En helt ny, veldig farlig kryptovaluta-gruveinfeksjon har blitt oppdaget av sikkerhetsforskere. den malware, kalt Gpapi.exe can infect target victims utilizing a variety of ways. Essensen bak Gpapi.exe-gruvearbeideren er å bruke kryptovalutaoppgavearbeid på datamaskiner til ofre for å skaffe Monero-tokens på offerets bekostning. The outcome of this miner is the elevated power expenses and also if you leave it for longer time periods Gpapi.exe might even harm your computer systems components.
Gpapi.exe: distribusjonsmetoder
De Gpapi.exe malware utilizes two popular approaches which are used to infect computer targets:
- Nyttelast Levering gjennom Tidligere infeksjoner. If an older Gpapi.exe malware is deployed on the target systems it can automatically upgrade itself or download a newer variation. This is possible using the integrated update command which obtains the release. Dette gjøres ved å knytte til en bestemt forhåndsdefinert hacker-kontrollert webserver som gir malware-koden. Det nedlastede viruset får navnet på en Windows-løsning og plasseres i “%Systemet% temp” sted. Vital residential or commercial properties and also running system setup files are transformed in order to allow a relentless and also silent infection.
- Programvare Utnytter Program for sikkerhetsproblem. The most current version of the Gpapi.exe malware have actually been discovered to be triggered by the some ventures, allment forstått for å bli brukt i ransomware-angrep. Infeksjoner er gjort ved å målrette åpne tjenester via TCP port. Angrepene er automatiserte av hackere styrt rammeverk som vender opp om porten er åpen. If this problem is fulfilled it will check the service and retrieve information about it, bestående av enhver type variasjon samt oppsettdata. Exploits and prominent username and password mixes may be done. Når utnyttelsen utløses mot den sårbare koden, vil gruvearbeideren sikkert bli løslatt sammen med bakdøren. Dette vil presentere en dobbelinfeksjon.
In addition to these approaches other methods can be used as well. Miners can be dispersed by phishing emails that are sent in bulk in a SPAM-like fashion and rely on social engineering tricks in order to confuse the sufferers right into thinking that they have actually obtained a message from a legit service or business. The infection data can be either directly connected or put in the body contents in multimedia content or message web links.
The bad guys can also develop harmful landing pages that can pose vendor download web pages, software download websites and various other frequently accessed areas. When they use comparable appearing domain to legitimate addresses and protection certifications the users may be pushed into engaging with them. I noen tilfeller bare åpne dem kan føre til at miner infeksjon.
One more approach would be to utilize payload carriers that can be spread out utilizing those methods or via file sharing networks, BitTorrent er bare ett av de mest foretrukne seg. It is regularly used to disperse both reputable software and also documents and also pirate web content. To av de mest populære hale leverandører er følgende:
Other approaches that can be taken into consideration by the lawbreakers consist of making use of web browser hijackers -hazardous plugins which are made suitable with the most preferred web browsers. They are posted to the appropriate databases with phony user testimonials and programmer credentials. I de fleste tilfeller oppsummeringer kan inkludere skjermbilder, videos and also elaborate descriptions encouraging fantastic feature improvements and performance optimizations. Likevel på avbetaling handlingene påvirket nettlesere vil forvandle- users will discover that they will certainly be redirected to a hacker-controlled touchdown web page as well as their settings might be altered – standard startside, internett søkemotor samt nye faner nettside.

Gpapi.exe: Analyse
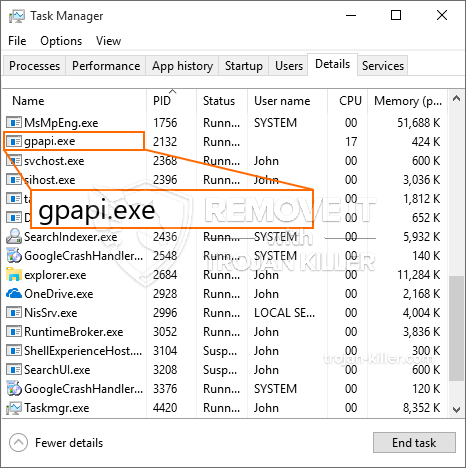
The Gpapi.exe malware is a traditional situation of a cryptocurrency miner which depending on its setup can cause a wide range of harmful activities. Hovedmålet er å utføre kompliserte matematiske oppgaver som vil bruke de lett tilgjengelige systemkildene: prosessor, GPU, minne og også harddisk område. Måten de jobber på er ved å koble til en unik server som kalles gruvedrift, hvor den etterlyste koden lastes ned og installeres. Så snart en av oppgavene er lastet ned, startes den med en gang, flere omstendigheter kan utføres så snart. Når en gitt jobb er ferdig, vil en til lastes ned og installeres på plass, og smutthullet vil fortsette til datamaskinen slås av., infeksjonen elimineres eller en mer sammenlignbar anledning skjer. Kryptovaluta vil deles ut til de kriminelle kontrollerne (hacking gruppe eller en enslig cyberpunk) rett til sine lommebøker.
Et skadelig trekk ved denne kategorien malware er at eksempler som denne kan ta alle systemressurser, samt praktisk talt gjøre offerets datasystem ubrukelig til trusselen er helt fjernet.. Mange av dem har en vedvarende installasjon som gjør dem veldig vanskelige å bli kvitt. Disse kommandoene vil selvfølgelig gjøre endringer for å starte opp valg, setup documents as well as Windows Registry values that will certainly make the Gpapi.exe malware begin instantly once the computer system is powered on. Tilgang til helbredende matvalg samt valg kan være hindret, noe som gjør mange praktiske fjerningsoversikter praktisk talt meningsløse.
Denne spesielle infeksjonen ordner en Windows-tjeneste for seg selv, etter utført beskyttelsesanalyse er følgende handlinger blitt observert:
. Under gruveoperasjonene kan tilkoblet skadelig programvare koble til allerede kjørende Windows-løsninger og tredjeparts installerte applikasjoner. Ved å gjøre det kan systemadministratorene ikke oppdage at ressursbelastningen stammer fra en egen prosedyre.
| Navn | Gpapi.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Gpapi.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre avanserte kommandoer hvis de er konfigurert slik. They are based upon a modular structure enabling the criminal controllers to manage all sort of hazardous behavior. En av de foretrukne tilfeller er innstillingen av Windows-registret – alterations strings related by the os can trigger severe performance disruptions and also the failure to accessibility Windows services. Depending upon the extent of adjustments it can additionally make the computer system completely unusable. On the various other hand control of Registry worths coming from any third-party set up applications can sabotage them. Some applications might stop working to release entirely while others can suddenly stop working.
Denne spesifikke gruvearbeideren i sin nåværende variant er konsentrert om å utvinne Monero-kryptovalutaen med en endret versjon av XMRig CPU-gruvedrift. If the projects verify successful then future versions of the Gpapi.exe can be released in the future. Siden skadelig programvare bruker programvaresårbarheter for å infisere målverter, det kan være en del av en usikker saminfeksjon med ransomware og trojanere.
Elimination of Gpapi.exe is strongly suggested, because you take the chance of not only a big electrical power costs if it is operating on your COMPUTER, but the miner may additionally do other undesirable tasks on it and also even damage your COMPUTER completely.
Gpapi.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Gpapi.exe
SKRITT 5. Gpapi.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Gpapi.exe
Hvor å forhindre din PC blir infisert med “Gpapi.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Gpapi.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Gpapi.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Gpapi.exe”.







