En helt ny, virkelig usikre kryptovaluta miner infeksjonen har blitt identifisert av sikkerhetsforskere. den malware, kalt XmrigDaemon.exe kan smitte målrammede ved å bruke en rekke måter. Hovedpoenget bak XmrigDaemon.exe miner er å ansette kryptovaluta miner oppgaver på datasystemene til sufferers for å få Monero Merker på lider utgifter. The outcome of this miner is the raised electricity bills and if you leave it for longer periods of time XmrigDaemon.exe might also damage your computers components.
XmrigDaemon.exe: distribusjonsmetoder
De XmrigDaemon.exe skadelig benytter to populære teknikk som benyttes for å infisere datamaskinen mål:
- Nyttelast Levering bruke Prior Infeksjoner. If an older XmrigDaemon.exe malware is deployed on the sufferer systems it can automatically update itself or download and install a newer version. Dette er mulig gjennom den integrerte oppgradering kommando som kjøper lansering. Dette gjøres ved å koble til en bestemt forhåndsdefinert hacker styrt server som gir den skadelige koden. Den nedlastede viruset vil få navnet på en Windows-tjeneste samt bli plassert i “%Systemet% temp” område. Vital bygninger og operativsystem arrangement filer er endret for å tillate en nådeløs og stille infeksjon.
- Programvare Utnytter Program for sikkerhetsproblem. The most current variation of the XmrigDaemon.exe malware have been discovered to be brought on by the some ventures, allmenn kjent for å bli anvendt i Ransomware streik. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt ramme som søker ut om porten er åpen. Hvis dette problemet er oppfylt det vil skanne løsningen og hente informasjon om det, bestående av en hvilken som helst variasjon samt oppsett data. Utnytter og populær brukernavn samt passord mikser kan gjøres. Når gjøre bruk av er satt av mot i fare kode miner vil bli lansert i tillegg til bakdør. Dette vil sikkert presentere en dobbelinfeksjon.
Foruten disse fremgangsmåter andre metoder kan benyttes så vel. Gruvearbeidere kan spres ved phishing e-postmeldinger som sendes i bulk i en spam-aktig måte, så vel som avhenger av sosiale designmetoder for å puslespill ofrene akkurat til å tro at de faktisk har fått en melding fra en ekte tjeneste eller selskap. Viruset data kan enten rett festes eller anbringes i kroppen materialene i multimedia webinnhold eller meldingsforbindelser.
Lovbrytere kan også produsere destruktive landing websider som kan etterligne leverandør laste ned og installere websider, program nedlasting nettsteder samt andre ofte brukte steder. Når de bruker likelydende domene til ekte adresser samt sikkerhet sertifiseringer enkeltpersoner kan bli tvunget til å engasjere med dem. I noen tilfeller rett og slett å åpne dem kan aktivere miner infeksjon.
En annen strategi ville sikkert være å bruke hale tjenesteytere som kan være spredt ut utnytte de nærmer eller via fildelingsnettverk, BitTorrent er bare ett av de mest fremtredende. Det er ofte brukt til å spre både legit programvare og data, og også pirat webinnhold. To av de mest populære hale leverandører er følgende:
Diverse andre tilnærminger som kan være tenkt av skurkene består av bruk av internett browser hijackers -unsafe plugins som er laget kompatibel med en av de mest fremtredende web nettlesere. De er sendt til de aktuelle repositories med falske kunder og også utviklerlegitimasjoner. I de fleste tilfeller oppsummeringer kan inkludere skjermbilder, videoer samt intrikate beskrivelser tiltalende gode funksjonsforbedringer samt effektivitet optimaliseringer. Men ved avdrag handlingene påvirket nettlesere vil endre- individer vil sikkert finne at de vil sikkert bli omdirigert til en hacker-kontrollert landing nettside og også deres oppsett kan bli endret – standard startside, søkemotor og nye faner nettside.

XmrigDaemon.exe: Analyse
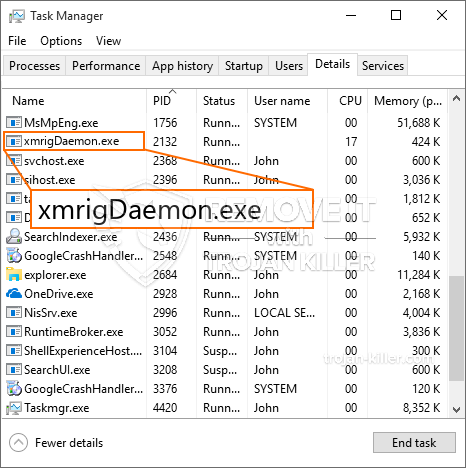
The XmrigDaemon.exe malware is a classic situation of a cryptocurrency miner which depending on its arrangement can cause a variety of unsafe activities. Its major goal is to perform complicated mathematical tasks that will certainly capitalize on the readily available system resources: prosessor, GPU, minne og også harddisk område. The method they work is by connecting to an unique server called mining pool from where the called for code is downloaded and install. Så raskt som blant oppgavene blir lastet ned vil det bli startet på en gang, flere tilfeller kan være borte for en gangs skyld. When a given job is completed one more one will be downloaded in its location and also the loop will proceed till the computer system is powered off, infeksjonen fjernes eller et ytterligere tilsvarende hendelse skjer. Kryptovaluta vil sikkert bli belønnet til de kriminelle kontrollerne (hacking gruppe eller en enslig cyberpunk) direkte til sine lommebøker.
A harmful quality of this classification of malware is that examples like this one can take all system sources and practically make the victim computer system unusable until the threat has been totally eliminated. A lot of them feature a consistent installation which makes them really difficult to remove. Disse kommandoene vil sikkert gjøre endringer i oppstartsvalg, configuration data as well as Windows Registry values that will make the XmrigDaemon.exe malware beginning automatically once the computer system is powered on. Accessibility to healing food selections and options may be blocked which renders lots of hand-operated elimination guides almost ineffective.
Denne spesifikke infeksjonen vil sikkert arrangere en Windows-løsning for seg selv, adhering to the carried out security analysis ther following actions have been observed:
. During the miner procedures the associated malware can hook up to already running Windows solutions and also third-party installed applications. By doing so the system administrators might not see that the source load comes from a different procedure.
| Navn | XmrigDaemon.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove XmrigDaemon.exe |

Disse slags malware infeksjoner er spesielt effektiv til å utføre innovative kommandoer hvis satt opp slik at. They are based on a modular structure enabling the criminal controllers to manage all type of hazardous habits. Blant de populære forekomster er endring av Windows-registeret – alterations strings associated by the operating system can create severe efficiency disturbances and the inability to accessibility Windows services. Depending upon the range of changes it can additionally make the computer system totally unusable. På den annen side kan manipulering av registerverdier som kommer fra alle slags tredjepartsoppsettprogrammer sabotere dem. Some applications may fall short to launch entirely while others can suddenly stop working.
This specific miner in its current version is focused on extracting the Monero cryptocurrency including a changed variation of XMRig CPU mining engine. If the campaigns verify successful after that future versions of the XmrigDaemon.exe can be launched in the future. Som malware benytter programvare susceptabilities forurense målet verter, det kan være bestanddel av en farlig samtidig infeksjon med ransomware og også trojanere.
Elimination of XmrigDaemon.exe is highly recommended, considering that you risk not only a large electrical energy costs if it is running on your PC, yet the miner may also carry out various other unwanted activities on it and also damage your COMPUTER permanently.
XmrigDaemon.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove XmrigDaemon.exe
SKRITT 5. XmrigDaemon.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove XmrigDaemon.exe
Hvor å forhindre din PC blir infisert med “XmrigDaemon.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “XmrigDaemon.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “XmrigDaemon.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “XmrigDaemon.exe”.







