En ny, veldig skadelig kryptovaluta miner infeksjon har faktisk blitt oppdaget av sikkerhetsforskere. den malware, kalt Dxsetup.exe kan forurense target lider det benyttes en rekke fremgangsmåter. Hovedideen bak gruvearbeideren Dxsetup.exe er å benytte gruvearbeideroppgaver i kryptovaluta på datasystemene til ofre for å få Monero-tokens til kostnad for ofre. The result of this miner is the elevated electrical power bills and if you leave it for longer time periods Dxsetup.exe may even harm your computer systems elements.
Dxsetup.exe: distribusjonsmetoder
De Dxsetup.exe malware uses two prominent methods which are utilized to infect computer system targets:
- Nyttelast Levering gjennom Tidligere infeksjoner. If an older Dxsetup.exe malware is deployed on the victim systems it can automatically update itself or download a newer variation. Dette er mulig gjennom den innebygde oppgraderingskommandoen som skaffer lanseringen. Dette gjøres ved å koble til en viss forhåndsdefinert hacker styrt server som gir den skadelige koden. The downloaded and install virus will certainly get the name of a Windows service and also be positioned in the “%Systemet% temp” sted. Important buildings and also running system setup documents are changed in order to allow a consistent and silent infection.
- Programvare Utnytter Program for sikkerhetsproblem. The most recent variation of the Dxsetup.exe malware have been found to be caused by the some ventures, populært forstått for å ha blitt brukt i ransomware-angrepene. Infeksjonene er gjort ved å målrette åpne løsninger ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt rammeverk som vender opp om porten er åpen. If this problem is met it will scan the solution and recover info about it, consisting of any type of version and also setup data. Ventures as well as preferred username and also password mixes might be done. When the make use of is caused against the susceptible code the miner will be deployed in addition to the backdoor. Dette vil sikkert gi en dobbel infeksjon.
In addition to these approaches other strategies can be made use of too. Miners can be distributed by phishing emails that are sent out wholesale in a SPAM-like fashion and rely on social engineering techniques in order to puzzle the targets into believing that they have actually received a message from a reputable service or business. The virus data can be either straight attached or placed in the body contents in multimedia material or text web links.
The wrongdoers can likewise produce harmful touchdown web pages that can impersonate supplier download and install pages, software application download sites as well as other regularly accessed areas. When they utilize similar sounding domain names to reputable addresses as well as safety and security certificates the users might be persuaded into interacting with them. I noen tilfeller bare åpne dem kan føre til at miner infeksjon.
An additional strategy would be to utilize haul providers that can be spread utilizing those approaches or through file sharing networks, BitTorrent er en av de mest populære. It is often utilized to distribute both legit software application and also files and also pirate web content. 2 of one of the most popular haul carriers are the following:
Other methods that can be considered by the crooks consist of the use of internet browser hijackers -harmful plugins which are made suitable with one of the most preferred web browsers. They are published to the relevant repositories with phony customer evaluations as well as developer qualifications. I mange tilfeller kan sammendragene bestå av skjermbilder, videos and sophisticated descriptions appealing wonderful function improvements and performance optimizations. Likevel på avbetaling vaner av de berørte nettlesere vil endre seg- customers will certainly find that they will be rerouted to a hacker-controlled touchdown web page and their settings may be altered – standard nettside, søkemotor samt helt nye faner nettside.

Dxsetup.exe: Analyse
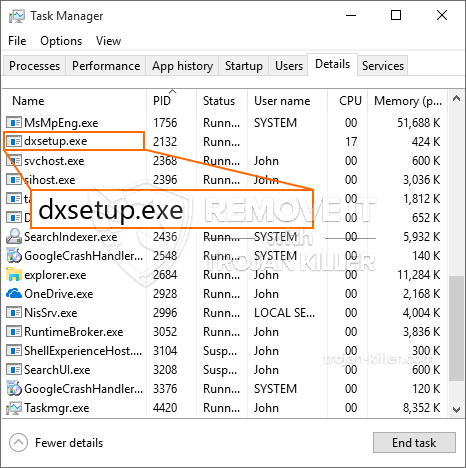
The Dxsetup.exe malware is a timeless instance of a cryptocurrency miner which depending on its configuration can create a wide variety of hazardous actions. Its major objective is to do intricate mathematical tasks that will take advantage of the readily available system sources: prosessor, GPU, minne og harddisk område. The way they operate is by connecting to a special server called mining swimming pool from where the called for code is downloaded and install. As soon as among the tasks is downloaded it will certainly be begun at the same time, flere forhold kan kjøres på en gang. When a provided job is completed another one will be downloaded and install in its location and the loop will continue till the computer system is powered off, TubeDown_Setup.exe malware er et klassisk tilfelle av en kryptovaluta-gruvearbeider som stoler på konfigurasjonen kan utløse en rekke skadelige handlinger. Kryptovaluta vil sikkert bli belønnet til de kriminelle kontrollerne (hacking team eller en enslig cyberpunk) rett til sine budsjetter.
A hazardous characteristic of this category of malware is that samples like this one can take all system sources and also practically make the sufferer computer unusable till the danger has actually been totally gotten rid of. A lot of them feature a consistent installment which makes them truly challenging to eliminate. Disse kommandoene vil foreta justeringer også valg, setup data and Windows Registry values that will make the Dxsetup.exe malware beginning automatically as soon as the computer system is powered on. Access to healing menus as well as alternatives might be obstructed which renders many hand-operated removal guides practically pointless.
Denne spesielle infeksjonen vil absolutt sette opp en Windows-tjeneste for seg selv, following the carried out security evaluation ther adhering to activities have actually been observed:
. During the miner procedures the linked malware can attach to already running Windows services and third-party set up applications. By doing so the system managers might not observe that the resource load originates from a different process.
| Navn | Dxsetup.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Dxsetup.exe |

These type of malware infections are particularly effective at carrying out advanced commands if set up so. They are based on a modular structure enabling the criminal controllers to orchestrate all sort of unsafe behavior. En av de foretrukne eksempler er modifiseringen av Windows-registret – modifications strings related by the os can cause severe performance interruptions and also the lack of ability to gain access to Windows solutions. Depending upon the scope of changes it can also make the computer totally unusable. On the various other hand manipulation of Registry worths belonging to any kind of third-party mounted applications can sabotage them. Some applications might fail to introduce entirely while others can suddenly quit working.
This specific miner in its existing variation is concentrated on mining the Monero cryptocurrency consisting of a customized version of XMRig CPU mining engine. If the campaigns prove successful after that future versions of the Dxsetup.exe can be introduced in the future. Som malware gjør bruk av programvare applikasjons susceptabilities å infisere målet verter, det kan være bestanddel av en usikker samtidig infeksjon med ransomware og også trojanere.
Removal of Dxsetup.exe is highly advised, considering that you run the risk of not just a big electrical power expense if it is running on your COMPUTER, but the miner might additionally do other unwanted activities on it and also even damage your COMPUTER permanently.
Dxsetup.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Dxsetup.exe
SKRITT 5. Dxsetup.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Dxsetup.exe
Hvor å forhindre din PC blir infisert med “Dxsetup.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Dxsetup.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Dxsetup.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Dxsetup.exe”.







