Um novo em folha, muito perigosa infecção criptomoeda mineiro realmente foi detectado por cientistas de segurança. o malware, chamado ZM.exe pode contaminar sofredores alvo utilizando uma variedade de métodos. A ideia principal por trás do minerador ZM.exe é utilizar tarefas de minerador de criptomoedas nos computadores das vítimas para adquirir símbolos Monero ao custo das vítimas. O resultado final deste minerador são os elevados gastos com energia elétrica e também se você deixá-lo por períodos mais longos, o ZM.exe também pode danificar os componentes do seu computador.
ZM.exe: Métodos de distribuição
o ZM.exe utiliza de malware 2 abordagens populares que são usados para infectar alvos de computador:
- Payload Entrega através de infecções anteriores. Se um malware ZM.exe mais antigo for implantado nos sistemas de destino, ele poderá se atualizar automaticamente ou baixar uma variação mais recente. Isso é possível por meio do comando de atualização integrado que recebe o lançamento. Isto é feito, anexando a um determinado servidor controlado por hackers predefinido que fornece o código de malware. O vírus baixado adquirirá o nome de uma solução Windows e também será colocado no “%% Temp sistema” localização. As propriedades essenciais, bem como os documentos de configuração do sistema em execução, são transformados para permitir uma infecção implacável e silenciosa.
- Software exploração de vulnerabilidades de aplicativos. Descobriu-se que a variação mais atual do malware ZM.exe é desencadeada por alguns exploits, conhecido por ser usado em ataques de ransomware. As infecções são feitas por alvo serviços abertos através da porta TCP. Os ataques são automatizados por um quadro controlado por hackers que olha para cima se a porta está aberta. Se esta condição for atendida, certamente irá escanear o serviço e recuperar detalhes sobre ele, constituído por qualquer tipo de variação, bem como informações arranjo. Exploits, bem como nome de usuário preferido, bem como misturas de senha pode ser feito. Quando o uso é causado contra o código propenso, o minerador certamente será implantado além do backdoor. Isto irá apresentar a uma infecção dupla.
Além dessas técnicas, várias outras técnicas podem ser usadas também. Os mineradores podem ser distribuídos por e-mails de phishing que são enviados em massa de maneira semelhante a SPAM, bem como dependem de técnicas de design social para deixar os sofredores perplexos a acreditar que receberam uma mensagem de um serviço ou empresa legítimo. Os arquivos de vírus podem ser anexados diretamente ou inseridos no conteúdo do corpo em conteúdo multimídia ou links da web de mensagens.
Além disso, os infratores podem produzir páginas de destino prejudiciais que podem representar o download e a instalação de páginas da web do fornecedor, sites de download de aplicativos de software, bem como outros locais regularmente acessados. Quando eles utilizam nomes de domínio de aparência semelhante para endereços legítimos e também certificações de segurança e proteção, os clientes podem ser persuadidos a se comunicar com eles. Às vezes, basta abri-los pode desencadear a infecção mineiro.
Mais uma técnica certamente seria usar transportadores de transporte que podem ser espalhados utilizando os métodos mencionados acima ou usando redes de compartilhamento de dados, BitTorrent está entre um dos mais preferidos. É usado regularmente para dispersar aplicativos de software respeitáveis, bem como arquivos e material pirata. 2 dos mais prestadores de serviços de destaque de carga útil são os seguintes:
Várias outras técnicas que podem ser levadas em consideração pelos infratores da lei consistem no uso de seqüestradores de navegador da Internet - plugins prejudiciais que são adequados aos navegadores da web mais proeminentes. Eles são enviados aos repositórios pertinentes com depoimentos falsos de clientes, bem como qualificações de programadores. Em muitos casos, as descrições podem incluir screenshots, vídeos e também resumos sofisticados incentivando grandes melhorias de recursos, bem como otimizações de eficiência. No entanto, após a instalação, os hábitos dos navegadores da Web influenciados certamente mudarão- os clientes descobrirão que serão redirecionados para uma página de touchdown controlada por hackers, bem como suas configurações poderão ser alteradas – a página web padrão, motor de busca na internet e também a página web novas guias.
ZM.exe: Análise
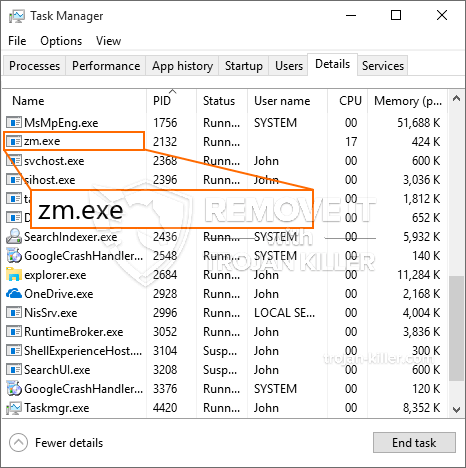
O malware ZM.exe é uma situação atemporal de um minerador de criptomoedas que dependendo de sua configuração pode criar uma grande variedade de ações inseguras. Seu principal objetivo é realizar tarefas matemáticas complexas que capitalizarão as fontes do sistema disponíveis: CPU, GPU, memória, bem como espaço no disco rígido. O método que eles trabalham é vinculando-se a um servidor web especial chamado pool de mineração de onde o código necessário é baixado e instalado. Assim que um dos trabalhos é descarregado certamente será iniciada de imediato, várias circunstâncias pode ser executado em quando. Quando um trabalho fornecido for concluído, mais um será baixado em seu lugar, assim como o loop certamente continuará até que o computador seja desligado, a infecção está se livrado ou uma ocasião mais comparável ocorre. Criptomoeda certamente será compensada para os controladores criminais (Hacker equipe ou um hacker solitário) direto para suas bolsas.
Uma característica insegura deste grupo de malware é que exemplos semelhantes a este podem levar todos os recursos do sistema, bem como virtualmente tornar o sistema do computador da vítima inútil até que a ameaça seja totalmente eliminada. A maioria deles inclui uma configuração implacável que os torna realmente difíceis de remover. Estes comandos fará mudanças também escolhas, dados de configuração e também valores do Registro do Windows que farão com que o malware ZM.exe seja iniciado instantaneamente assim que o computador for ligado. O acesso a seleções de alimentos curativos, bem como escolhas, pode ser obstruído, o que torna praticamente inúteis várias visões gerais de remoção prática.
Esta infecção particular configuração de um serviço do Windows por si mesmo, cumprindo com a análise de segurança e proteção realizada, o cumprimento das atividades foram realmente observados:
. Durante as operações do minerador, o malware vinculado pode se conectar a serviços do Windows já em execução e aplicativos montados de terceiros. Ao fazer isso, os gerentes de sistema podem não observar que os lotes de recursos se originam de um processo diferente.
| Nome | ZM.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware para detectar e remover ZM.exe |
id =”82228″ alinhar =”aligncenter” largura =”600″]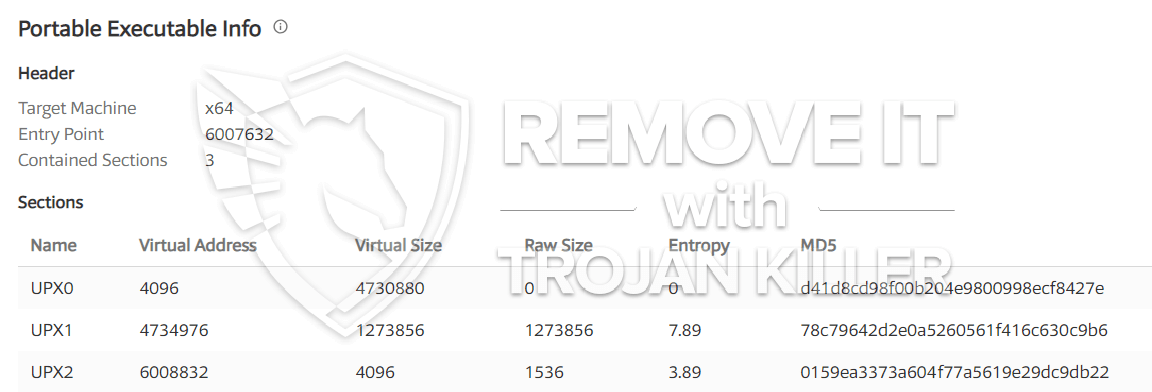 ZM.exe
ZM.exe
Esses tipos de infecções por malware são especificamente eficazes na execução de comandos sofisticados se configurados de forma. Eles são baseados em uma estrutura modular que permite aos controladores criminais orquestrar todo tipo de comportamento perigoso. Um dos exemplos populares é a alteração do Registro do Windows – seqüências de modificações associadas pelo sistema operacional podem criar sérias interrupções de eficiência e a falha na acessibilidade das soluções Windows. Dependendo do escopo dos ajustes, também pode tornar o computador completamente inutilizável. Por vários outros ajuste mão de Valores do Registro vindo de qualquer conjunto de terceiros até aplicações podem sabotar-los. Alguns aplicativos podem parar de funcionar para liberar completamente, enquanto outros podem parar de funcionar inesperadamente.
Este determinado minerador em sua variação existente está concentrado na extração da criptomoeda Monero, incluindo uma versão alterada do mecanismo de mineração XMRig CPU. Se os projetos confirmarem a eficácia, versões futuras do ZM.exe poderão ser lançadas no futuro. Como o malware utiliza susceptabilities software para contaminar anfitriões alvo, ele pode ser componente de uma co-infecção prejudicial com ransomware e também Trojans.
A eliminação de ZM.exe é altamente sugerida, dado que você corre o risco não apenas de uma enorme conta de eletricidade se estiver rodando no seu COMPUTADOR, no entanto, o minerador também pode executar outras tarefas indesejáveis nele e até mesmo danificar seu COMPUTADOR permanentemente.
Processo de remoção do ZM.exe
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” botão para remover ZM.exe
Degrau 5. ZM.exe removido!
Guia de vídeo: Como usar o GridinSoft Anti-Malware para remover ZM.exe
Como evitar que o seu PC seja infectado novamente com “ZM.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “ZM.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “ZM.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “ZM.exe”.