En helt ny, veldig farlig kryptovaluta miner infeksjon har blitt oppdaget av sikkerhetsforskere. den malware, kalt Sysupdater.exe kan forurense målet ofrene å gjøre bruk av en rekke virkemidler. Essensen bak Sysupdater.exe-gruvearbeideren er å bruke kryptovalutaoppgavearbeid på datamaskinsystemene til pasienter for å få Monero-tokens på ofrenes bekostning. The end result of this miner is the elevated electrical power costs and if you leave it for longer periods of time Sysupdater.exe may even damage your computers elements.
Sysupdater.exe: distribusjonsmetoder
De Sysupdater.exe malware bruksområder 2 popular methods which are utilized to contaminate computer system targets:
- Nyttelast Levering via Tidligere infeksjoner. If an older Sysupdater.exe malware is released on the victim systems it can automatically update itself or download a more recent version. Dette er mulig ved hjelp av den integrerte oppdatert kommando som overtar utskytnings. This is done by attaching to a specific predefined hacker-controlled server which provides the malware code. The downloaded virus will obtain the name of a Windows solution and be positioned in the “%Systemet% temp” sted. Vital properties and running system configuration files are transformed in order to allow a consistent and quiet infection.
- Utnytter programvare for sikkerhetsproblem. The most current version of the Sysupdater.exe malware have actually been discovered to be triggered by the some exploits, populært forstått til å bli gjort bruk av i ransomware streik. Infeksjonene er gjort ved å målrette åpne løsninger via TCP-port. Angrepene er automatiserte av hackere styrt ramme som søker ut om porten er åpen. If this problem is met it will scan the service as well as retrieve details about it, including any variation and also configuration information. Ventures and also popular username and also password combinations might be done. When the exploit is activated against the at risk code the miner will be released along with the backdoor. Dette vil gi den en dual-smitte.
In addition to these approaches other strategies can be utilized also. Miners can be distributed by phishing emails that are sent out wholesale in a SPAM-like manner and also depend upon social engineering techniques in order to puzzle the victims right into believing that they have actually gotten a message from a legitimate service or firm. The virus data can be either directly attached or put in the body contents in multimedia web content or message links.
The criminals can additionally produce harmful landing web pages that can impersonate supplier download and install pages, software download portals as well as various other frequently accessed locations. When they make use of comparable appearing domain names to legitimate addresses and also safety and security certifications the users may be persuaded into communicating with them. Noen ganger bare åpne dem kan sette av miner infeksjon.
One more approach would certainly be to utilize haul carriers that can be spread using the above-mentioned techniques or via documents sharing networks, BitTorrent er en av de mest populære. It is frequently utilized to distribute both genuine software application and also data and pirate content. 2 av en av de mest fremtredende nyttelast leverandører er følgende:
Other approaches that can be considered by the crooks include using browser hijackers -hazardous plugins which are made suitable with the most preferred internet browsers. They are uploaded to the appropriate repositories with fake individual testimonials as well as designer qualifications. Ofte sammendragene kan bestå av skjerm, videos and sophisticated descriptions encouraging excellent feature improvements and efficiency optimizations. Likevel på oppsett oppførselen til de berørte nettlesere vil endre- individuals will find that they will certainly be rerouted to a hacker-controlled landing page and their setups might be altered – standard nettside, online søkemotor og nye faner nettside.

Sysupdater.exe: Analyse
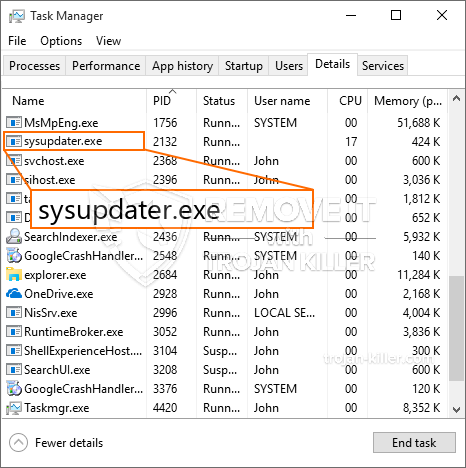
The Sysupdater.exe malware is a timeless situation of a cryptocurrency miner which depending on its setup can trigger a wide array of dangerous activities. Dets primære mål er å utføre kompliserte matematiske oppgaver som vil dra nytte av de tilgjengelige systemkildene: prosessor, GPU, minne, så vel som harddiskplass. Midlene de opererer er ved å koble til en spesiell server som heter mining pool, hvor den nødvendige koden lastes ned og installeres. Så snart en av jobbene er lastet ned, vil den helt sikkert bli startet på en gang, flere forekomster kan utføres så snart som. Når en tilbudt jobb er ferdig vil en til bli lastet ned og installert i området, så vel som smutthullet fortsetter til datasystemet er slått av, infeksjonen fjernes eller en lignende hendelse inntreffer. Kryptovaluta vil bli belønnet til de kriminelle kontrollerne (hacking gruppe eller en enkelt cyberpunk) rett til sine lommebøker.
Et farlig kjennetegn ved denne kategorien skadelig programvare er at prøver som denne kan ta alle systemkilder og praktisk talt gjøre det lidende datasystemet meningsløst til risikoen faktisk har blitt fullstendig eliminert. De fleste av dem har et konsistent oppsett som gjør dem virkelig utfordrende å fjerne. Disse kommandoene vil sikkert gjøre justeringer i oppstartsalternativer, setup files and also Windows Registry values that will certainly make the Sysupdater.exe malware begin automatically as soon as the computer system is powered on. Tilgjengeligheten til gjenopprettingsmenyer og alternativer kan hindres, noe som gjør mange praktiske eliminasjonsveiledninger nesten ubrukelige.
Denne spesifikke infeksjonen vil konfigurere en Windows-løsning for seg selv, i samsvar med den gjennomførte sikkerhetsevalueringen har følgende handlinger blitt observert:
. Under gruveprosedyrene kan den tilknyttede skadelig programvaren koble til Windows-tjenester og tredjeparts konfigureringsprogrammer som for øyeblikket kjøres. Ved å gjøre det kan det hende at systemansvarlige ikke ser at ressurspartiene kommer fra en egen prosess.
| Navn | Sysupdater.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Sysupdater.exe |

Disse slags skadelige infeksjoner er spesielt effektive ved utførelse av innovative kommandoer hvis konfigurert så. They are based upon a modular framework enabling the criminal controllers to manage all type of dangerous behavior. Blant de populære forekomster er endring av Windows-registeret – alterations strings associated by the operating system can create significant efficiency disruptions and also the inability to access Windows solutions. Depending upon the range of modifications it can likewise make the computer system completely pointless. On the various other hand control of Registry values coming from any kind of third-party set up applications can sabotage them. Noen applikasjoner kan komme til å slippe helt, mens andre plutselig kan slutte å jobbe.
This certain miner in its current version is concentrated on extracting the Monero cryptocurrency having a changed variation of XMRig CPU mining engine. If the campaigns confirm effective then future versions of the Sysupdater.exe can be launched in the future. Som malware bruker programvare sårbarheter forurense målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware og også trojanere.
Removal of Sysupdater.exe is strongly suggested, because you risk not only a big electrical power expense if it is running on your PC, however the miner may additionally do other undesirable activities on it and also damage your COMPUTER completely.
Sysupdater.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Sysupdater.exe
SKRITT 5. Sysupdater.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Sysupdater.exe
Hvor å forhindre din PC blir infisert med “Sysupdater.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Sysupdater.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Sysupdater.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Sysupdater.exe”.







