En helt ny, ekstremt skadelig kryptovaluta-gruve-infeksjon har blitt oppdaget av sikkerhetsforskere. den malware, kalt Node.exe kan forurense målrammede ved hjelp av en rekke midler. Hovedideen bak Node.exe-gruvearbeideren er å bruke cryptocurrency-gruvearbeideraktiviteter på datasystemene til lidende for å skaffe Monero-symboler til ofrenes utgifter. Resultatet av denne gruvearbeideren er de økte strømregningene, og også hvis du lar den stå over lengre tid, kan Node.exe også skade datasystemets komponenter.
Node.exe: distribusjonsmetoder
De Node.exe malware bruksområder 2 foretrukne teknikker som brukes til å infisere datasystemmål:
- Nyttelast Levering ved hjelp av tidligere infeksjoner. Hvis en eldre Node.exe-skadevare er distribuert på målsystemene, kan den umiddelbart oppgradere seg selv eller laste ned en nyere variant. Dette er mulig via den innebygde oppdatert kommando som får frigjørings. Dette gjøres ved å koble til en bestemt forhåndsdefinert hacker styrt web-server som gir den skadelige koden. Den nedlastede og installerte infeksjonen vil sikkert få navnet på en Windows-løsning og også være plassert i “%Systemet% temp” sted. Viktige bygninger og også operativsystemdokumenter blir transformert for å tillate en vedvarende og også stille infeksjon.
- Utnytter programvare for sikkerhetsproblem. Den nyeste versjonen av Node.exe malware har blitt oppdaget å være utløst av enkelte utnyttelser, kjent for å ha blitt brukt i løsepengevareovergrepene. Infeksjoner er gjort ved å målrette åpne tjenester via TCP port. Angrepene er automatiserte av hackere styrt struktur som søker ut om porten er åpen. Hvis dette problemet er oppfylt, vil det sikkert sjekke tjenesten og få informasjon om det, inkludert eventuelle variasjoner samt arrangementsdata. Foretak og populære brukernavn og passordblandinger kan gjøres. Når utnyttelsen aktiveres mot den mottakelige koden, vil gruvearbeideren bli utplassert sammen med bakdøren. Dette vil gi en dobbel infeksjon.
Bortsett fra disse metodene kan andre metoder også brukes. Gruvearbeidere kan distribueres ved phishing-e-poster som sendes ut i grossistsalg på en SPAM-lignende måte, samt er avhengige av sosiale designteknikker for å pusle målene rett til å tro at de har mottatt en melding fra en ekte tjeneste eller virksomhet. Infeksjonsfilene kan enten kobles direkte eller plasseres i kroppsinnholdet i multimedienettinnhold eller meldingslenker.
De slemme gutta kan på samme måte lage destruktive touchdown-websider som kan etterligne leverandørens nedlasting og installering av nettsider, portaler for programvarenedlasting samt forskjellige andre steder som ofte er tilgjengelig. Når de bruker lignende domene som legitime adresser og også sikkerhets- og sikkerhetssertifiseringer, kan kundene bli presset til å koble seg til dem. I noen tilfeller rett og slett å åpne dem kan utløse miner infeksjon.
En annen teknikk ville sikkert være å bruke transportleverandører som kan spres ved hjelp av de ovennevnte tilnærmingene eller ved hjelp av dokumentdelingsnettverk, BitTorrent er blant en av de mest foretrukne. Det brukes jevnlig til å distribuere både ekte programvare og dokumenter samt piratnettinnhold. 2 av en av de mest foretrukne hale tjenesteytere er følgende:
Andre metoder som kan tenkes på av skurkene inkluderer bruk av nettleserkaprere - farlige plugins som er gjort kompatible med en av de mest populære nettleserne. De lastes opp til de relevante depotene med falske brukeranmeldelser og designerlegitimasjon. I mange tilfeller sammendragene kan inkludere skjermbilder, videoklipp samt forseggjorte beskrivelser tiltalende fantastiske funksjonsforbedringer samt effektivitetsoptimaliseringer. Ved oppsett vil imidlertid oppførselen til de berørte nettleserne endres- enkeltpersoner vil finne at de helt sikkert vil bli omdirigert til en hackerkontrollert touchdown-side, i tillegg til at innstillingene deres kan endres – standard nettside, Internett-søkemotor samt splitter nye fanesider.

Node.exe: Analyse
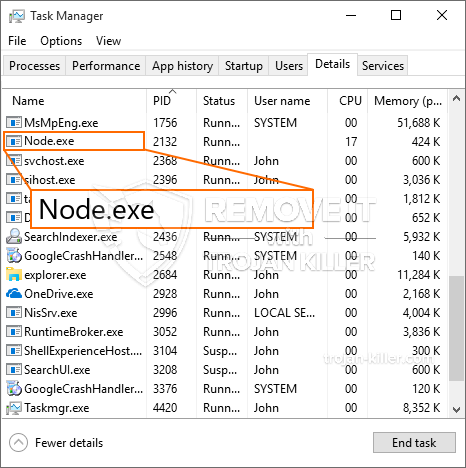
Node.exe malware er en tidløs forekomst av en kryptovaluta-gruvearbeider som avhengig av konfigurasjonen kan forårsake en rekke usikre aktiviteter. Hovedmålet er å utføre intrikate matematiske jobber som helt sikkert vil få mest mulig ut av de tilbudte systemkildene: prosessor, GPU, minne og også harddisk plass. Måten de fungerer på er ved å koble til en spesiell webserver kalt gruvebasseng, hvorfra den kalte koden lastes ned og installeres. Så snart en av oppgavene er lastet ned, vil den bli startet på samme tid, flere forhold kan utføres på en gang. Når en gitt jobb er fullført, vil en annen sikkert lastes ned og installeres på stedet, og løkken vil sikkert fortsette til datasystemet slås av, infeksjonen blir kvitt eller en annen sammenlignbar anledning finner sted. Kryptovaluta vil sikkert deles ut til de kriminelle kontrollerne (hacking team eller en enkelt cyberpunk) rett til sine lommebøker.
En farlig kvalitet ved denne kategorien skadevare er at prøver som ligner på denne kan ta alle systemressurser og også nesten gjøre offerets datasystem ubrukelig til risikoen faktisk er fullstendig kvitt. De fleste av dem har et nådeløst oppsett som gjør dem virkelig utfordrende å bli kvitt. Disse kommandoene vil sikkert gjøre justeringer av oppstartsalternativer, oppsettfiler og også Windows-registerverdier som vil få Node.exe til å starte automatisk når datamaskinen slås på. Tilgjengelighet til gjenvinningsmatvalg og også alternativer kan bli blokkert, noe som gjør mange praktiske fjerningsoversikter nesten meningsløse.
Denne infeksjonen vil sikkert konfigurasjons en Windows-løsning for seg selv, i samsvar med den utførte sikkerhetsevalueringen, er følgende aktiviteter observert:
. Under gruveprosedyrene kan den tilkoblede skadevare kobles til allerede kjørende Windows-løsninger og tredjepartsmonterte applikasjoner. Ved å gjøre det kan det hende at systemansvarlige ikke observerer at kildetonnene kommer fra en egen prosedyre.
| Navn | Node.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Node.exe |

Denne typen malware-infeksjoner er spesielt pålitelige til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på et modulært rammeverk som gjør det mulig for de kriminelle kontrollørene å orkestrere alle slags skadelige vaner. Blant de populære forekomster er endring av Windows-registeret – modifikasjonsstrenger knyttet til operativsystemet kan utløse betydelige ytelsesavbrudd samt manglende evne til å få tilgang til Windows-tjenester. Avhengig av omfanget av endringer kan det også gjøre datamaskinen helt ubrukelig. På den annen side kan manipulering av registerverdier som kommer fra alle slags tredjepartsmonterte applikasjoner sabotere dem. Noen programmer kan mislykkes i å frigis helt, mens andre plutselig kan slutte å fungere.
Denne spesifikke gruvearbeideren i sin nåværende variant er konsentrert om å utvinne Monero-kryptovalutaen, inkludert en tilpasset variant av XMRig CPU-gruvemotoren. Hvis prosjektene bekrefter vellykket, kan fremtidige varianter av Node.exe introduseres i fremtiden. Ettersom skadelig programvare bruker sikkerhetsproblemer i programmet for å forurense målvertene, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Fjerning av Node.exe anbefales sterkt, siden du ikke bare risikerer en stor strømregning hvis den fungerer på DATAMASKINEN, men gruvearbeideren kan i tillegg utføre forskjellige andre uønskede oppgaver på den, samt skade DATAMASKINEN din fullstendig.
Node.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” knappen for å fjerne Node.exe
SKRITT 5. Node.exe fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for å fjerne Node.exe
Hvor å forhindre din PC blir infisert med “Node.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Node.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Node.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Node.exe”.







