Um novo, realmente infecção mineiro criptomoeda inseguro foi descoberto por pesquisadores de proteção. o malware, chamado Emulation.exe pode infectar vítimas-alvo fazendo uso de uma variedade de maneiras. O principal ponto por trás do minerador Emulation.exe é usar as atividades do minerador criptomoeda nos sistemas de computador das vítimas para obter símbolos Monero nos alvos’ despesa. The outcome of this miner is the elevated electricity bills and also if you leave it for longer amount of times Emulation.exe may even damage your computer’s parts.
Emulation.exe: Métodos de distribuição
o Emulation.exe malwares faz uso de 2 métodos proeminentes que são usados para contaminar alvos de computador:
- Payload Entrega via Infecções anteriores. If an older Emulation.exe malware is deployed on the target systems it can instantly update itself or download a more recent version. This is possible by means of the built-in update command which gets the launch. Isto é feito, anexando a um servidor web específico pré-definido controlado por hackers que fornece o código de malware. A infecção baixado e instalar irá adquirir o nome de um serviço do Windows e ser colocado no “%% Temp sistema” Lugar, colocar. Essential properties and running system configuration documents are transformed in order to allow a persistent and also quiet infection.
- Software exploração de vulnerabilidades Programa. The most recent version of the Emulation.exe malware have actually been found to be caused by the some exploits, notoriamente reconhecido por ser feito uso de nos assaltos ransomware. As infecções são feitas por alvo serviços abertos através da porta TCP. Os assaltos são automatizados por uma estrutura controlada hacker que procura se a porta é aberta. If this problem is fulfilled it will certainly scan the solution and obtain details about it, consistindo em qualquer tipo de variação e também dados de configuração. Ventures e combinações de nome de usuário e senha de destaque pode ser feito. When the manipulate is triggered versus the prone code the miner will certainly be released in addition to the backdoor. Isto irá oferecer a uma infecção dupla.
Em adição a estas abordagens outras técnicas podem também ser utilizadas. Miners can be dispersed by phishing emails that are sent out wholesale in a SPAM-like fashion as well as depend upon social engineering methods in order to confuse the sufferers into believing that they have actually received a message from a legitimate solution or business. The infection data can be either straight connected or put in the body components in multimedia content or message links.
The bad guys can also produce destructive touchdown web pages that can pose supplier download web pages, sites de download de software e também outros lugares regularmente acessados. When they make use of comparable seeming domain names to genuine addresses and also safety certificates the individuals may be persuaded right into communicating with them. Em muitos casos, simplesmente abri-los pode ativar a infecção mineiro.
An additional technique would be to make use of payload carriers that can be spread utilizing the above-mentioned techniques or via documents sharing networks, BitTorrent é apenas um dos mais populares. It is regularly utilized to distribute both reputable software as well as data and pirate web content. 2 dos prestadores de serviços de carga útil mais preferidos são os seguintes:
Other techniques that can be taken into consideration by the offenders consist of making use of browser hijackers -dangerous plugins which are made compatible with the most prominent web browsers. They are submitted to the pertinent repositories with phony customer testimonials and also developer qualifications. Em muitos casos, os resumos pode consistir de screenshots, videos and sophisticated summaries appealing excellent feature enhancements as well as performance optimizations. However upon installment the behavior of the affected internet browsers will certainly transform- individuals will locate that they will be rerouted to a hacker-controlled landing page as well as their setups might be changed – a página inicial padrão, motor de pesquisa da Internet e novas guias página web.

Emulation.exe: Análise
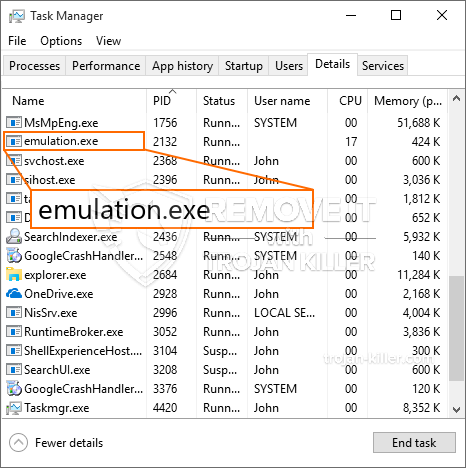
The Emulation.exe malware is a classic situation of a cryptocurrency miner which depending on its arrangement can trigger a wide range of unsafe actions. Its main objective is to execute intricate mathematical tasks that will certainly make use of the readily available system resources: CPU, GPU, memória, bem como espaço no disco rígido. The way they function is by attaching to a special web server called mining swimming pool from where the required code is downloaded and install. Assim como entre os trabalhos é descarregado certamente será iniciado simultaneamente, vários casos pode ser realizada em tão logo. When a provided task is finished another one will be downloaded and install in its area and the loophole will proceed till the computer system is powered off, a infecção é removido ou um evento comparável adicional ocorre. Criptomoeda será recompensado aos controladores criminais (grupo de hackers ou de um cyberpunk solitária) diretamente para os seus orçamentos.
A hazardous feature of this group of malware is that examples such as this one can take all system sources and almost make the sufferer computer unusable till the risk has been entirely gotten rid of. A maioria deles apresentam uma configuração consistente que os torna realmente desafiador para se livrar de. Estes comandos certamente vai fazer ajustes para opções de inicialização, arrangement files as well as Windows Registry values that will make the Emulation.exe malware beginning immediately once the computer is powered on. Access to recovery menus as well as alternatives may be obstructed which renders lots of manual elimination overviews almost useless.
Esta infecção particular, certamente configuração uma solução Windows para si, aderindo ao ther segurança e avaliação de segurança realizada na sequência das acções foram realmente observado:
. Durante os procedimentos mineiro o malware associado pode anexar a já em execução soluções Windows e de terceiros criadas aplicações. Ao fazer isso, os administradores de sistema podem não descobrir que a carga de origem se origina de um procedimento diferente.
| Nome | Emulation.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware to detect and remove Emulation.exe |

These kind of malware infections are specifically reliable at accomplishing sophisticated commands if set up so. They are based upon a modular framework enabling the criminal controllers to manage all kinds of dangerous actions. Um dos exemplos preferidos é a alteração do Registro do Windows – modifications strings related by the operating system can trigger major efficiency disruptions and also the failure to access Windows solutions. Baseando-se na gama de modificações também pode tornar o computador completamente inútil. Por outro lado, a manipulação de valores de registro provenientes de qualquer tipo de aplicativo instalado de terceiros pode sabotá-los. Some applications might fail to introduce entirely while others can unexpectedly stop working.
This specific miner in its current variation is focused on extracting the Monero cryptocurrency consisting of a modified version of XMRig CPU mining engine. If the campaigns show successful then future variations of the Emulation.exe can be introduced in the future. Como o malware utiliza as vulnerabilidades de software para infectar hosts de destino, pode ser parte de uma co-infecção prejudicial com ransomware e também Trojans.
Removal of Emulation.exe is strongly recommended, since you take the chance of not only a large electricity bill if it is running on your COMPUTER, however the miner might additionally execute various other undesirable activities on it and also even damage your COMPUTER permanently.
Emulation.exe removal process
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” button to remove Emulation.exe
Degrau 5. Emulation.exe Removed!
Guia de vídeo: How to use GridinSoft Anti-Malware for remove Emulation.exe
Como evitar que o seu PC seja infectado novamente com “Emulation.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “Emulation.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “Emulation.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “Emulation.exe”.







