En ny, ekstremt farlig kryptovaluta miner infeksjon har faktisk blitt oppdaget av sikkerhetsforskere. den malware, kalt Cpuminer-amd.exe kan infisere målet lider gjøre bruk av et utvalg av måter. Essensen bak Cpuminer-amd.exe gruvearbeider er å utnytte kryptovaluta miner aktiviteter på datamaskinene til sufferers for å tilegne seg Monero symboler på ofrene utgifter. Utfallet av denne miner er forhøyet elektriske strømregninger så vel som om du lar den stå i lengre perioder av gangen Cpuminer-amd.exe kan også skade din datamaskin elementer.
Cpuminer-amd.exe: distribusjonsmetoder
De Cpuminer-amd.exe malware gjør bruk av 2 fremtredende tilnærminger som er gjort bruk av forurense data mål:
- Nyttelast Levering via Tidligere infeksjoner. Hvis en eldre Cpuminer-amd.exe malware er utplassert på målsystemene kan det umiddelbart oppdatere seg selv eller laste ned en nyere versjon. Dette er mulig gjennom den innebygde oppdatert kommando som får frigjørings. Dette gjøres ved å koble til en bestemt forhåndsdefinert hacker styrt server som gir den skadelige koden. Den nedlastede viruset vil få navnet på en Windows-tjeneste og bli satt i “%Systemet% temp” sted. Essential boliger og operativsystem konfigurasjonsfiler er endret for å tillate en konsekvent og rolig infeksjon.
- Programvare Utnytter Program for sikkerhetsproblem. Den nyeste varianten av Cpuminer-amd.exe malware har blitt oppdaget å bli brakt videre av noen ventures, populært kjent for å bli anvendt i Ransomware angrepene. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Overfallene er automatiserte av hackere styrt rammeverk som søker etter om porten er åpen. Hvis dette problemet er tilfreds det vil skanne løsning samt hente informasjon om det, inkludert alle typer versjon og også konfigurasjonsinformasjon. Ventures samt populære brukernavn- og passordkombinasjoner kan gjøres. Når manipulere utløses mot mottakelige koden miner vil bli utplassert sammen med bakdør. Dette vil sikkert tilby en dual-smitte.
Bortsett fra disse metodene andre metoder kan anvendes også. Gruvearbeidere kan spres ved phishing e-poster som sendes i bulk i en spam-aktig måte, samt stole på sosiale design triks for å puslespill ofrene til å tro at de har fått en melding fra en legit tjeneste eller firma. Infeksjonen dokumenter kan enten direkte festet eller plassert i kroppen innholdet i multimedieinnhold eller meldings lenker.
De kriminelle kan i tillegg lage skadelige Touchdown sider som kan etterligne leverandør laste ned og installere websider, program nedlasting nettsteder og også andre ofte brukte steder. Når de bruker lignende tilsynelatende domene til anerkjente adresser samt sikkerhet sertifiseringer enkeltpersoner kan bli tvunget rett inn i kontakt med dem. I noen tilfeller bare åpne dem kan føre til at miner infeksjon.
En ytterligere tilnærming ville sikkert være å utnytte nyttelast tjenesteytere som kan spres ut ved hjelp av ovennevnte metoder eller ved hjelp av fildelingsnettverk, BitTorrent er blant de mest fremtredende. Det blir jevnlig brukt til å distribuere både legit program samt filer og pirat webinnhold. 2 av de mest prominente hale leverandører er følgende:
Forskjellige andre metoder som kan vurderes av lovbrytere består av å bruke internett nettleserkaprere -dangerous plugins som er laget kompatibel med en av de mest fremtredende nettlesere. De er publisert til de riktige repositories med falske individuelle evalueringer samt utvikler kvalifikasjoner. I de fleste tilfeller beskrivelsene kan inkludere skjermbilder, videoer samt forseggjorte sammendrag tiltalende utmerket funksjon effektivisering og optimaliseringer. Likevel ved installasjon atferd påvirket nettlesere vil sikkert endring- kunder vil finne at de vil sikkert bli omdirigert til en hacker-kontrollert landing nettside samt deres innstillingene kan endres – standard nettside, Internett-søkemotor og splitter nye faner siden.

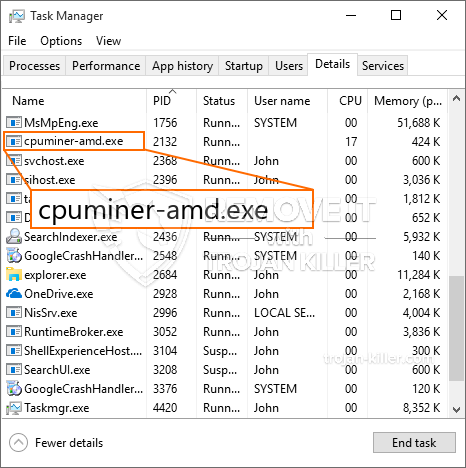
Cpuminer-amd.exe: Analyse
Den Cpuminer-amd.exe skadelig er et klassisk eksempel på et kryptovaluta miner som avhengig av dens oppsettet kan utløse et bredt spekter av farlige aktiviteter. Dens primære mål er å utføre kompliserte matematiske arbeidsplasser som vil sikkert kapitalisere på de tilbudte system kilder: prosessor, GPU, minne og harddisk plass. Metoden de opererer er ved å koble til en unik web server kalt gruvedrift basseng hvor den nødvendige koden er lastet ned. Så raskt som blant oppgavene blir lastet ned det vil sikkert være i gang samtidig, mange tilfeller kan være borte så snart. Når en tilbudt oppgaven er ferdig med ett mer en vil bli lastet ned og installere i sin beliggenhet samt løkken vil sikkert fortsette inntil datamaskinen er slått av, infeksjonen er eliminert eller en mer sammenlign hendelse skjer. Kryptovaluta vil sikkert bli kompensert for den kriminelle kontrollerne (hacking gruppe eller en enkelt cyberpunk) direkte til sine budsjetter.
En skadelig trekk ved denne gruppen av malware er at eksempler som ligner på dette kan man ta alle system kilder og også praktisk talt gjøre offeret datamaskinen ubrukelig til faren faktisk har blitt helt fjernet. De fleste av dem inneholder et vedvarende avdrag som gjør dem veldig vanskelig å fjerne. Disse kommandoene vil sikkert gjøre endringer i oppstartsalternativer, arrangement data samt Windows Registry verdier som vil gjøre Cpuminer-amd.exe malware starter automatisk når datamaskinen er slått på. Tilgjengelighet til rekreasjon menyer og også alternativer kan bli hindret som gir mange manuell fjerning oversikter nesten verdiløs.
Denne spesifikke infeksjonen vil sikkert konfigurasjons en Windows-tjeneste for seg selv, holde utført sikkerhetsanalysen ther i samsvar med aktiviteter har faktisk blitt observert:
. Under gruvearbeider prosedyrer knyttet malware kan koble til for tiden kjører Windows-tjenester og også tredjeparts installerte programmer. Ved å gjøre slik at systemadministratorer kan ikke se at ressurs mange kommer fra en annen prosedyre.
| Navn | Cpuminer-amd.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å detektere og fjerne Cpuminer-amd.exe |

Disse slags malware infeksjoner er spesielt effektiv til å utføre innovative kommandoer hvis satt opp slik at. De er basert på en modulær struktur som tillater den kriminelle kontrollere for å organisere alle typer utrygge vaner. En av de foretrukne tilfeller er modifiseringen av Windows-registret – justeringer trenger tilkoblet av operativsystemet kan føre til store ytelses forstyrrelser og også manglende evne til å åpne Windows-tjenester. Stole på rekke modifikasjoner det kan også gjøre datasystemet helt meningsløst. På de ulike derimot justering av registerverdiene kommer fra enhver form for tredjeparts installerte programmer kan sabotere dem. Noen programmer kan falle kort til å lansere helt, mens andre kan plutselig slutte å fungere.
Denne visse miner i sin nåværende variant er konsentrert på utvinningen av det Monero kryptovaluta som inneholder en endret versjon av XMRig CPU gruvedrift motoren. Hvis kampanjene bevise effektive deretter fremtidige versjoner av Cpuminer-amd.exe kan bli lansert i fremtiden. Som malware bruker programmet sårbarheter å forurense målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware og også trojanere.
Eliminering av Cpuminer-amd.exe på det sterkeste, gitt at du tar sjansen på å ikke bare en stor strømutgiftene hvis det fungerer på din PC, men miner kan i tillegg gjøre andre uønskede oppgaver på den, samt også skade din PC permanent.
Cpuminer-amd.exe fjerningen
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” knappen for å fjerne Cpuminer-amd.exe
SKRITT 5. Cpuminer-amd.exe Fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for remove Cpuminer-amd.exe
Hvor å forhindre din PC blir infisert med “Cpuminer-amd.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Cpuminer-amd.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Cpuminer-amd.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Cpuminer-amd.exe”.







