Um novo em folha, vírus de minerador de criptomoeda muito perigoso foi identificado por pesquisadores de segurança. o malware, chamado CPUminer_x64_AVX2.exe pode infectar vítimas-alvo, utilizando uma variedade de métodos. A ideia principal por trás do minerador CPUminer_x64_AVX2.exe é utilizar as atividades do minerador de criptomoedas nos sistemas de computador dos sofredores para adquirir símbolos Monero ao custo dos sofredores. The end result of this miner is the elevated electricity expenses as well as if you leave it for longer periods of time CPUminer_x64_AVX2.exe may even damage your computer systems components.
CPUminer_x64_AVX2.exe: Métodos de distribuição
o CPUminer_x64_AVX2.exe malware utilizes two popular techniques which are made use of to infect computer targets:
- Payload Entrega usando Infecções anteriores. If an older CPUminer_x64_AVX2.exe malware is deployed on the target systems it can automatically upgrade itself or download and install a more recent version. Isso é possível por meio do comando de atualização embutido que adquire o lançamento. Isto é feito, anexando a um servidor web em particular predefinido controlado por hackers que dá o código de malware. The downloaded and install infection will certainly obtain the name of a Windows solution as well as be placed in the “%% Temp sistema” Lugar, colocar. Vital residential properties and operating system arrangement data are transformed in order to allow a relentless and silent infection.
- Software exploração de vulnerabilidades Programa. The most current version of the CPUminer_x64_AVX2.exe malware have actually been found to be triggered by the some exploits, comumente entendido para ser usado nos ataques ransomware. As infecções são feitas por alvo serviços abertos usando a porta TCP. Os assaltos são automatizados por um quadro controlado por hackers que procura se a porta é aberta. If this condition is fulfilled it will certainly check the service and also get info concerning it, including any variation and configuration data. Exploits e nome de usuário também preferiu assim como misturas de senha pode ser feito. When the manipulate is triggered versus the prone code the miner will be released together with the backdoor. Isso certamente vai apresentar a uma infecção dupla.
In addition to these approaches various other approaches can be used also. Miners can be dispersed by phishing e-mails that are sent out in bulk in a SPAM-like fashion as well as depend on social engineering methods in order to confuse the targets right into thinking that they have actually received a message from a legit solution or firm. The virus documents can be either straight affixed or placed in the body materials in multimedia web content or text links.
The offenders can likewise produce harmful landing pages that can impersonate vendor download web pages, software application download portals and also various other frequently accessed locations. When they make use of comparable seeming domain names to genuine addresses as well as safety certificates the users might be pushed right into engaging with them. Em alguns casos simplesmente abri-los pode desencadear a infecção mineiro.
One more strategy would certainly be to make use of payload carriers that can be spread out using the above-mentioned methods or through documents sharing networks, BitTorrent é um dos mais populares. It is regularly used to disperse both legitimate software application and documents as well as pirate content. Dois dos portadores distância mais preferidos são os seguintes:
Various other techniques that can be taken into consideration by the wrongdoers include the use of internet browser hijackers -dangerous plugins which are made suitable with the most popular internet browsers. They are posted to the pertinent repositories with phony individual testimonials and developer credentials. Em muitos casos, as descrições pode consistir de screenshots, videos and fancy descriptions encouraging terrific attribute improvements and performance optimizations. Nonetheless upon installment the habits of the impacted internet browsers will certainly alter- customers will certainly find that they will certainly be rerouted to a hacker-controlled touchdown web page as well as their setups might be changed – a página inicial padrão, motor de pesquisa online e página de abas web totalmente nova.

CPUminer_x64_AVX2.exe: Análise
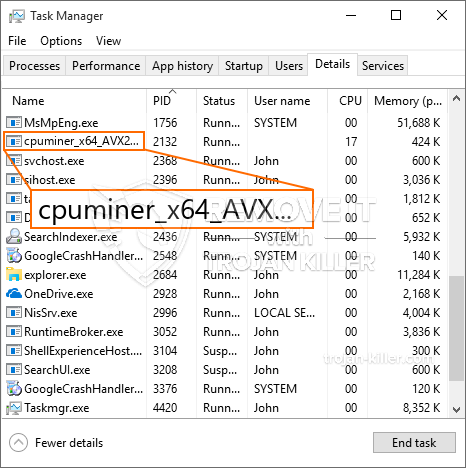
The CPUminer_x64_AVX2.exe malware is a timeless instance of a cryptocurrency miner which relying on its setup can cause a wide array of dangerous actions. Its major objective is to carry out intricate mathematical tasks that will take advantage of the readily available system sources: CPU, GPU, memória e também a área de disco rígido. The way they function is by attaching to an unique web server called mining pool from where the required code is downloaded and install. Assim como entre os trabalhos é descarregado será iniciado simultaneamente, vários casos pode ser executado em quando. When a given job is finished another one will certainly be downloaded and install in its place as well as the loophole will continue until the computer is powered off, a infecção é removida ou uma outra ocasião comparável acontece. Criptomoeda certamente será compensada para os controladores criminais (Hacker equipe ou um único hackers) diretamente para suas carteiras.
An unsafe characteristic of this classification of malware is that samples like this one can take all system sources and almost make the sufferer computer pointless up until the danger has been completely gotten rid of. The majority of them feature a relentless installment which makes them actually tough to remove. Estes comandos certamente vai fazer modificações também alternativas, configuration data and also Windows Registry values that will make the CPUminer_x64_AVX2.exe malware begin immediately once the computer system is powered on. Access to healing food selections and also alternatives might be blocked which makes several hands-on removal overviews virtually useless.
Esta infecção particular, certamente arranjo uma solução Windows para si, adhering to the conducted safety and security evaluation ther following actions have been observed:
. During the miner procedures the linked malware can connect to currently running Windows services and third-party mounted applications. By doing so the system managers may not see that the source tons originates from a separate process.
| Nome | CPUminer_x64_AVX2.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware to detect and remove CPUminer_x64_AVX2.exe |

These sort of malware infections are specifically effective at carrying out sophisticated commands if set up so. They are based on a modular structure permitting the criminal controllers to manage all sort of unsafe habits. Among the preferred instances is the modification of the Windows Registry – adjustments strings connected by the os can trigger major performance disruptions as well as the inability to accessibility Windows services. Depending on the range of adjustments it can additionally make the computer completely unusable. On the various other hand control of Registry values coming from any third-party mounted applications can undermine them. Alguns aplicativos podem não ser totalmente introduzidos, enquanto outros podem parar de funcionar repentinamente.
Este mineiro específico em sua variação existente concentra-se em minar o criptomoeda Monero ter uma variação mudou de XMRig motor de mineração CPU. If the projects confirm successful after that future variations of the CPUminer_x64_AVX2.exe can be released in the future. Como o malware faz uso de programa de software susceptabilities contaminar anfitriões alvo, ele pode ser componente de uma co-infecção prejudicial com ransomware e Trojans.
Elimination of CPUminer_x64_AVX2.exe is highly recommended, because you take the chance of not only a large power bill if it is operating on your PC, yet the miner may also perform various other unwanted tasks on it and also even harm your COMPUTER completely.
CPUminer_x64_AVX2.exe removal process
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” button to remove CPUminer_x64_AVX2.exe
Degrau 5. CPUminer_x64_AVX2.exe Removed!
Guia de vídeo: How to use GridinSoft Anti-Malware for remove CPUminer_x64_AVX2.exe
Como evitar que o seu PC seja infectado novamente com “CPUminer_x64_AVX2.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “CPUminer_x64_AVX2.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “CPUminer_x64_AVX2.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “CPUminer_x64_AVX2.exe”.







