En helt ny, svært skadelig kryptovaluta miner virus har blitt funnet av trygghet og sikkerhet forskere. den malware, kalt CoreSync.exe kan infisere target pasienter som benytter en rekke måter. Hovedideen bak CoreSync.exe miner er å ansette kryptovaluta miner oppgaver på datasystemene til ofre for å få Monero Merker på mål kostnad. Utfallet av denne miner er hevet elektrisk energi utgifter og også hvis du lar den lenger antall ganger CoreSync.exe kan også skade dine datamaskiner komponenter.
CoreSync.exe: distribusjonsmetoder
De CoreSync.exe skadelig anvendelser to foretrukne metoder som er anvendt for å infisere datamaskinsystemet mål:
- Nyttelast Levering bruke Prior Infeksjoner. Hvis en eldre CoreSync.exe malware er utplassert på den lidende systemer kan det umiddelbart oppgradere seg selv eller laste ned og installere en nyere variant. Dette er mulig ved hjelp av den innebygde oppdateringskommando som overtar utskytnings. Dette gjøres ved å feste til en viss forhåndsdefinert hacker styrt server som gir den skadelige koden. Den nedlastede infeksjon vil sikkert skaffe navnet på en Windows-tjeneste samt bli plassert i “%Systemet% temp” plassering. Essensielle bygninger og operativsystemet arrangement dataene blir transformert for å tillate en vedvarende og rolig infeksjon.
- Programvare Utnytter Søknad om sikkerhetsproblemene. Den nyeste versjonen av CoreSync.exe malware har blitt funnet å være utløst av noen ventures, allmenn kjent for å bli gjort bruk av i ransomware angrepene. Infeksjonene er gjort ved å målrette åpne løsninger via TCP-port. Overfallene er automatiserte av hackere styrt rammeverk som vender opp om porten er åpen. Hvis dette problemet er tilfreds det vil skanne løsningen og også gjenopprette informasjon om det, bestående av en hvilken som helst form for variasjons og arrangement data. Ventures samt fremtredende brukernavn og også passord mikser kan gjøres. Når utnytter er satt av mot i fare kode miner vil sikkert bli lansert i tillegg til bakdør. Dette vil gi den en dobbel infeksjon.
I tillegg til disse teknikker forskjellige andre tekniske midler kan anvendes i tillegg. Gruvearbeidere kan spres ved phishing e-poster som sendes engros i en spam-aktig måte, og også avhengige av sosiale design triks for å forvirre de syke til å tro at de har mottatt en melding fra en legitim løsning eller firma. Viruset filer kan enten direkte festet eller satt inn i kroppen innholdet i multimedieinnhold eller tekstnettlenker.
Synderne kan også lage ondsinnede landing websider som kan etterligne leverandør laste ned nettsider, nedlasting av programvare portaler og andre ofte tilgang til steder. Når de bruker sammenlign tilsynelatende domene til ekte adresser og også sikkerhetssertifiseringer kundene kan bli overtalt rett inn i samspill med dem. I noen tilfeller rett og slett å åpne dem kan føre til at miner infeksjon.
En teknikk ville sikkert være å gjøre bruk av hale bærere som kan være spredt utnytte de ovennevnte teknikker eller ved hjelp av fildelingsnettverk, BitTorrent er en av de mest fremtredende. Det er ofte brukt til å distribuere både legitim programvare og dokumenter, og også pirat webinnhold. 2 av en av de mest foretrukne hale tjenesteytere er følgende:
Diverse andre tilnærminger som kan tas i betraktning ved de kriminelle består av å bruke nettleseren flykaprerne -hazardous plugins som er laget kompatibel med de fleste populære nettlesere. De er sendt til relevante databaser med falske bruker attester samt designer kvalifikasjoner. Ofte beskrivelsene kan inkludere skjermbilder, videoklipp og fancy beskrivelser oppmuntrende fantastisk funksjon effektivisering og optimaliseringer. Men ved avdrag vaner av de berørte nettlesere vil sikkert endre- individer vil finne at de vil bli omdirigert til en hacker styrt destinasjonssiden og også deres oppsett kan bli endret – standard nettside, søkemotor og splitter nye faner siden.
CoreSync.exe: Analyse
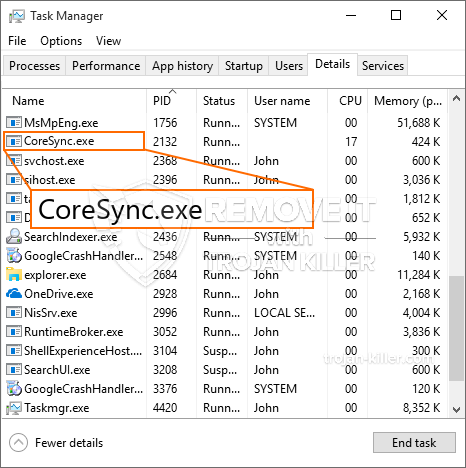
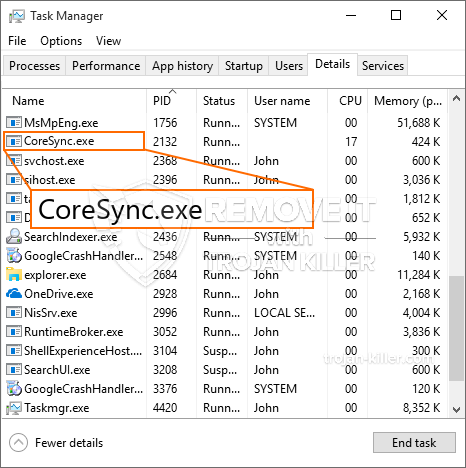
Den CoreSync.exe malware er en klassisk situasjon med en kryptovaluta gruvearbeider som avhengig av oppsettet kan forårsake en rekke skadelige handlinger. Dens hovedmål er å utføre kompliserte matematiske oppgaver som vil sikkert kapitalisere på de lett tilgjengelige systemressurser: prosessor, GPU, minne og harddisk plass. De betyr at de arbeider er ved å koble til en unik server kalt gruvedrift basseng hvor den nødvendige koden er lastet ned. Så raskt som en av oppgavene blir lastet det vil bli startet på en gang, tallrike eksempler kan utføres på en gang. Når en gitt oppgave er ferdig en annen vil sikkert lastes ned og installere på sin plass og også loopen vil fortsette til datamaskinen er slått av, infeksjonen er fjernet, eller en mer lik hendelse finner sted. Kryptovaluta vil deles ut til de kriminelle kontrollerne (hacking gruppe eller en enslig cyberpunk) rett til deres vesker.
En usikker funksjon i denne kategorien av malware er at prøver som dette kan ta alle systemressurser, så vel som praktisk talt gjør offeret datasystem meningsløs inntil faren er helt blitt kvitt. De fleste av dem har en vedvarende installasjon som gjør dem veldig tøft å bli kvitt. Disse kommandoene vil gjøre endringer i oppstartsalternativer, arrangement dokumenter samt Windows Registry verdier som vil sikkert gjøre CoreSync.exe malware starte umiddelbart etter at datamaskinen er slått på. Tilgjengelighet til healing mat valg og også alternativer kan bli blokkert som gir mange manuelle eliminering oversikter nesten ineffektive.
Dette bestemte infeksjon vil konfigurasjons en Windows-løsning for seg selv, holde utført beskyttelse evaluering ther følgende aktiviteter har faktisk blitt observert:
Under gruvearbeider prosedyrer knyttet malware kan koble til for tiden kjører Windows-tjenester og også tredjeparts installerte programmer. Ved å gjøre dette systemet ledere kan ikke merke at kilde masse stammer fra en annen prosess.
| Navn | CoreSync.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å detektere og fjerne CoreSync.exe |

Disse type skadelige infeksjoner er særlig effektive til å utføre sofistikerte kommandoer om å sette opp så. De er basert på en modulær struktur gjør det mulig for kriminelle kontrollere for å administrere alle typer usikre handlinger. Blant de foretrukne eksempler er endring av Windows-registeret – justeringer strenger forbundet med os kan utløse betydelige ytelses avbrudd og også manglende evne til å få tilgang til Windows-løsninger. Stole på rekke justeringer kan det også gjøre datasystemet helt ubrukelig. På den annen side justering av register worths kommer fra tredjeparts installerte programmer kan sabotere dem. Noen programmer kan unnlate å lansere helt, mens andre kan plutselig slutte arbeids.
Denne spesifikke miner i sin nåværende versjon er fokusert på gruvedrift Monero kryptovaluta består av en endret variant av XMRig CPU gruvedrift motor. Hvis kampanjene bekrefte effektive deretter fremtidige versjoner av CoreSync.exe kan innføres i fremtiden. Som malware gjør bruk av programvare susceptabilities å forurense målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Fjerning av CoreSync.exe er svært oppmerksom, fordi du risikerer ikke bare en stor strøm regning hvis det kjører på datamaskinen, men miner kan i tillegg gjøre andre uønskede oppgaver på det, så vel som med skade datamaskinen helt.
CoreSync.exe fjerningen
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” knappen for å fjerne CoreSync.exe
SKRITT 5. CoreSync.exe Fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for remove CoreSync.exe
Hvor å forhindre din PC blir infisert med “CoreSync.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “CoreSync.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “CoreSync.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “CoreSync.exe”.







