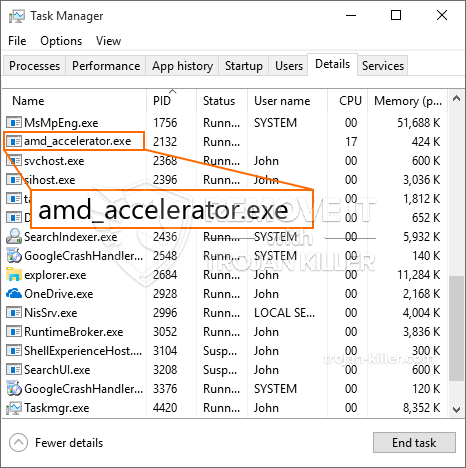
En ny, virkelig farligt cryptocurrency minearbejder virus er blevet fundet ved sikkerhed og sikring forskere. den malware, hedder Amd_accelerator.exe kan forurene target syge ved hjælp af forskellige måder. Hovedidéen bag Amd_accelerator.exe minearbejderen er at anvende cryptocurrency minearbejde på ofrenes computersystemer for at erhverve Monero-symboler til syge omkostninger. The end result of this miner is the raised electrical power expenses and if you leave it for longer amount of times Amd_accelerator.exe may also harm your computer systems elements.
Amd_accelerator.exe: distributionssystemer Metoder
Det Amd_accelerator.exe malware anvendelser 2 preferred methods which are made use of to infect computer targets:
- Payload Levering via Prior Infektioner. If an older Amd_accelerator.exe malware is released on the sufferer systems it can immediately update itself or download and install a more recent version. Dette er muligt ved hjælp af den integrerede opdateringskommando, som henter lanceringen. Dette gøres ved at knytte til en bestemt foruddefineret hacker-kontrolleret server, der giver malware-koden. Den downloadede infektion får bestemt navnet på en Windows-løsning og placeres i “%systemet% temp” areal. Important residential or commercial properties and operating system configuration documents are transformed in order to allow a relentless and also quiet infection.
- Software Application sårbarhed udnytter. The newest variation of the Amd_accelerator.exe malware have been located to be caused by the some ventures, almindeligt kendt for at blive udnyttet i de ransomware strikes. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Overgrebene er automatiseret af en hacker-kontrolleret ramme som opsøger hvis porten er åben. If this condition is satisfied it will certainly check the service and retrieve info regarding it, including any variation and configuration data. Ventures såvel som fremtrædende brugernavn og også adgangskodekombinationer kan gøres. When the make use of is caused versus the at risk code the miner will certainly be released together with the backdoor. Dette vil bestemt præsentere en dobbelt infektion.
In addition to these techniques other approaches can be used also. Miners can be dispersed by phishing e-mails that are sent in bulk in a SPAM-like fashion and also depend on social engineering tricks in order to perplex the sufferers right into thinking that they have received a message from a legitimate service or firm. The virus documents can be either straight affixed or placed in the body components in multimedia content or text links.
The bad guys can also create destructive landing web pages that can pose vendor download and install pages, software application download sites as well as other often accessed places. When they use similar sounding domain names to genuine addresses and safety and security certificates the customers may be persuaded into interacting with them. I nogle tilfælde blot at åbne dem kan modregne minearbejder infektion.
One more strategy would be to utilize haul service providers that can be spread out utilizing the above-mentioned methods or through file sharing networks, BitTorrent er blandt en af de mest populære. It is often used to disperse both legit software application and also files and also pirate material. To af en af de mest foretrukne lastbærere er følgende:
Other approaches that can be taken into consideration by the lawbreakers include making use of internet browser hijackers -harmful plugins which are made suitable with the most popular web browsers. They are posted to the appropriate repositories with phony individual testimonials and designer credentials. Oftentimes beskrivelserne kan bestå af skærmbilleder, video clips as well as intricate summaries encouraging fantastic attribute improvements and also performance optimizations. Nevertheless upon installment the habits of the affected browsers will certainly alter- individuals will certainly locate that they will be redirected to a hacker-controlled landing page as well as their setups may be modified – standard startside, internetsøgemaskine samt splinterny faneblad side.

Amd_accelerator.exe: Analyse
The Amd_accelerator.exe malware is a traditional instance of a cryptocurrency miner which depending upon its arrangement can create a wide variety of hazardous activities. Dens hovedformål er at udføre komplicerede matematiske opgaver, der helt sikkert vil drage fordel af de tilbudte systemkilder: CPU, GPU, hukommelse samt harddisk plads. Metoden, de bruger, er ved at oprette forbindelse til en unik server kaldet mining pool, hvorfra den nødvendige kode downloades. Så snart blandt de arbejdspladser er downloadet det vil blive startet på samme tid, flere forekomster kan køres på én gang. Når et givent job er færdigt, vil et mere blive downloadet på dets placering, og løkken fortsætter, indtil computersystemet slukkes, infektionen fjernes, eller der sker en yderligere sammenlignelig begivenhed. Cryptocurrency vil helt sikkert blive belønnet for de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) lige til deres budgetter.
En usikker kvalitet ved denne kategori af malware er, at prøver som denne kan tage alle systemressourcer og praktisk talt gøre målcomputersystemet meningsløst, indtil truslen er fuldstændig elimineret. De fleste af dem har en vedvarende opsætning, som gør dem faktisk svære at fjerne. Disse kommandoer vil foretage justeringer for at starte alternativer, arrangement files as well as Windows Registry values that will certainly make the Amd_accelerator.exe malware begin immediately as soon as the computer is powered on. Adgang til gendannelsesmenuer og også valg kan være blokeret, hvilket giver adskillige manuelle fjernelsesoversigter praktisk talt ubrugelige.
Denne specifikke infektion vil arrangementet en Windows-tjeneste for sig selv, at overholde den udførte sikkerheds- og sikkerhedsevaluering, er følgende handlinger faktisk blevet observeret:
. Under minedriftsprocedurerne kan den tilsluttede malware linke til allerede kørende Windows-løsninger og tredjeparts opsætningsapplikationer. Ved at gøre det kan systemadministratorerne muligvis ikke observere, at ressourcebelastningen kommer fra en anden procedure.
| Navn | Amd_accelerator.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Amd_accelerator.exe |

Disse slags malware-infektioner er særligt effektive til at udføre avancerede kommandoer, hvis de er konfigureret. They are based on a modular structure enabling the criminal controllers to manage all kinds of harmful behavior. Blandt de foretrukne tilfælde er justeringen af Windows-registreringsdatabasen – alterations strings associated by the operating system can cause serious performance disruptions and the failure to access Windows services. Depending upon the scope of adjustments it can likewise make the computer system completely pointless. On the various other hand adjustment of Registry worths belonging to any type of third-party set up applications can undermine them. Some applications might stop working to introduce completely while others can suddenly quit working.
This certain miner in its existing variation is concentrated on extracting the Monero cryptocurrency containing a changed version of XMRig CPU mining engine. If the projects prove successful then future versions of the Amd_accelerator.exe can be launched in the future. Da malware gør brug af software program sårbarheder til at inficere target værter, det kan være del af en skadelig co-infektion med ransomware og trojanske heste.
Elimination of Amd_accelerator.exe is highly advised, because you take the chance of not only a large electrical energy costs if it is operating on your PC, however the miner may also do various other unwanted tasks on it and even damage your COMPUTER permanently.
Amd_accelerator.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Amd_accelerator.exe
TRIN 5. Amd_accelerator.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Amd_accelerator.exe
Hvordan undgår din pc fra at blive inficeret med “Amd_accelerator.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Amd_accelerator.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Amd_accelerator.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Amd_accelerator.exe”.







