede beskrivelser, der appellerer til fantastiske funktionsforbedringer samt effektivitetsoptimeringer. Imidlertid vil opførelsen af de påvirkede webbrowsere ændre sig ved opsætning- enkeltpersoner vil lokalisere, at de helt sikkert vil blive omdirigeret til en hacker-kontrolleret touchdown-webside, så deres indstillinger kunne ændres – standard webside, internetsøgemaskine samt splinterny faneblad side.

Cmdsrvs.exe: Analyse
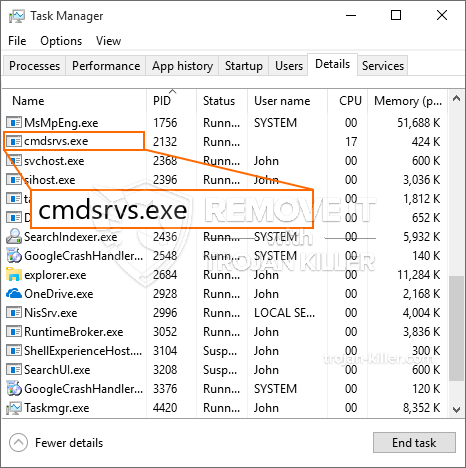
Cmdsrvs.exe-malware er en traditionel situation for en cryptocurrency-miner, som kan stole på dens arrangement kan forårsage en lang række usikre handlinger. Dets hovedmål er at udføre komplekse matematiske job, der vil gøre brug af de let tilgængelige systemkilder: CPU, GPU, hukommelse og også harddisk område. Metoden, de arbejder, er ved at knytte til en unik server kaldet mining swimmingpool, hvorfra den nødvendige kode downloades. Så snart blandt de arbejdspladser er downloadet det vil blive startet på samme tid, flere omstændigheder kan udføres på en gang. Når et tilbudt job er afsluttet, downloades et bestemt bestemt i sit område, og loopen fortsætter også, indtil computeren er slukket, infektionen er fjernet eller ét forekommer mere sammenlignelig begivenhed. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking team eller en enkelt hacker) direkte til deres punge.
Et farligt kendetegn ved denne klassificering af malware er, at prøver som denne kan tage alle systemkilder og praktisk talt gøre målcomputeren ubrugelig, indtil faren er fuldstændig fjernet. Mange af dem inkluderer en ensartet installation, der gør dem virkelig udfordrende at slippe af med. Disse kommandoer vil foretage justeringer også valg, konfigurationsfiler såvel som Windows-registerværdier, der helt sikkert får Cmdsrvs.exe malware til at starte automatisk, når computersystemet er tændt. Tilgængelighed til helende menuer såvel som alternativer kan være hindret, hvilket giver flere håndbetjente fjernelsesoversigter næsten ineffektive.
Denne vis infektion vil arrangementet en Windows-tjeneste for sig selv, efter den gennemførte sikkerhedsevaluering er der faktisk blevet observeret overholdelse af handlinger:
. I løbet af minerprocedurerne kan den tilsluttede malware linke til aktuelt kørende Windows-løsninger og også tredjepartsmonterede applikationer. Ved at gøre dette systemets ledere ikke kan observere, at de ressourcemæssige tons stammer fra en særskilt procedure.
| Navn | Cmdsrvs.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware at registrere og fjerne Cmdsrvs.exe |

Denne type malware-infektioner er især pålidelige til at udføre innovative kommandoer, hvis de er konfigureret sådan. De er baseret på en modulopbygget ramme, der gør det muligt for de kriminelle kontrollører at koordinere alle former for farlig adfærd. Et af de fremtrædende tilfælde er ændringen af Windows-registreringsdatabasen – ændringsstrenge, der er forbundet med os, kan skabe alvorlige ydelsesforstyrrelser såvel som manglende evne til at få adgang til Windows-løsninger. At stole på justeringsområdet, kan det også gøre computersystemet helt ubrugeligt. På den anden side kan manipulation af Registreringsværdier, der kommer fra alle slags tredjepartsinstallationer, underminere dem. Nogle programmer kan undlade at frigive helt, mens andre uventet kan afslutte arbejde.
Denne særlige miner i sin nuværende version er koncentreret om minedrift af Monero cryptocurrency med en tilpasset variation af XMRig CPU-minedriftmotor. Hvis kampagnerne viser sig effektive efter det, kan fremtidige variationer af Cmdsrvs.exe introduceres i fremtiden. Da malware udnytter software ansøgning susceptabilities at forurene mål værter, det kan være en del af en usikker co-infektion med ransomware og også trojanske heste.
Eliminering af Cmdsrvs.exe anbefales kraftigt, i betragtning af at du tager chancen for ikke kun en enorm elektrisk energiregning, hvis den kører på din COMPUTER, men minearbejderen kan desuden udføre andre uønskede opgaver på den såvel som også skade din pc permanent.
Cmdsrvs.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” -knap for at fjerne Cmdsrvs.exe
TRIN 5. Cmdsrvs.exe blev fjernet!
Video guide: Sådan bruges GridinSoft Anti-Malware til at fjerne Cmdsrvs.exe
Hvordan undgår din pc fra at blive inficeret med “Cmdsrvs.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Cmdsrvs.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Cmdsrvs.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Cmdsrvs.exe”.







