Back in February of this year, 16-year-old bug-hunter from their Czech Republic, Thomas Orlita, discovered a dangerous vulnerability in a Google backend application.
Discovered bug allowed stealing cookies from company’s internal applications and user’s cookies, and with their help organize phishing attacks and access other parts of Google internal network.The problem was fixed in April, and, after waiting some time, Orlita decided to reveal details of the discovered vulnerability publicly.
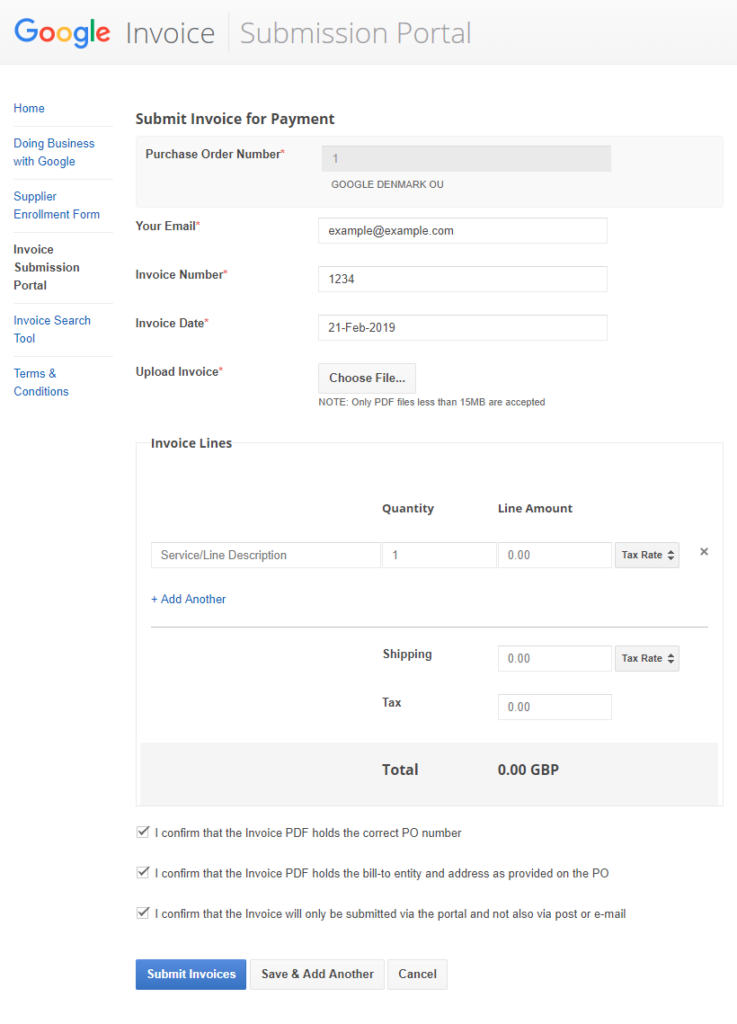
The vulnerability was XSS (cross-site scripting) on the Google Invoice Submission Portal (gist-uploadmyinvoice.appspot.com), through which company’s business partners submit invoices for payment under already arranged contracts.
The researcher discovered that attacker could upload specially modified files using the Upload Invoice field.
Using a proxy, attacker could intercept downloaded file immediately after adding the form, but before validation took place.
“Apart from text input, there’s also an input for selecting a PDF file. Though it’s in a way that only PDF files can be selected uploading. Since this is only front-end validation, it doesn’t stop us from changing file type while sending for uploading POST request. Once we select any PDF file, an upload request is fired. We can intercept the request using a web proxy debugger and change the filename and the contents from .pdf to .html”, – said Thomas Orlita.
After modifying the document from PDF to HTML, data falls on Google backend, where it was automatically executed when the employee tried to view them.
«The XSS bug was triggered on the googleplex.com subdomain, say, xxx.googleplex.com, when an employee logged on to the system. Since arbitrary javascript can be performed on this subdomain, an attacker gains access to the control panel on this subdomain, where is possible to view and manage accounts. Depending on the cookie settings on googleplex.com, it was also possible to access other internal applications hosted on this domain”, – Orlita explains.
Google fixed a bug.
The XSS is now on a sandboxed domain where the XSS poses no risk for the user.
Source: https://appio.dev
