
Uma equipe de pesquisadores dos Estados Unidos, Austrália e Áustria desenvolveu uma nova versão de ataque Rowhammer.
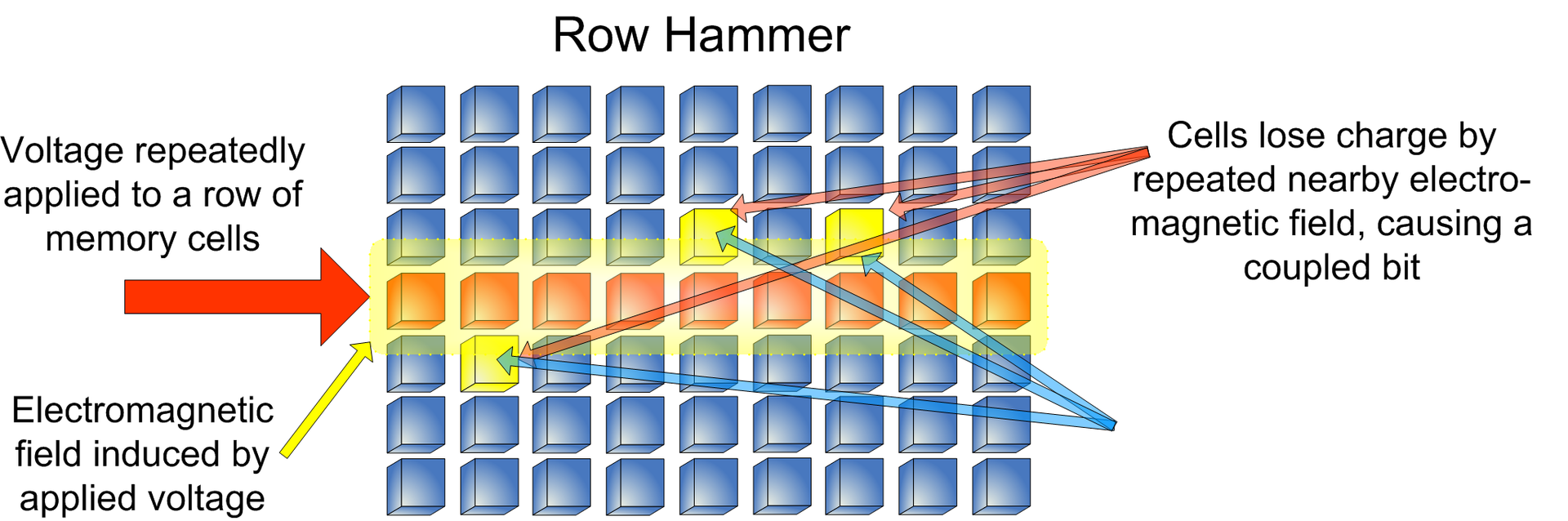
oncomo as versões anteriores, um novo ataque chamado RAMBleed permite não apenas modificar dados e aumentar privilégios, mas também roubar dados armazenados no dispositivo.Rowhammer é uma classe de vulnerabilidade hardware explorar (CVE-2019-0174) em cartões de memória modernos. Por padrão, os dados nos cartões de memória são armazenados em células localizadas em um chip de silício em linhas formando uma grade.
Em 2014, cientistas descobriram que várias leituras de dados armazenados na mesma linha resultam em uma carga elétrica que pode afetar os dados em linhas adjacentes. O ataque foi chamado Marreta, e com sua ajuda, cientistas podem danificar dados ou usá-los para fins maliciosos.
Desde a 2014, pesquisadores expandiram significativamente as capacidades do ataque original, Contudo, só agora era possível remover dados da memória e roubá-los.
“É amplamente assumido, no entanto,, esse bit vira dentro da memória privada do adversário não tem implicações de segurança, pois o invasor já pode modificar sua memória privada por meio de operações regulares de gravação. Demonstramos que essa suposição é incorreta empregando Rowhammer como um canal de leitura. Mais especificamente, mostramos como um invasor sem privilégios pode explorar a dependência de dados entre os bits induzidos por Rowhammer e os bits nas linhas próximas para deduzir esses bits, incluindo valores pertencentes a outros processos e ao kernel”, - relatório pesquisadores.
Para tornar possível o ataque RAMBleed, cientistas conseguiram forçar alocador de memória Linux (alocador de amigos) para habilitar um grande bloco de endereços físicos consecutivos que permitiram orquestrar o ataque.
Pesquisadores criaram um novo mecanismo, “Quadro Feng Shui“, para colocar as páginas do programa da vítima no lugar certo na memória física. além do que, além do mais, eles desenvolveram um novo método de gerenciar dados na memória e repetir sua leitura (o chamado martelamento de linha) para determinar quais dados estão nas células de memória vizinhas.
"Desta forma, A principal contribuição deste trabalho é mostrar que Rowhammer é uma ameaça não só à integridade, mas também à confidencialidade”, — dizem os cientistas.
Fonte: https://rambleed.com/docs/
