Um novo, vírus minerador de criptomoeda realmente inseguro foi encontrado por pesquisadores de segurança. o malware, chamado Issch.exe podem contaminar vítimas-alvo fazendo uso de uma variedade de maneiras. O ponto principal por trás do minerador Issch.exe é empregar atividades de minerador de criptomoeda nos sistemas de computadores dos destinos para adquirir tokens Monero às custas das vítimas. O resultado final desse mineiro é o aumento das contas de energia elétrica e, se você o deixar por um longo período, o Issch.exe também poderá danificar os elementos do computador..
Issch.exe: Métodos de distribuição
o Issch.exe O malware usa duas abordagens populares que são utilizadas para infectar os alvos do sistema de computador:
- Payload entrega por meio de infecções anteriores. Se um malware Issch.exe mais antigo for lançado nos sistemas de destino, ele poderá se atualizar instantaneamente ou baixar uma versão mais recente.. Isso é possível através do comando de atualização integrado que adquire o release. Isto é feito através da ligação a um servidor controlado por hackers específico predefinido que fornece o código de malware. O vírus baixado e instalado adquirirá o nome de um serviço do Windows e também será colocado no diretório “%% Temp sistema” localização. Edifícios essenciais e arquivos de configuração do sistema operacional são transformados para permitir uma infecção persistente e silenciosa.
- Software exploração de vulnerabilidades Programa. A mais recente variação do malware Issch.exe foi localizada para ser causada por algumas explorações, popularmente entendido por ser feito uso de nos ataques ransomware. As infecções são feitas pelo direccionamento soluções abertas por meio da porta TCP. Os ataques são automatizados por uma estrutura controlada hacker que procura se a porta é aberta. Se essa condição for atendida, certamente verificará a solução e obterá detalhes sobre ela, incluindo qualquer tipo de versão, bem como informações de configuração. Explorações, nome de usuário preferido e também combinações de senhas podem ser feitas. Quando a exploração é activada contra o código vulnerável o mineiro vai certamente ser implantado em adição a porta das traseiras. Isso certamente vai oferecer a uma infecção dupla.
Além dessas técnicas, outras técnicas também podem ser usadas. Os mineiros podem ser dispersos por e-mails de phishing que são enviados por atacado de maneira semelhante a SPAM, além de depender de truques de design social para convencer as vítimas a acreditar que realmente receberam uma mensagem de um serviço ou empresa genuína. Os dados do vírus podem ser anexados diretamente ou inseridos no conteúdo do corpo em material multimídia ou links de mensagens na web.
Os infratores também podem desenvolver páginas de touchdown prejudiciais que podem representar páginas de download de fornecedores, sites de download de aplicativos de software e também outras áreas acessadas com frequência. Quando eles usam um domínio aparentemente comparável a endereços genuínos e também certificações de segurança, os usuários podem ser pressionados a interagir com eles. Em alguns casos simplesmente abri-los pode causar a infecção mineiro.
Outra estratégia seria certamente fazer uso de transportadoras de carga útil que podem se espalhar usando esses métodos ou através de redes de compartilhamento de arquivos, BitTorrent é um dos mais populares. É frequentemente usado para dispersar software e dados legítimos e também piratear material. 2 de um dos provedores de serviços de transporte mais preferidos são os seguintes:
Outros métodos que podem ser levados em consideração pelos criminosos incluem o uso de seqüestradores de navegador da Internet - plugins prejudiciais que são compatíveis com um dos mais populares navegadores da Internet. Eles são enviados aos repositórios relevantes com depoimentos falsos de clientes e credenciais de programador. Muitas vezes os resumos podem incluir screenshots, videoclipes, bem como descrições elaboradas que prometem melhorias fantásticas nas funções e também otimizações de desempenho. No entanto, após a instalação, o comportamento dos navegadores afetados certamente alterará- os clientes certamente descobrirão que serão redirecionados para uma página de touchdown controlada por hackers e que suas configurações poderão ser alteradas – a página inicial padrão, motor de pesquisa da Internet, bem como página de abas novíssimo.
Issch.exe: Análise
O malware Issch.exe é uma situação atemporal de um minerador de criptomoedas que, dependendo de sua configuração, pode desencadear uma variedade de atividades inseguras. Seu principal objetivo é executar tarefas matemáticas complexas que aproveitarão ao máximo as fontes de sistema prontamente disponíveis: CPU, GPU, memória, bem como sala de disco rígido. O modo como eles operam é vinculando-se a um servidor Web exclusivo chamado pool de mineração, onde o código solicitado é baixado. Assim que o download dos trabalhos for iniciado, certamente será iniciado ao mesmo tempo, várias circunstâncias pode ser executado em tão logo. Quando uma tarefa fornecida é concluída, outra será baixada e instalada em seu lugar, e o loop certamente continuará até que o sistema do computador seja desligado, a infecção está se livrado ou mais uma ocasião semelhante acontece. Criptomoeda será atribuído aos controladores criminais (grupo pirataria ou um único hackers) diretamente para suas carteiras.
Uma qualidade perigosa dessa categoria de malware é que exemplos como esse podem consumir todos os recursos do sistema e quase tornar o sistema de computador da vítima inutilizável até que a ameaça seja realmente totalmente eliminada.. A maioria deles inclui uma configuração implacável que os torna realmente difíceis de eliminar. Estes comandos farão modificações também alternativas, documentos de organização e também valores do Registro do Windows que certamente farão com que o malware Issch.exe seja iniciado automaticamente quando o sistema do computador for ligado. O acesso às opções de recuperação de alimentos, bem como às opções, pode ser bloqueado, o que torna inúmeras guias de remoção prática praticamente inúteis.
Esta infecção específica configurará uma solução do Windows para si mesma, foram observadas as conformidades com as análises de segurança e proteção realizadas, em conformidade com as ações.:
. Durante as operações do minerador, o malware vinculado pode se conectar a soluções Windows atualmente em execução e também a aplicativos instalados de terceiros. Ao fazer isso, os administradores de sistema podem não perceber que as toneladas de origem vêm de um procedimento diferente.
| Nome | Issch.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware detectar e remover Issch.exe |
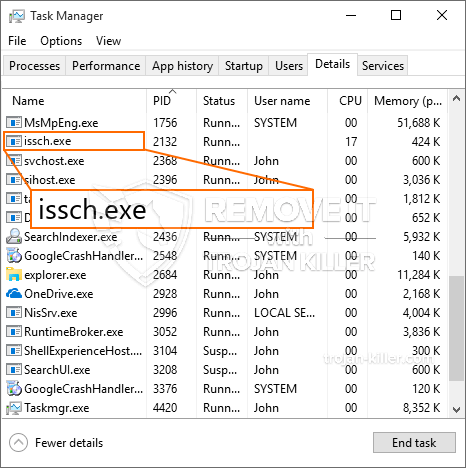
id =”83478″ alinhar =”aligncenter” largura =”600″]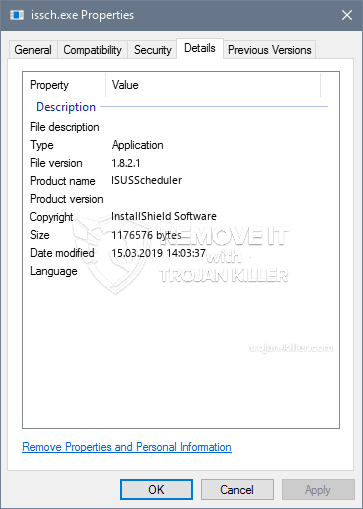 Issch.exe
Issch.exe
Esse tipo de infecção por malware é particularmente eficaz na execução de comandos sofisticados, se configurados. Eles são baseados em uma estrutura modular que permite os controladores criminais para coordenar todos os tipos de ações prejudiciais. Um dos exemplos proeminentes é a alteração do Registro do Windows – alterações nas cordas conectadas pelo sistema operacional podem criar sérios distúrbios de eficiência, além da falta de capacidade de acessar as soluções do Windows. Dependendo da extensão das modificações, ele também pode tornar o sistema do computador totalmente inutilizável.. Por outro lado, a manipulação dos valores do Registro provenientes de qualquer tipo de aplicativo instalado por terceiros pode prejudicá-los.. Alguns aplicativos podem não funcionar completamente, enquanto outros podem parar de funcionar inesperadamente.
Esse minerador específico em sua versão existente está focado na mineração da criptomoeda Monero, incluindo uma variação personalizada do mecanismo de mineração de CPU XMRig. Se as campanhas forem bem-sucedidas, versões futuras do Issch.exe poderão ser introduzidas no futuro. Como o malware faz uso de vulnerabilidades de programas de software para contaminar anfitriões alvo, pode ser parte de uma co-infecção perigosa com ransomware e Trojans.
A eliminação do Issch.exe é altamente recomendada, considerando que você corre o risco de não apenas uma grande conta de energia, se estiver operando no seu PC, mas o mineiro também pode executar outras tarefas indesejadas e também danificar completamente o seu COMPUTADOR.
Processo de remoção de Issch.exe
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” botão para remover Issch.exe
Degrau 5. Issch.exe removido!
Guia de vídeo: Como usar o GridinSoft Anti-Malware para remover Issch.exe
Como evitar que o seu PC seja infectado novamente com “Issch.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “Issch.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “Issch.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “Issch.exe”.