En helt ny, virkelig usikre kryptovaluta miner infeksjon har blitt oppdaget av sikkerhetsforskere. den malware, kalt Vmicsvc.exe kan forurense målpasienter på forskjellige måter. Essensen bak Vmicsvc.exe miner er å bruke kryptovaluta miner oppgaver på datamaskinene til ofre for å få Monero tokens på ofrene kostnads. Resultatet av denne gruvearbeideren er de økte elektriske energikostnadene, og også hvis du lar den stå over lengre tid kan Vmicsvc.exe også skade datamaskinens deler.
Bortsett fra disse tilnærmingene kan andre metoder også brukes. Gruvearbeidere kan spre seg gjennom phishing-e-postmeldinger som sendes ut på engros på en spam-lignende måte, samt stole på sosiale designteknikker for å forvirre ofrene til å tro at de har fått en melding fra en ekte løsning eller et selskap. Virusdokumentene kan enten kobles direkte til eller plasseres i kroppsmaterialet i multimediemateriale eller meldingsnettkoblinger.
Lovbryterne kan på samme måte utvikle destruktive destinasjonssider som kan etterligne nedlasting og installering av websider fra leverandører, nedlasting av portaler og forskjellige andre steder du ofte får tilgang til. Når de bruker lignende tilsynelatende domene til legitime adresser og også sikkerhetssertifikater, kan brukerne bli overtalt til å kommunisere med dem. Noen ganger kan bare å åpne dem utløse minerinfeksjonen.
En annen strategi ville være å bruke transportleverandører som kan spres ut ved å bruke ovennevnte metoder eller ved hjelp av fildelingsnettverk, BitTorrent er bare en av de mest foretrukne. Det blir ofte brukt til å distribuere både legitim programvare og data og også piratinnhold. To av en av de mest fremtredende nyttelast leverandører er følgende:
Andre teknikker som kan vurderes av de som gjør urett, inkluderer bruk av nettleserkaprere -usikre plugins som er gjort kompatible med de mest fremtredende nettleserne. De blir publisert til de aktuelle depotene med falske kundeanmeldelser i tillegg til designerkvalifikasjoner. I mange tilfeller sammendragene kan bestå av skjermbilder, videoklipp og flotte sammendrag som lover gode funksjonsforbedringer samt effektivitetsoptimaliseringer. Likevel vil vanene til de berørte nettleserne helt sikkert endre seg etter installasjonen- enkeltpersoner vil finne ut at de sikkert vil bli omdirigert til en hacker-kontrollert destinasjonsside, og deres oppsett kan endres – standard startside, internett søkemotor samt nye faner nettside.

Vmicsvc.exe: Analyse
Vmicsvc.exe -skadelig programvare er et klassisk tilfelle av en kryptovaluta -gruvearbeider, som avhengig av oppsettet kan skape et bredt spekter av farlige aktiviteter. Hovedmålet er å utføre intrikate matematiske jobber som vil dra nytte av de lett tilgjengelige systemressursene: prosessor, GPU, minne og også harddisk plass. Midlene de jobber er ved å koble til en unik server som kalles gruvebasseng der den nødvendige koden lastes ned og installeres. Så raskt som blant jobbene blir lastet ned, vil den absolutt startes med en gang, flere tilfeller kan være borte for en gangs skyld. Når en tilbudt jobb er fullført, vil en ekstra en helt sikkert bli lastet ned og installere i området, og smutthullet vil sikkert fortsette til datamaskinsystemet er slått av., infeksjonen er fjernet eller en annen lignende hendelse skjer. Kryptovaluta vil sikkert deles ut til de kriminelle kontrollerne (hacking team eller en enkelt hacker) rett til sine lommebøker.
Et usikkert trekk ved denne klassifiseringen av skadelig programvare er at eksempler som ligner på denne kan ta alle systemkilder og også nesten gjøre måldatasystemet ubrukelig frem til risikoen er fullstendig fjernet. Flertallet av dem inkluderer et vedvarende oppsett som gjør dem virkelig vanskelige å fjerne. Disse kommandoene vil gjøre endringer for alternativer, oppsettdata og Windows -registerverdier som får Vmicsvc.exe -skadelig programvare til å starte umiddelbart når datamaskinen slås på. Tilgang til utvinning av matvalg og alternativer kan hindres, noe som gjør mange hånddrevne eliminasjonsoversikter praktisk talt ineffektive.
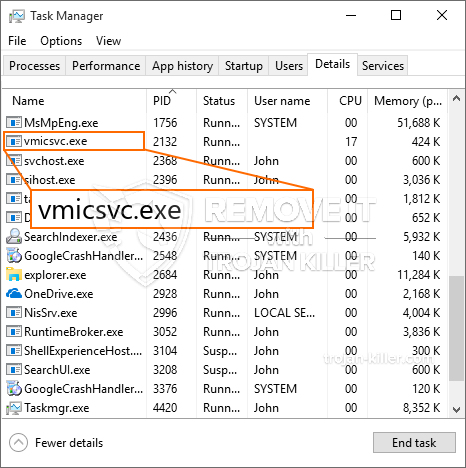
Denne spesifikke infeksjonen vil ordningen en Windows-tjeneste for seg selv, etter utført sikkerhetsanalyse er følgende handlinger blitt observert:
. Under gruveprosedyrene kan den tilknyttede malware lenke til Windows-tjenester som for øyeblikket kjører, og også installerte applikasjoner fra tredjeparter. Ved å gjøre det kan det hende at systemansvarlige ikke observerer at kildebelastningen stammer fra en egen prosedyre.
| Navn | Vmicsvc.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Vmicsvc.exe |

Denne typen malwareinfeksjoner er spesielt pålitelige for å utføre innovative kommandoer hvis de er konfigurert. De er basert på en modulær struktur som gjør at kriminelle kontrollører kan håndtere alle typer skadelig oppførsel. En av de fremtredende tilfeller er endring av Windows-registeret – modifikasjonsstrenger som er koblet til av operativsystemet, kan skape alvorlige ytelsesforstyrrelser og manglende tilgang til Windows -løsninger. Avhengig av omfanget av endringer kan det på samme måte gjøre datasystemet helt meningsløst. På den annen side kan manipulering av registerverdier som tilhører tredjeparts installerte applikasjoner undergrave dem. Noen programmer kan slutte å virke til å lansere helt mens andre kan plutselig slutte å fungere.
Denne bestemte gruvearbeideren i sin nåværende versjon er konsentrert om gruvedrift av Monero -kryptokurrency med en tilpasset versjon av XMRig CPU -gruvedrift. Hvis prosjektene viser effekt etter at fremtidige versjoner av Vmicsvc.exe kan bli utgitt i fremtiden. Som malware benytter program susceptabilities å infisere målet verter, det kan være en del av en usikker samtidig infeksjon med ransomware og også trojanere.
Eliminering av Vmicsvc.exe anbefales på det sterkeste, fordi du risikerer ikke bare en stor strømregning hvis den fungerer på PCen, men gruvearbeideren kan også utføre andre uønskede oppgaver på den og også skade PCen permanent.
Vmicsvc.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” -knappen for å fjerne Vmicsvc.exe
SKRITT 5. Vmicsvc.exe fjernet!
video guide: Slik bruker du GridinSoft Anti-Malware for å fjerne Vmicsvc.exe
Hvor å forhindre din PC blir infisert med “Vmicsvc.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Vmicsvc.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Vmicsvc.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Vmicsvc.exe”.







