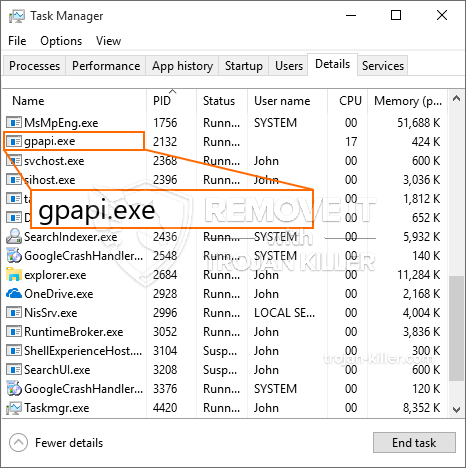
Um novo em folha, infecção muito perigosa criptomoeda mineiro foi detectado por cientistas de segurança. o malware, chamado Gpapi.exe pode infectar vítimas-alvo utilizando uma variedade de maneiras. A essência por trás do mineiro Gpapi.exe é usar tarefas mineiro criptomoeda nos computadores das vítimas, a fim de obter Monero fichas às custas vítimas. O resultado deste mineiro é as despesas de energia elevados e também se você deixá-lo por longos períodos de tempo Gpapi.exe pode até prejudicar seus componentes de sistemas de computador.
Gpapi.exe: Métodos de distribuição
o Gpapi.exe malwares utiliza duas abordagens populares que são usados para infectar alvos de computador:
- Payload Entrega através de infecções anteriores. Se um malwares Gpapi.exe mais velho é implantado nos sistemas de destino pode atualizar-se automaticamente ou baixar uma variação mais recente. Isso é possível utilizando o comando de atualização integrado que obtém a liberação. Isto é feito, anexando a um determinado servidor web controlado por hackers predefinido que dá o código de malware. O vírus baixado terá o nome de uma solução Windows, bem como ser colocada no “%% Temp sistema” Lugar, colocar. propriedades residenciais ou comerciais vitais e também a execução de arquivos de configuração do sistema são transformados de modo a permitir uma infecção implacável e também silenciosa.
- Software exploração de vulnerabilidades Programa. A versão mais atual do malware Gpapi.exe foram realmente descobertos para ser desencadeada pela alguns empreendimentos, amplamente entendido para ser usado nos ataques ransomware. As infecções são feitas por alvo serviços abertos através da porta TCP. As greves são automatizados por um quadro controlado por hackers que olha para cima se a porta está aberta. Se este problema é cumprida ele irá verificar o serviço e recuperar informações sobre ele, constituído por qualquer tipo de variação, bem como dados de configuração. Exploits e proeminentes username e password misturas pode ser feito. Quando o exploit é disparado contra o código vulnerável o mineiro certamente vai ser lançado juntamente com o backdoor. Isto irá apresentar a uma dupla infecção.
Em adição a estas abordagens outros métodos podem ser usados, bem. Mineiros podem ser dispersos por phishing e-mails que são enviados a granel de uma forma SPAM-like e dependem de truques de engenharia social, a fim de confundir os sofredores certo em pensar que eles têm realmente obtido uma mensagem de um serviço legítimo ou negócio. Os dados de infecção pode ser conectado diretamente ou colocar no conteúdo do corpo em conteúdo multimídia ou links da web de mensagens.
Os bandidos também podem desenvolver páginas de destino nocivos que podem representar fornecedor de download de páginas web, sites de download de software e várias outras áreas freqüentemente acessados. Quando usar o domínio que aparece comparável aos endereços legítimos e certificações de proteção os usuários podem ser empurrados para se envolver com eles. Em alguns casos simplesmente abri-los pode causar a infecção mineiro.
Mais uma abordagem seria utilizar portadores de carga que podem ser espalhados utilizando esses métodos ou através de redes de compartilhamento de arquivos, BitTorrent é apenas um dos mais preferidos. Ele é regularmente utilizado para dispersar tanto software respeitável e também documentos e também o conteúdo da web pirata. Dois dos provedores de curso mais populares são os seguintes:
Outras abordagens que podem ser tomadas em consideração pelos infratores consistem em fazer uso do navegador web sequestradores plugins -hazardous que são feitas adequado com os navegadores mais preferidos. Eles são enviados para os bancos de dados apropriados com depoimentos de usuários falsos e credenciais programador. Na maioria dos casos, os resumos podem incluir screenshots, vídeos e também descrições elaboradas a promover a melhoria característica fantástica e otimizações de desempenho. No entanto após a prestação das ações dos navegadores de internet impactadas transformará- os usuários irão descobrir que eles certamente vão ser redirecionado para uma página web pouso controlado por hackers, bem como suas configurações podem ser alteradas – a página inicial padrão, motor de pesquisa da Internet, bem como novas abas página web.

Gpapi.exe: Análise
O malware Gpapi.exe é uma situação tradicional de um mineiro criptomoeda que dependendo de sua configuração pode causar uma ampla gama de atividades prejudiciais. Seu principal objetivo é executar tarefas matemáticas complicadas que farão uso das fontes de sistema prontamente disponíveis: CPU, GPU, memória e também área de disco rígido. A forma como eles trabalham é através da ligação a um servidor chamado única piscina de natação de mineração onde a chamada para o código é baixado e instalar. Assim que uma das tarefas é baixado ele vai ser iniciado de imediato, várias circunstâncias pode ser realizada em tão logo. Quando um determinado trabalho é terminado mais um um será baixado e instalar em seu lugar e também a brecha prosseguirá até que o computador é desligado, a infecção é eliminada ou uma ocasião mais comparável acontece. Criptomoeda será atribuído aos controladores criminais (grupo de hackers ou de um cyberpunk solitária) direto para suas carteiras.
Uma característica prejudicial desta categoria de malware é que as amostras como este pode levar todos os recursos do sistema, bem como praticamente fazer o sistema de computador da vítima inutilizável até que a ameaça foi completamente removido. Muitos deles apresentam uma instalação persistente que torna muito difícil de se livrar de. Estes comandos certamente vai fazer modificações para arrancar escolhas, documentos de instalação, bem como valores de registro do Windows que certamente tornarão o malware Gpapi.exe começar imediatamente uma vez que o sistema de computador está ligado. Acesso a cura seleções de alimentos, bem como escolhas podem ser obstruídas que faz com que muitos hands-on remoção súmulas praticamente inútil.
Este arranjo particular infecção vontade um serviço do Windows por si mesmo, na sequência da análise realizada ther proteção foram observados seguintes ações:
. Durante as operações mineiro o malware conectado pode conectar-se já em execução soluções Windows e aplicativos de terceiros instalados. Ao fazer isso os administradores de sistema podem não descobrir que a carga de recursos provém de um procedimento separado.
| Nome | Gpapi.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware para detectar e remover Gpapi.exe |

Estes tipos de infecções maliciosos são especificamente eficiente em executar comandos avançados se configurado de modo. Eles são baseados em uma estrutura modular que permite aos controladores criminais para gerir todo o tipo de comportamento de risco. Um dos exemplos preferidos é o ajuste do Registro do Windows – cordas alterações relacionadas pelo sistema operacional pode provocar interrupções de desempenho graves e também a falta de serviços de acessibilidade do Windows. Dependendo da extensão de ajustes pode adicionalmente fazer o sistema de computador completamente inutilizável. Por vários outros controle da mão de worths Registro vindo de qualquer terceiro configurar aplicativos podem sabotar-los. Alguns aplicativos podem parar de trabalhar para liberar inteiramente enquanto outros podem de repente parar de trabalhar.
Este mineiro específica na sua actual variação está concentrada na mineração do criptomoeda Monero ter uma versão modificada do motor XMRig mineração CPU. Se os projetos verificar bem sucedido, então as futuras versões do Gpapi.exe pode ser lançado no futuro. Como o malware faz uso de vulnerabilidades de software para infectar hosts de destino, pode ser parte de uma co-infecção inseguro com ransomware e Trojans.
Eliminação de Gpapi.exe é fortemente sugerido, porque você ter a chance de não apenas grandes custos de energia elétrica, se ele está operando no seu computador, mas o mineiro pode ainda fazer outras tarefas indesejáveis sobre ele e também até mesmo danificar o seu computador completamente.
processo de remoção Gpapi.exe
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” botão para remover Gpapi.exe
Degrau 5. Gpapi.exe Removido!
Guia de vídeo: Como usar GridinSoft Anti-Malware para remover Gpapi.exe
Como evitar que o seu PC seja infectado novamente com “Gpapi.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “Gpapi.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “Gpapi.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “Gpapi.exe”.







