About .CHECH
.CHECH is classified by our malware research team as the brand-new ransomware infection. Some anti-virus programs already spot it, nonetheless, there are certain applications that bypass it and also thus permit its breach. Individuals have actually concerned calling it that, due to the extension, it includes at the end of your files. Let’s specify. Ransomware tool attack your computer via slyness as well as skill. Then, once they enter, they spread their corruption. They use file encryption formulas to lock your data. After that, extort you for their launch. After .CHECH sneaks right into your system, it places every one of your files under lock-down. It connects its very own extension at the end, thus making it inaccessible. And also, no documents can leave its reach. It targets records, archives, images, songs, video clips, all of it! After that, you can much longer open it. Moving the documents, or relabeling it, won’t help. The only way to release your data from the ransomware’s maintain, is compliance. The infection expects you to pay a ransom money, if you wish to free your documents. It makes that clear, in the ransom note it leaves after file encryption. The note is typically a text documents, left on your Desktop. You can likewise find it in every folder which contains locked data. It describes your predicament, and also gives you a way out. According to .CHECH, the only means to release your files is with an unique decryption key. As well as, to get it, you should pay a ransom money. The quantity varies, and it’s typically asked for in Bitcoin. Yet other cryptocurrencies are additionally an option. The infection guarantees, to send you the trick you require, after you complete the transfer. And, that’s it. That’s all you get– a guarantee. You have zero warranties that compliance leads to something positive. Do not rest on words of cyber offenders. These are unstable individuals with harmful schedules. People, who will certainly double-cross you. Do NOT pay them a penny. Don’t call them Do NOT comply with their demands. It may seem a tough contact us to make, but it’s the right one.
Special Offer
.CHECH encrypted your documents, but that might not be the only damage done to you. The ransomware might still be hidingon your computer. To identify whether this holds true, we suggest downloading GridinSoft Anti-Malware.
Download GridinSoft Anti-Malware
GridinSoft Anti-Malware Review, How to get free trial?, EULA, and Privacy Policy.

Exactly how did my system got damaged by .CHECH?
Your computers gets contaminated with the .CHECH virus due to your failing to be conscientious. Some individuals do not take note of important details while surfing the web or installing numerous programs. As well as, perhaps this is the means you ended up with an infection. Right here’s the important things. The infection makes use of the old but gold intrusive techniques to deceive you. As well as, slide past you unnoticed. That consists of hiding behind corrupted web links, sites, and torrents. It utilizes freeware as a way to hide itself. And, impersonates a fake system or program update. Like, Adobe Flash Player or Java. Yet, more often than not, it uses spam emails. You obtain an e-mail that seems to come from a well-known business. Like, Amazon or PayPal. As well as, the e-mail urges you to click a link, or download and install an add-on. If you do, you end up with a ransomware. Remember that these types of threats exploit your carelessness. They need you to rush, as well as avoid doing due persistance. That alleviates their concealed infiltration. They rely on you to leave your destiny to chance. Don’t! Don’t choose carelessness over care. One keeps infections out. The various other invites them in.

Why is .CHECH harmful?
Do NOT act the method .CHECH instructs you. Obeying its hazardous commands is dangerous as well as will clearly make your budget thinner. For this reason, do not pay them cash. Do not reach out to the cyber abductors. If you do, you’ll regret it. It’s a futile attempt to reclaim your information, and also it will not finish well for you. Right here’s why. There are a couple of circumstances that can unfold, when you see the ransom money note on your display. Say, you decide to comply. You connect to the extortionists, pay their ransom, and wait. You await them to send you the decryption secret they guaranteed. Well, what if they do not? After all, you have no warranties. All, you rest on, is a pledge. Can you genuinely believe the word of cyber abductors? The response is ‘No.’ These are people, that will dissatisfy you. Don’t give them loan! There’s also another alternative. They can, in fact, send you a decryption secret. Yet, when you try to use it, it stops working to function. Yes, they can send you the incorrect one. Then, you have less loan, as well as your data continues to be secured. Do not pay! As well as, also your best-case scenario, isn’t a reason for delight. What happens after you pay the ransom money, obtain the right key, and also cost-free your data? Well? Think about it. You paid loan to get rid of a sign, however not the infection causing it. So, you eliminate the security, yet the .CHECH ransomware remains. It’s still prowling in the edges of your system, cost-free to strike once again. Then, you’re back at fresh start. There aren’t enough methods to stress this enough. Do NOT pay!
.CHECH is getting on the nerves of many users, so you’re not its only victim.
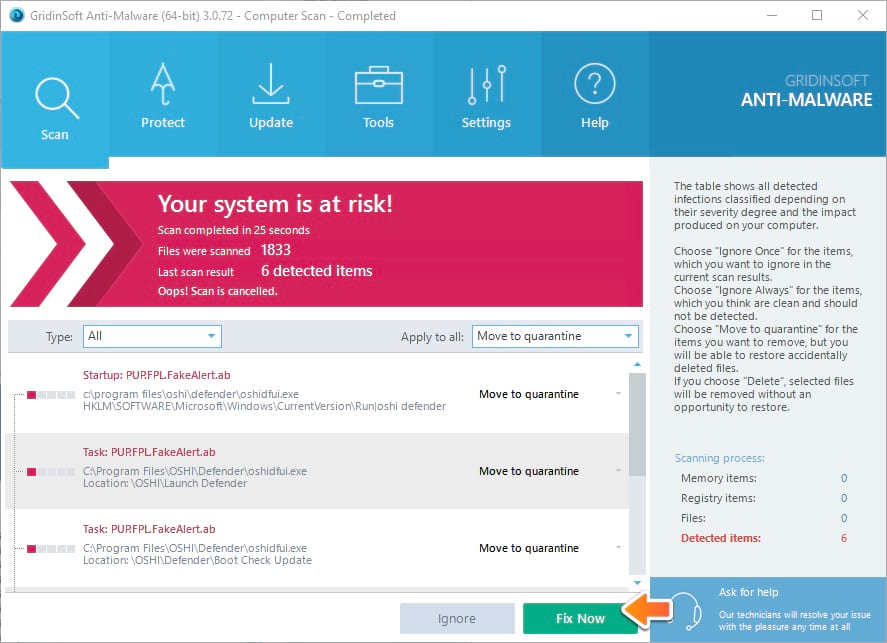
People ask how to fix the problem effectively. Getting rid of the infection manually may be a long-lasting undertaking and can damage other important system files. Scan your PC with GridinSoft Anti-Malware to detect and delete .CHECH in the right way.

GridinSoft Anti-Malware Review, How to get free trial?, EULA, and Privacy Policy.
So, your computer obtained struck by .CHECH and probably you have lost time attempting to eliminate it manually. We are definitely certain that the remedy below will definitely be effective in removing .CHECH in an automated way. However allow us initially discuss avoidance of such ransomware attacks in future. Exists something that you can do to avoid this type of unpleasant threat from entering your computer beforehand? There are couple of points we would like to discuss right here. Initially one is your individual duty for being exceptionally careful while you utilize your computer system and largely while you browse the internet. When examining your email as well as see some dubious accessories included, do not hurry up to open them. In the same way, when you get on Facebook and also someone in your get in touches with sends you messages including add-ons, be extremely mindful, specifically if these are some executable documents. The second thing to think about is examining the integrity of your present anti-virus program. Regretfully, there are numerous security applications these days that just assert to be reliable, whereas in times of genuine malware breaches they merely stop working to do the task as advertised. In instance .CHECH permeated right into your computer this implies that your present anti-virus did not execute its advertised function and also actually fell short to shield your system. So, clearly, it is a reason for you to reevaluate your selections and also absolutely change to some other application that can most definitely render the wanted degree of protection. We might additionally discuss some percent of users who like not to have any kind of anti-virus software application in all. Certainly, this is a major blunder on their part, because presently the world wide web is full of cyber dangers that may privately penetrate susceptible systems, particularly those that are not furnished with some basic level of safety and security. So, having anti-malware permanently running and protecting your computer is a must-do point in today’s cyber globe.
STEP 1. Recover files from .CHECH ransomware encryption
There are a lot of different ransomware viruses on the internet. Some of them are more dangerous than the others because they not only leaving malicious processes to protect themselves, but also removing backups of your system to make the recovery process impossible.
Please Note: Not all ransomware infections are able to remove backups of your system, so it is always worth to try a windows recovery method below. In order to protect your backups from this danger, try our Anti-Ransomware product:
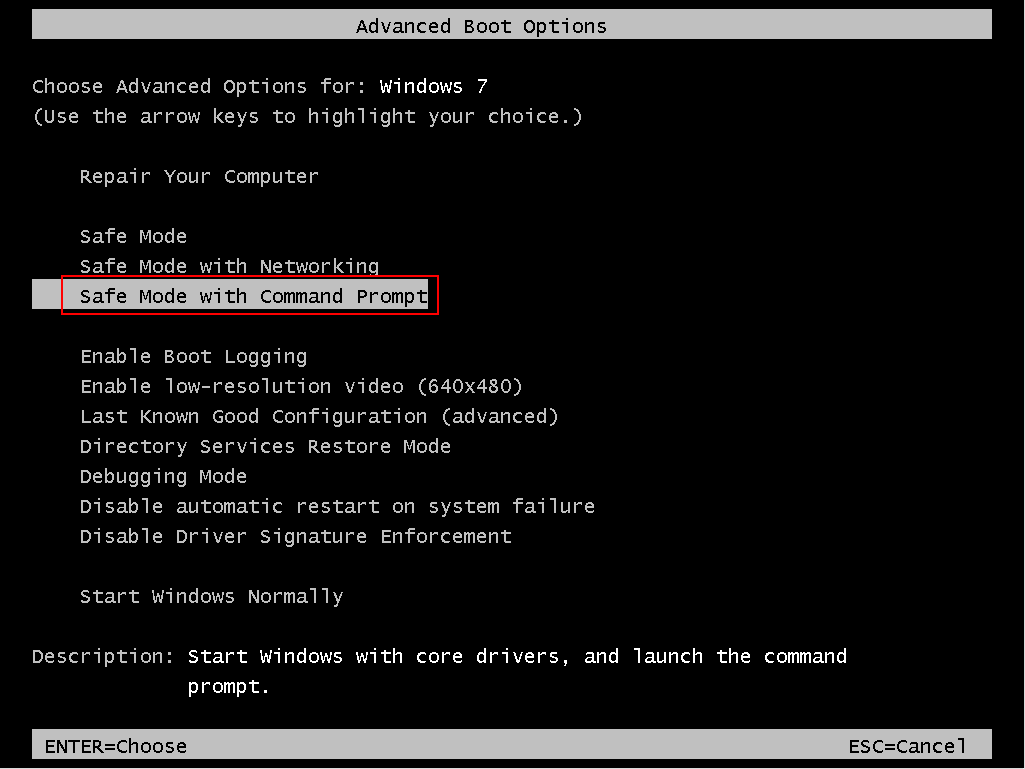
We recommend use Safe Mode with command prompt to safely perform a recovery of your files. You will have to reboot your computer, so you better save this instruction some where on your hard drive or read if from second computer.
-
Windows 7 users: You need to reboot your system and before its loaded constantly press “F8” button until you see boot options.
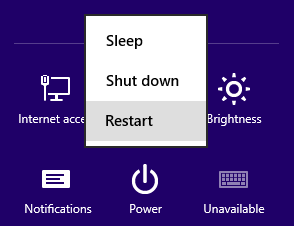
- Windows 8/10 users: Press the “Power” button from Windows login screen or Settings. Hold the Shift key on your keyboard and click on “Restart”
- After your computer reboots – Click on “Troubleshoot” – press “Advanced options” – “Startup Settings”
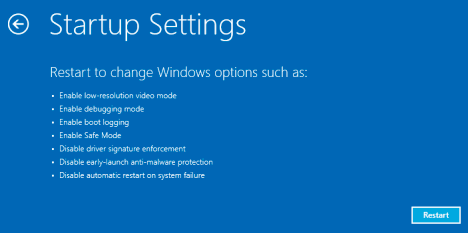
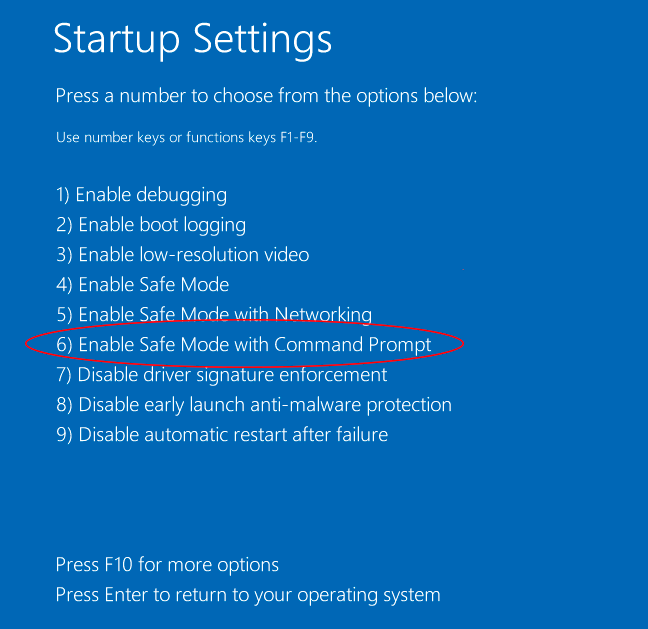
- Click the “Restart” button and your computer will reload again and show you the list with all options. You need to choose the “Safe Mode with Command Prompt”
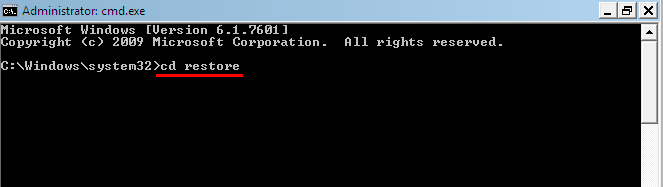
- When your windows loads, enter the following line: cd restore and press Enter.
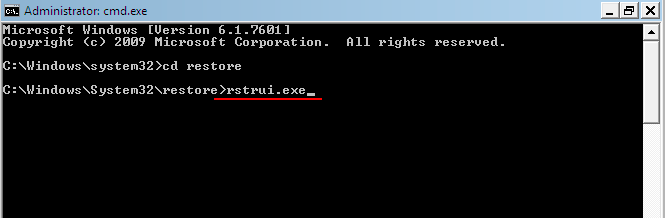
- After that type rstrui.exe line and press Enter.
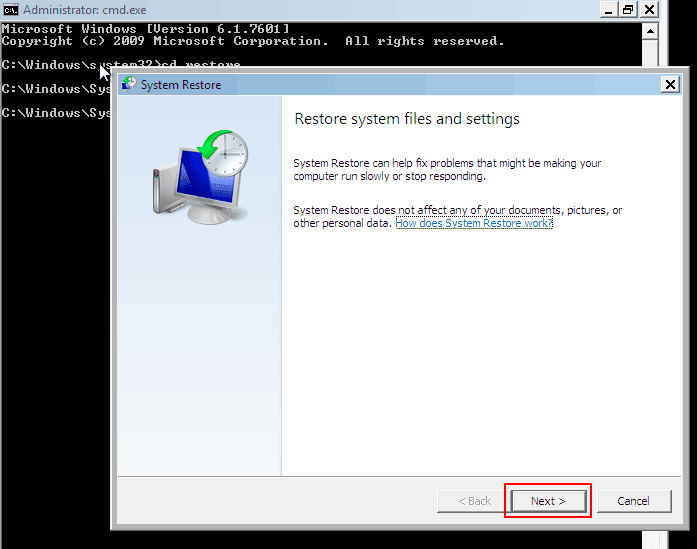
- A recovery window will open before you, Click Next to proceed.
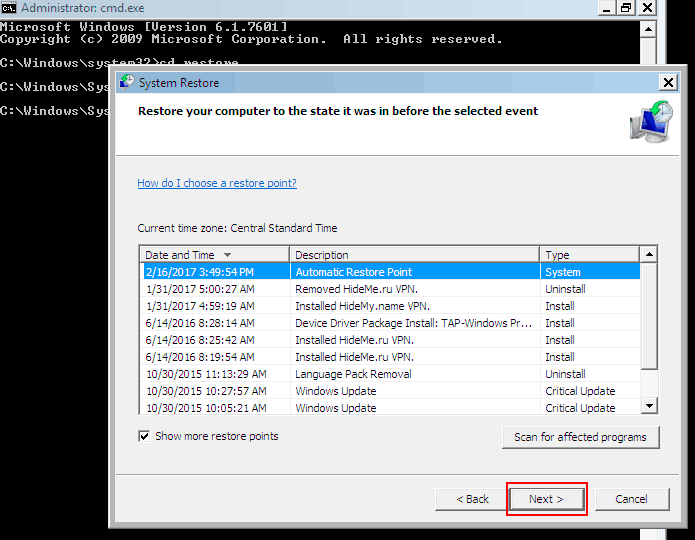
- In the next window, you need to choose a Restore point. All files in protected drives will be recovered at the time when this point was created (prior to the infection with .CHECH). In the case when ransomware removes these backups, there will be no Restore points listed. Select a Restore point and click “Next”.
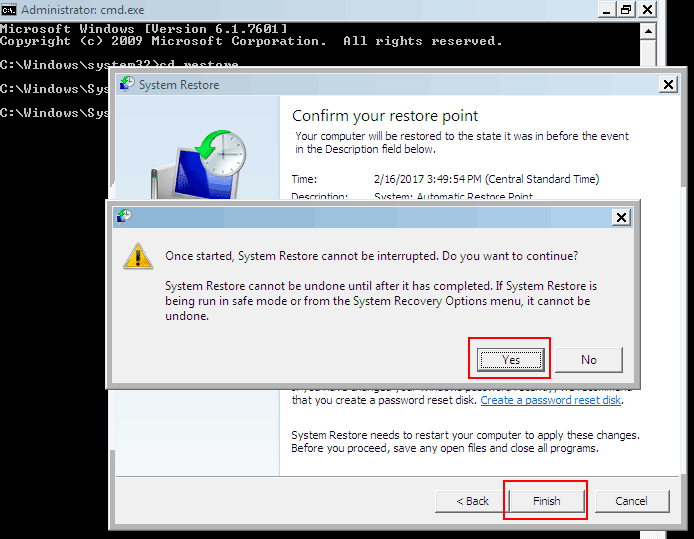
- Click “Finish” in this window and confirm the recovery process by pressing “Yes“.
Simple example of how to recover your files from ransomware infection:
STEP 2. Removing .CHECH ransomware malicious files
Once the recovery process is complete, you should consider scanning your computer with a GridinSoft Anti-Malware in order to find any traces of .CHECH infection. Though some ransomware viruses are removing themselves right after the encryption of your files, some may leave malicious processes on your computer for special purposes of cyber criminals.
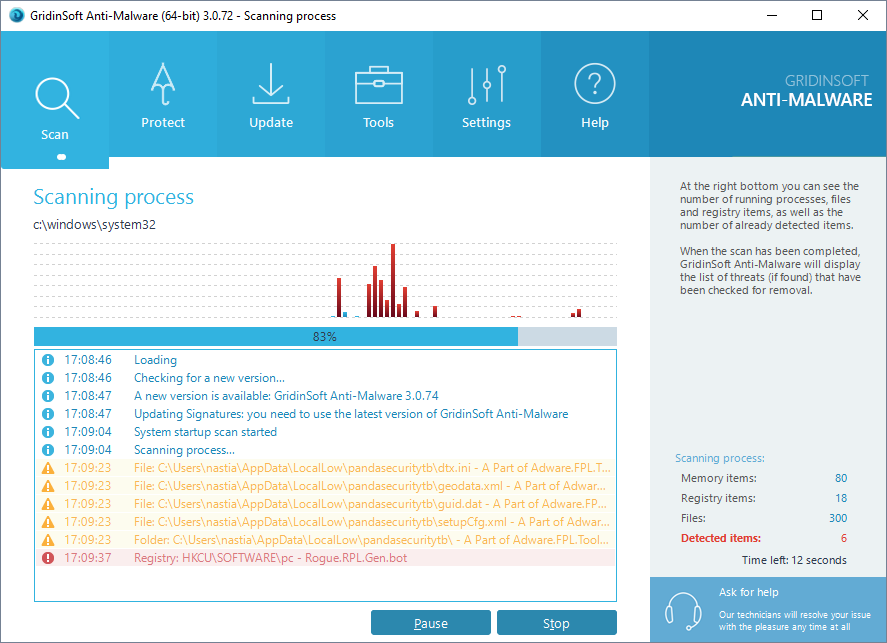
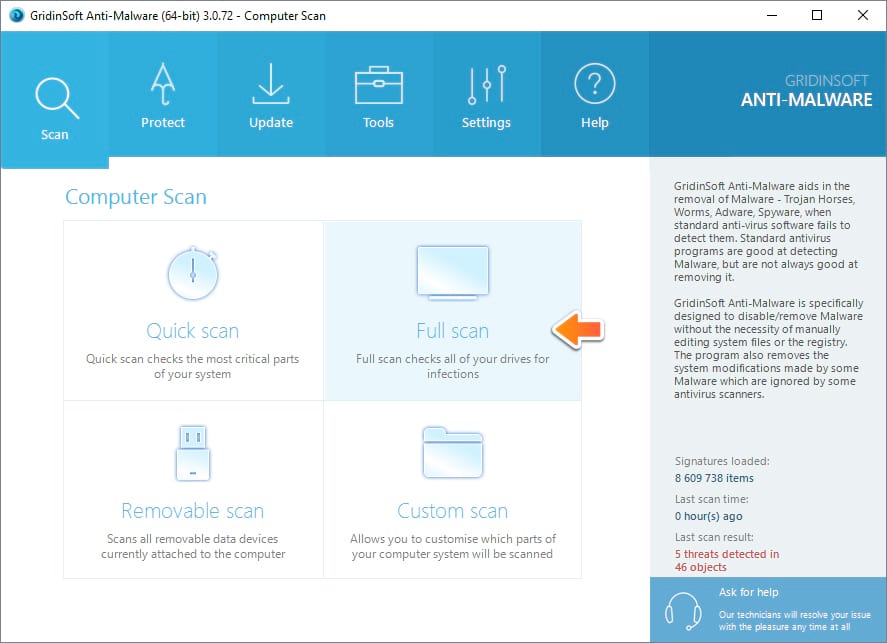
- Run GridinSoft Anti-Malware and choose the scan type, which is suitable for your needs. Of course, for the accuratest scan results we recommend you to choose the “Full Scan”.
- Give Anti-Malware a little time to check your system:
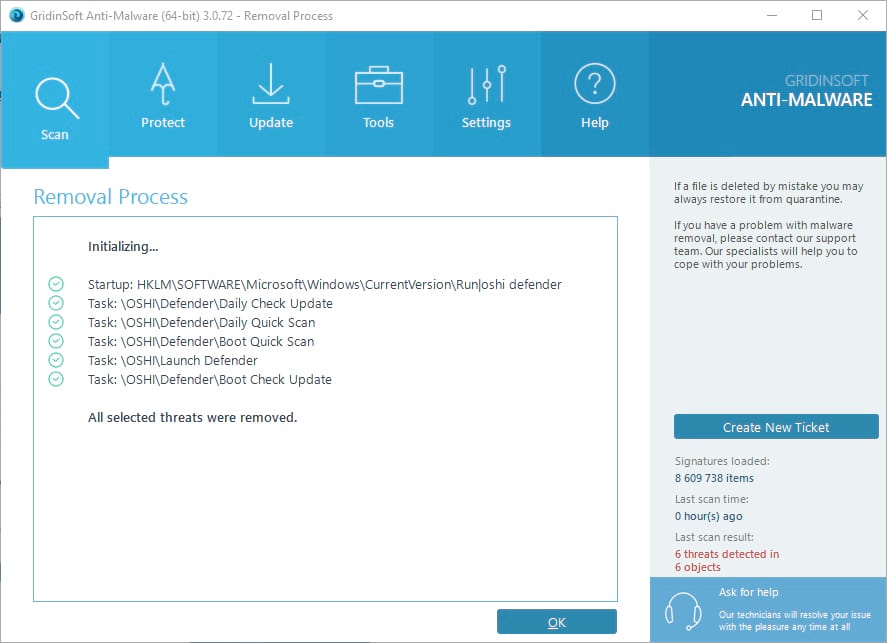
- Move to quarantine all the viruses and unwanted files, that you see in the results list:
- Enjoy the malware removal process:
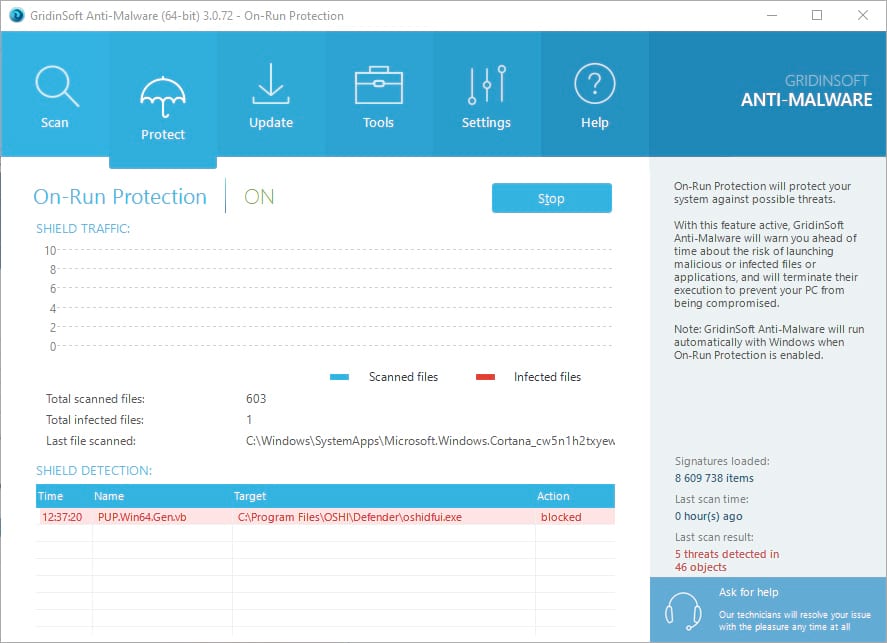
Use of On-run protection may additionaly prevent different types of cyber attacks, our protect may flag the downloader of the ransomware as a malicious application preventing the download of .CHECH.
STEP 3. Prevent the .CHECH ransomware infection with GridinSoft Anti-Ransomware
Despite that some ransomware can remove backups of your OS, our product GridinSoft Anti-Ransomware is able to protect them from the removing in the first place. When some kind of a malicious program or ransomware virus tries to delete your backups, out program intercepts this request and blocks the sending process.
Note: that the product is still in Beta testing phase, some bugs and glitches are possible.
Besides the protection tool, you should read and learn few simple rules. Follow them every time you work on your computer and your will decrease chances of your infection to a minimum:
- Don’t open suspicious spam letters. No way! Be very careful with your downloads. Download and install software preferably from its official website.
- Do backups of your important files regularly. Storing your really important files in few different places is a good decision.
- Keep your system free from adware, hijackers and PUPs The infected computer will be more likely compromised with other malicious software, and ransomware is not an exception in this case.
- Don’t panic and be reasonable. Don’t pay the ransom fee right after you got infected, it is always best to search on the internet for some answers. It is possible that someone have developed a decryption tool that might help you.