En ny, veldig skadelig kryptovaluta miner viruset har blitt identifisert av beskyttelse forskere. den malware, kalt Ntdll.exe kan smitte mot målgrupper ved bruk av en rekke metoder. Hovedpoenget bak Ntdll.exe miner er å bruke kryptovaluta miner oppgaver på datasystemene til mål for å få Monero Merker på mål utgifter. Resultatet av denne gruvearbeideren er de økte utgiftene til elektrisk strøm, så vel som om du lar det ligge lenger tid Ntdll.exe kan til og med skade datamaskinens komponenter.
Ntdll.exe: distribusjonsmetoder
De Ntdll.exe malware bruker to populære metoder som brukes til å forurense datamål:
- Nyttelast Levering bruke Prior Infeksjoner. Hvis en eldre Ntdll.exe-malware blir utgitt på offersystemene, kan den umiddelbart oppgradere seg selv eller laste ned en nyere versjon. Dette er mulig å bruke den integrerte oppgraderingskommandoen som oppnår lanseringen. Dette gjøres ved å koble til en spesifikk forhåndsdefinert hacker-kontrollert server som gir malware-koden. Den nedlastede infeksjonen vil sikkert skaffe seg navnet på en Windows-tjeneste og bli lagt inn i “%Systemet% temp” plassering. Viktige bolig- eller kommersielle eiendommer og også kjørende systemkonfigurasjonsdokumenter endres for å tillate en jevn og rolig infeksjon.
- Programvare Utnytter Søknad om sikkerhetsproblemene. Den nyeste varianten av Ntdll.exe-malware har faktisk blitt lokalisert for å bli utløst av noen ventures, ofte kjent for å bli brukt i ransomware-angrep. Infeksjoner er gjort ved å målrette åpne løsninger gjennom TCP-port. Angrepene er automatiserte av hackere styrt rammeverk som søker etter om porten er åpen. Hvis dette problemet er oppfylt, vil det sikkert sjekke løsningen og hente informasjon om det, inkludert en hvilken som helst versjon, og også konfigurasjonsdataene. Utnytter samt foretrukne brukernavn og også passord kombinasjoner kan gjøres. Når manipulasjonen er forårsaket kontra risikokoden, blir gruvearbeideren løslatt sammen med bakdøren. Dette vil sikkert presentere en dobbelinfeksjon.
Bortsett fra disse tilnærmingene kan andre strategier også brukes. Gruvearbeidere kan distribueres ved phishing-e-post som sendes i bulk på en SPAM-lignende måte og er også avhengige av sosialtekniske metoder for å pusle opp målene til å tro at de har fått en melding fra en ekte løsning eller firma. Virusdataene kan enten rett festes eller settes inn i kroppens innhold i multimedia webinnhold eller tekstnettlenker.
De skurkene kan på samme måte lage ødeleggende touchdown-sider som kan forestille seg at leverandøren laster ned og installerer sider, programvare last ned portaler og andre ofte tilgjengelige områder. Når de bruker lignende domene til ekte adresser og også sikkerhetssertifiseringer, kan individene overtales rett til å kommunisere med dem.. I noen tilfeller rett og slett å åpne dem kan aktivere miner infeksjon.
En strategi til er å bruke tilbydere av transporttjenester som kan spres ut ved hjelp av disse metodene eller ved bruk av delingsnettverk, BitTorrent er en av de mest foretrukne seg. Det brukes jevnlig til å spre både legit programvare så vel som dokumenter og piratinnhold. To av de mest foretrukne trekkbærere er følgende:
Andre metoder som lovbryterne kan tenke på, inkluderer bruk av nettleserkaprere - farlige plugins som er gjort kompatible med de mest fremtredende nettleserne.. De lastes opp til de aktuelle depotene med falske brukeranmeldelser og utviklerkvalifikasjoner. I de fleste tilfeller oppsummeringer kan bestå av skjermbilder, videoer og kompliserte beskrivelser som appellerer til fantastiske funksjonsforbedringer og ytelsesoptimaliseringer. Likevel ved avbetaling vil oppførselen til de påvirkede nettleserne absolutt forandre seg- brukere vil sikkert finne at de sikkert vil bli omdirigert til en hacker-kontrollert destinasjonswebside og innstillingene deres kan bli endret – standard startside, søkemotor så vel som splitter ny faneside.

Ntdll.exe: Analyse
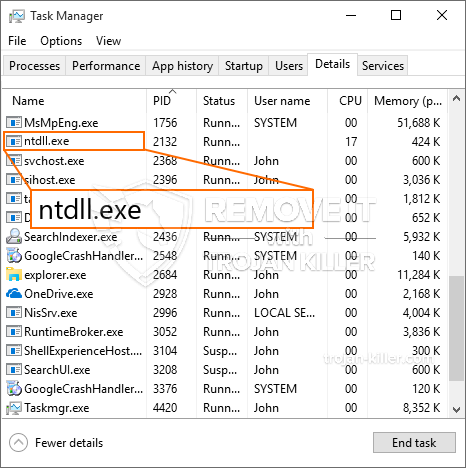
Ntdll.exe-malware er et klassisk eksempel på en cryptocurrency-gruvearbeider, som avhengig av ordningen kan skape et bredt spekter av farlige aktiviteter. Hovedmålet er å utføre kompliserte matematiske oppgaver som sikkert vil utnytte de tilbudte systemressursene: prosessor, GPU, minne og harddisk plass. Måten de fungerer på er ved å koble til en unik webserver som heter mining pool, hvor den etterlyste koden lastes ned og installeres. Så raskt som en av oppgavene lastes ned, vil den absolutt bli startet samtidig, flere forekomster kan utføres på en gang. Når en gitt oppgave er fullført, vil en ekstra lastes ned og installeres i området, og løkken fortsetter også til datamaskinen er slått av, infeksjonen er eliminert eller et ytterligere tilsvarende hendelse skjer. Kryptovaluta vil bli belønnet til de kriminelle kontrollerne (hacking gruppe eller en enkelt hackere) direkte til sine lommebøker.
En utrygg funksjon i denne kategorien skadelig programvare er at eksempler som denne kan ta alle systemkilder og også praktisk talt gjøre måldatasystemet meningsløst til risikoen faktisk har blitt fullstendig eliminert. De fleste av dem har et nådeløst oppsett som gjør dem faktisk vanskelig å eliminere. Disse kommandoene vil sikkert gjøre justeringer også opsjoner, konfigurasjonsdokumenter og Windows-registerverdier som sikkert vil føre til at Ntdll.exe-skadelig programvare starter umiddelbart så snart datamaskinen er slått på. Tilgang til valg av helbredende mat og alternativer kan hindres, noe som gir mange håndopererte fjerningsveiledninger tilnærmet meningsløse.
Denne visse infeksjonen vil sikkert konfigurere en Windows-løsning for seg selv, å overholde den utførte sikkerhets- og sikkerhetsanalysen som faktisk ble overholdt aktiviteter:
. Under gruveprosedyrene kan den tilknyttede skadelige programvaren knyttes til allerede kjørte Windows-tjenester og tredjepartsmonterte applikasjoner. Ved å gjøre det kan det hende at systemansvarlige ikke ser at ressurspartiene stammer fra en annen prosess.
| Navn | Ntdll.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Ntdll.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på et modulært rammeverk som gjør det mulig for kriminelle kontrollører å orkestrere alle slags skadelige handlinger. Blant de populære tilfellene er justeringen av Windows-registeret – endringstrenger som er koblet av operativsystemet, kan forårsake betydelige ytelsesforstyrrelser så vel som mangelen på tilgjengelighet Windows-tjenester. Avhengig av omfanget av modifikasjoner kan det i tillegg gjøre datasystemet helt ubrukelig. På den annen side kan justering av registerverdier fra tredjeparts konfigurerte applikasjoner sabotere dem. Noen programmer kan slutte å fungere til å lansere helt, mens andre kan uventet slutter å virke.
Denne spesifikke miner i sin nåværende variant er konsentrert på utvinningen av det Monero kryptovaluta som har en tilpasset versjon av XMRig CPU gruvedrift motoren. Hvis prosjektene viser effektive, kan fremtidige variasjoner av Ntdll.exe lanseres i fremtiden. Som malware bruker programmet susceptabilities å infisere målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Fjerning av Ntdll.exe anbefales sterkt, siden du risikerer ikke bare store elektriske strømkostnader hvis den fungerer på DATAMASKINEN, ennå kan gruvearbeideren i tillegg utføre andre uønskede aktiviteter på den og også skade datamaskinen din permanent.
Ntdll.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” for å fjerne Ntdll.exe
SKRITT 5. Ntdll.exe fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for å fjerne Ntdll.exe
Hvor å forhindre din PC blir infisert med “Ntdll.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Ntdll.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Ntdll.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Ntdll.exe”.







