Um novo, extremamente infecção prejudicial criptomoeda mineiro realmente foi encontrado por pesquisadores de segurança e proteção. o malware, chamado Service64.exe pode contaminar sofredores alvo utilizando uma variedade de métodos. A principal idéia por trás do mineiro Service64.exe é utilizar atividades criptomoeda mineiro nos computadores das vítimas, a fim de obter símbolos monero em despesas alvos. O resultado deste minerador é o aumento das contas de energia elétrica e também se você deixá-lo por períodos mais longos, o Service64.exe pode até prejudicar os elementos do seu computador.
Service64.exe: Métodos de distribuição
o Service64.exe malware usa duas técnicas importantes que são utilizadas para contaminar os alvos do sistema de computador:
- Payload Entrega usando Infecções anteriores. Se um malware Service64.exe mais antigo for implantado nos sistemas da vítima, ele pode se atualizar imediatamente ou baixar uma variação mais recente. Isso é possível usando o comando de atualização integrado que obtém o release. Isto é feito, anexando a um determinado servidor controlado por hackers predefinido que fornece o código de malware. A infecção baixada certamente obterá o nome de um serviço do Windows e será posicionada no “%% Temp sistema” área. Casas importantes e também documentos de configuração do sistema em execução são transformados para permitir uma infecção implacável e silenciosa.
- Software exploração de vulnerabilidades de aplicativos. A versão mais recente do malware Service64.exe foi localizada para ser desencadeada por alguns exploits, amplamente conhecido por ser usado nos ataques ransomware. As infecções são feitas pelo direccionamento soluções abertas por meio da porta TCP. Os ataques são automatizados por uma estrutura controlada hacker que olha para cima se a porta é aberta. Se esta condição for cumprida, certamente irá verificar a solução e também recuperar informações a respeito dela, incluindo qualquer variação e informações de configuração. Ventures, bem como combinações de nome de usuário e senha preferenciais podem ser feitas. Quando a exploração é causada contra o código suscetível, o minerador certamente será lançado junto com a porta dos fundos. Isso certamente vai apresentar a uma infecção dupla.
Em adição a estas abordagens vários outros métodos podem também ser utilizados. Os mineiros podem ser dispersos por e-mails de phishing enviados em massa de maneira semelhante a SPAM e dependem de métodos de design social para confundir os alvos, levando-os a pensar que receberam uma mensagem de uma solução ou empresa confiável. Os documentos de vírus podem ser anexados diretamente ou colocados no corpo de materiais em conteúdo multimídia ou links de texto da web.
Os criminosos também podem criar páginas de touchdown destrutivas que podem se passar por páginas da web de download do fornecedor, sites de programa de download de software, bem como vários outros locais regularmente acessados. Quando eles utilizam nomes de domínio com aparência comparável a endereços legítimos, bem como certificados de proteção e segurança, os usuários podem ser persuadidos a se conectar com eles. Em alguns casos simplesmente abri-los pode causar a infecção mineiro.
Uma técnica adicional seria certamente a utilização de transportadores que podem ser difundidos utilizando esses métodos ou por meio de redes de compartilhamento de dados, BitTorrent é apenas um dos mais preferidos. É frequentemente utilizado para dispersar software e documentos genuínos, bem como conteúdo pirata. Dois dos provedores de carga útil mais populares são os seguintes:
Outras técnicas que podem ser consideradas pelos malfeitores consistem em fazer uso de sequestradores de navegador - plug-ins perigosos que são adequados para um dos navegadores de Internet mais populares. Eles são enviados para os bancos de dados pertinentes com depoimentos de usuários falsos e credenciais de desenvolvedor. Muitas vezes as descrições podem incluir screenshots, videoclipes e descrições elaboradas encorajando grandes aprimoramentos de atributos e também otimizações de eficiência. No entanto, após a instalação, o comportamento dos navegadores influenciados irá alterar- os indivíduos certamente descobrirão que serão redirecionados para uma página de destino controlada por um hacker, bem como suas configurações podem ser modificadas – a página web padrão, motor de pesquisa online e nova página tabs.

Service64.exe: Análise
O malware Service64.exe é uma instância atemporal de um minerador de criptomoedas que, dependendo de sua configuração, pode causar uma ampla gama de ações perigosas. Seu principal objetivo é realizar tarefas matemáticas complicadas que se beneficiarão das fontes de sistema prontamente disponíveis: CPU, GPU, memória e também espaço no disco rígido. O método que eles funcionam é anexando a um servidor web especial chamado pool de mineração de onde o código necessário é baixado. Tão rapidamente como entre os trabalhos é descarregado será iniciado simultaneamente, inúmeros casos pode ser ido para tão logo. Quando uma tarefa oferecida for concluída, outra certamente será baixada em seu local e a brecha continuará até que o sistema do computador seja desligado, a infecção é removida ou outra ocasião comparável acontece. Criptomoeda certamente será compensada para os controladores criminais (grupo de hackers ou de um cyberpunk solitária) direto para suas carteiras.
Um atributo prejudicial deste grupo de malware é que exemplos semelhantes a este podem pegar todas as fontes do sistema, bem como praticamente tornar o sistema do computador alvo inútil até que a ameaça tenha sido totalmente removida. Muitos deles incluem uma instalação implacável que os torna realmente difíceis de remover. Estes comandos farão ajustes para arrancar opções, dados de configuração e valores do Registro do Windows que certamente farão o malware Service64.exe iniciar automaticamente quando o sistema do computador for ligado. A acessibilidade às seleções de alimentos de recuperação e também alternativas pode ser obstruída, o que fornece vários guias de remoção prática praticamente inúteis.
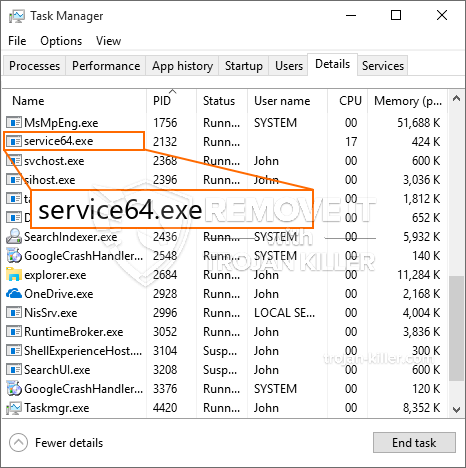
Esta infecção específica configuração de um serviço do Windows por si mesmo, após a avaliação de proteção realizada, as seguintes ações foram observadas:
. Durante os procedimentos de mineração, o malware conectado pode se conectar a soluções do Windows já em execução e também a aplicativos de terceiros instalados. Ao fazer isso, os gerentes de sistema podem não descobrir que as toneladas de origem se originam de um procedimento diferente.
| Nome | Service64.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware para detectar e remover Service64.exe |

Esse tipo de infecção por malware é especialmente eficiente na realização de comandos avançados, se configurado para. Eles são baseados em uma estrutura modular, permitindo que os controladores criminais orquestrem todos os tipos de hábitos inseguros. Um dos exemplos proeminentes é o ajuste do Registro do Windows – strings de ajustes relacionadas pelo sistema operacional podem causar interrupções de desempenho significativas, bem como a incapacidade de acessar os serviços do Windows. Contando com a gama de modificações, pode, adicionalmente, tornar o sistema de computador totalmente inutilizável. Por outro lado, o ajuste dos valores do Registro pertencentes a qualquer tipo de aplicativo de terceiros instalado pode sabotá-los. Alguns aplicativos podem parar de funcionar para serem liberados completamente, enquanto outros podem parar de funcionar de repente.
Este minerador específico em sua versão existente é focado em extrair a criptomoeda Monero que consiste em uma versão alterada do mecanismo de mineração XMRig CPU. Se os projetos forem bem-sucedidos, variações futuras do Service64.exe poderão ser lançadas no futuro. Como o malware utiliza susceptabilities de aplicativos de software para contaminar anfitriões alvo, ele pode ser componente de uma co-infecção inseguro com ransomware e também Trojans.
A eliminação de Service64.exe é fortemente recomendada, uma vez que você corre o risco de não só ter grandes custos de energia elétrica se estiver funcionando em seu COMPUTADOR, no entanto, o minerador pode, adicionalmente, realizar outras tarefas indesejáveis nele e também danificar seu COMPUTADOR completamente.
Processo de remoção do Service64.exe
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” botão para remover Service64.exe
Degrau 5. Service64.exe removido!
Guia de vídeo: Como usar o GridinSoft Anti-Malware para remover Service64.exe
Como evitar que o seu PC seja infectado novamente com “Service64.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “Service64.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “Service64.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “Service64.exe”.







