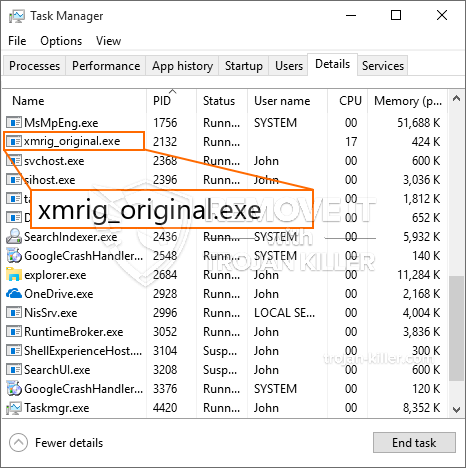
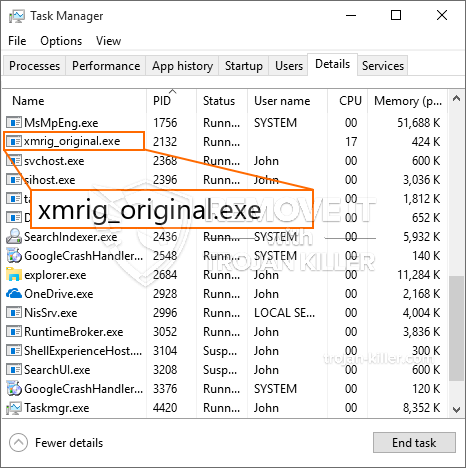
En helt ny, veldig farlig kryptovaluta miner virus har blitt funnet av sikkerhetsforskere. den malware, kalt Xmrig_original.exe kan forurense target lider benytter et utvalg av fremgangsmåter. Hovedideen bak Xmrig_original.exe miner er å bruke kryptovaluta miner oppgaver på datamaskinene til ofrene for å tilegne seg Monero symboler på mål bekostning. The outcome of this miner is the raised electrical energy bills as well as if you leave it for longer periods of time Xmrig_original.exe may even damage your computers elements.
Xmrig_original.exe: distribusjonsmetoder
De Xmrig_original.exe Fjern News-kotofa.cc Vis varsler:
- Nyttelast Levering via Tidligere infeksjoner. If an older Xmrig_original.exe malware is deployed on the target systems it can automatically upgrade itself or download a more recent version. Dette er mulig ved hjelp av den integrerte oppgraderingskommandoen som henter utgivelsen. Dette gjøres ved å knytte til en bestemt forhåndsdefinert hacker-kontrollert webserver som gir skadelig programvare-kode. Den nedlastede og installerte infeksjonen vil skaffe seg navnet på en Windows-løsning, samt være plassert i “%Systemet% temp” sted. Vitale boligeiendommer og operativsystemfiler blir transformert for å tillate en nådeløs og også stille infeksjon.
- Programvare Utnytter Program for sikkerhetsproblem. The latest variation of the Xmrig_original.exe malware have been found to be caused by the some exploits, populært kjent for å bli brukt i løsepengevarestreikene. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt rammeverk som vender opp om porten er åpen. Hvis dette problemet er oppfylt, vil det sjekke tjenesten og også få informasjon om det, bestående av en versjon samt konfigurasjonsdata. Utnytter og foretrukne brukernavn samt passord kombinasjoner kan gjøres. Når manipulasjonen er aktivert mot den sårbare koden, vil gruvearbeideren sikkert bli løslatt sammen med bakdøren. Dette vil gi den en dobbel infeksjon.
Bortsett fra disse teknikkene kan andre strategier også benyttes. Gruvearbeidere kan bli spredt ved phishing-e-poster som sendes i bulk på en SPAM-lignende måte, samt stole på sosiale ingeniørmetoder for å forvirre de lidende rett til å tro at de faktisk har fått en melding fra en legitim tjeneste eller et selskap. Gruvearbeidere kan bli spredt ved phishing-e-poster som sendes i bulk på en SPAM-lignende måte, samt stole på sosiale ingeniørmetoder for å forvirre de lidende rett til å tro at de faktisk har fått en melding fra en legitim tjeneste eller et selskap.
Gruvearbeidere kan bli spredt ved phishing-e-poster som sendes i bulk på en SPAM-lignende måte, samt stole på sosiale ingeniørmetoder for å forvirre de lidende rett til å tro at de faktisk har fått en melding fra en legitim tjeneste eller et selskap, program nedlastingsportaler samt diverse andre ofte tilgang til steder. Gruvearbeidere kan bli spredt ved phishing-e-poster som sendes i bulk på en SPAM-lignende måte, samt stole på sosiale ingeniørmetoder for å forvirre de lidende rett til å tro at de faktisk har fått en melding fra en legitim tjeneste eller et selskap. I mange tilfeller rett og slett å åpne dem kan utløse miner infeksjon.
En annen teknikk ville være å bruke nyttelasttjenesteleverandører som kan spres ved hjelp av disse tilnærmingene eller via datadelingsnettverk, BitTorrent er blant de mest fremtredende. Det brukes regelmessig til å spre både legitime programvareapplikasjoner så vel som filer så vel som piratmateriale. To av en av de mest foretrukne leverandørene av nyttelasttjenester er følgende:
Ulike andre tilnærminger som kan vurderes av lovbryterne består i å bruke nettleserkaprere - farlige plugins som er gjort egnet med en av de mest fremtredende nettleserne. De blir lagt ut i de relevante databasene med falske kundeanbefalinger og også designerlegitimasjon. Ofte sammendragene kan bestå av skjermbilder, videoklipp samt forseggjorte oppsummeringer tiltalende fantastiske attributtforbedringer samt ytelsesoptimaliseringer. Likevel vil handlingene til de berørte nettleserne endres ved installasjon- enkeltpersoner vil finne at de vil bli omdirigert til en hackerkontrollert landingsside, og oppsettene deres kan også bli endret – standard nettside, søkemotor og også splitter nye faner nettside.
Xmrig_original.exe: Analyse
The Xmrig_original.exe malware is a classic case of a cryptocurrency miner which relying on its configuration can create a wide array of hazardous actions. Its main objective is to execute intricate mathematical tasks that will make the most of the readily available system sources: prosessor, GPU, minne og også plass på harddisken. The means they function is by connecting to an unique web server called mining swimming pool where the required code is downloaded and install. Så snart blant oppgavene blir lastet det vil bli startet på samme tid, flere forhold kan være borte for en gangs skyld. When an offered job is completed an additional one will certainly be downloaded and install in its place as well as the loop will proceed up until the computer system is powered off, infeksjonen blir kvitt eller en annen sammenlignbar anledning oppstår. Kryptovaluta vil sikkert bli kompensert for den kriminelle kontrollerne (hacking gruppe eller en enkelt hackere) direkte til sine budsjetter.
A hazardous feature of this group of malware is that examples similar to this one can take all system resources as well as practically make the sufferer computer unusable till the danger has actually been totally gotten rid of. Most of them feature a relentless installation that makes them truly tough to remove. Disse kommandoene vil gjøre endringer for å starte opp valg, arrangement documents and Windows Registry values that will make the Xmrig_original.exe malware beginning instantly as soon as the computer is powered on. Access to healing food selections as well as alternatives might be blocked which makes numerous hand-operated removal guides almost pointless.
Denne spesifikke infeksjonen vil sikkert konfigurasjons en Windows-tjeneste for seg selv, complying with the performed safety evaluation ther following activities have actually been observed:
During the miner procedures the linked malware can attach to currently running Windows services and also third-party set up applications. By doing so the system administrators may not observe that the source lots originates from a different procedure.
| Navn | Xmrig_original.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Xmrig_original.exe |

Disse type skadelige infeksjoner er særlig effektive til å utføre sofistikerte kommandoer om å sette opp så. De er basert på en modulær struktur gjør det mulig for kriminelle kontrollere for å administrere alle typer usikre handlinger. Blant de foretrukne eksempler er endring av Windows-registeret – justeringer strenger forbundet med os kan utløse betydelige ytelses avbrudd og også manglende evne til å få tilgang til Windows-løsninger. Stole på rekke justeringer kan det også gjøre datasystemet helt ubrukelig. På den annen side justering av register worths kommer fra tredjeparts installerte programmer kan sabotere dem. Noen programmer kan unnlate å lansere helt, mens andre kan plutselig slutte arbeids.
Denne spesifikke miner i sin nåværende versjon er fokusert på gruvedrift Monero kryptovaluta består av en endret variant av XMRig CPU gruvedrift motor. If the campaigns confirm effective then future versions of the Xmrig_original.exe can be introduced in the future. Som malware gjør bruk av programvare susceptabilities å forurense målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Removal of Xmrig_original.exe is highly advised, fordi du risikerer ikke bare en stor strøm regning hvis det kjører på datamaskinen, men miner kan i tillegg gjøre andre uønskede oppgaver på det, så vel som med skade datamaskinen helt.
Xmrig_original.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Xmrig_original.exe
SKRITT 5. Xmrig_original.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Xmrig_original.exe
Hvor å forhindre din PC blir infisert med “Xmrig_original.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Xmrig_original.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Xmrig_original.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Xmrig_original.exe”.







