En helt ny, veldig skadelig kryptovaluta-gruvevirus har faktisk blitt identifisert av sikkerhets- og sikkerhetsforskere. den malware, kalt Cli.exe can contaminate target victims utilizing a range of ways. The main point behind the Cli.exe miner is to employ cryptocurrency miner tasks on the computer systems of targets in order to obtain Monero tokens at victims expense. The end result of this miner is the raised electrical power expenses and if you leave it for longer time periods Cli.exe might also harm your computers components.
Cli.exe: distribusjonsmetoder
De Cli.exe malware uses two popular approaches which are used to contaminate computer system targets:
- Nyttelast Levering gjennom Tidligere infeksjoner. If an older Cli.exe malware is deployed on the sufferer systems it can immediately update itself or download and install a more recent variation. This is feasible through the integrated upgrade command which acquires the launch. Dette gjøres ved å koble til en spesifikk forhåndsdefinert hackerkontrollert server som leverer skadevarekoden. Den lastet ned og installere infeksjon vil sikkert få navnet på en Windows-løsning og bli satt i “%Systemet% temp” sted. Crucial residential or commercial properties and also operating system setup files are transformed in order to allow a persistent as well as silent infection.
- Programvare Utnytter Program for sikkerhetsproblem. The latest version of the Cli.exe malware have been located to be caused by the some ventures, kjent for å bli brukt i de ransomware angrep. Infeksjoner er gjort ved å målrette åpne løsninger gjennom TCP-port. Angrepene er automatiserte av hackere styrt ramme som søker ut om porten er åpen. If this problem is satisfied it will check the solution and also fetch details about it, bestående av en hvilken som helst variasjon samt oppsett data. Ventures as well as popular username and also password combinations may be done. When the make use of is caused against the at risk code the miner will be released along with the backdoor. Dette vil gi den en dobbel infeksjon.
Apart from these techniques other approaches can be utilized also. Miners can be dispersed by phishing e-mails that are sent in bulk in a SPAM-like way and rely on social engineering tricks in order to puzzle the sufferers into believing that they have actually gotten a message from a reputable solution or business. The infection files can be either directly attached or placed in the body components in multimedia content or message links.
The lawbreakers can also develop destructive landing pages that can impersonate vendor download and install pages, software download sites and also various other often accessed areas. When they make use of similar seeming domain to legitimate addresses and safety certificates the individuals might be pushed into connecting with them. I noen tilfeller bare åpne dem kan sette av miner infeksjon.
One more strategy would be to utilize payload providers that can be spread out making use of the above-mentioned methods or by means of documents sharing networks, BitTorrent er blant de mest foretrukne. It is often utilized to distribute both legitimate software application and documents and also pirate web content. 2 av de mest foretrukne nyttelastleverandører er de følgende:
Other methods that can be thought about by the offenders consist of using internet browser hijackers -harmful plugins which are made compatible with the most preferred web internet browsers. They are published to the appropriate databases with fake user testimonials and programmer credentials. I mange tilfeller sammendragene kan inkludere skjermbilder, videos and also elaborate descriptions appealing fantastic function enhancements and performance optimizations. Nevertheless upon installation the actions of the impacted web browsers will transform- individuals will discover that they will be redirected to a hacker-controlled landing web page as well as their settings might be changed – standard startside, Internett-søkemotor, og også nye faner nettside.

Cli.exe: Analyse
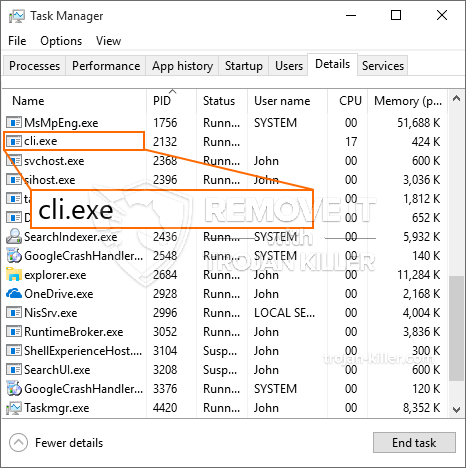
The Cli.exe malware is a classic case of a cryptocurrency miner which depending on its configuration can trigger a wide variety of hazardous activities. Hovedmålet er å gjøre kompliserte matematiske jobber som helt sikkert vil dra nytte av de tilgjengelige systemkildene: prosessor, GPU, minne og harddiskplass. Metoden de fungerer er ved å koble til en spesiell server kalt mining swimming pool hvor den nødvendige koden lastes ned. Så raskt som blant oppgavene blir lastet ned vil det bli startet på en gang, flere forhold kan være borte for når. Når en gitt oppgave er fullført, vil en annen helt sikkert bli lastet ned og installeret i stedet, og smutthullet vil sikkert fortsette til datamaskinen slås av, infeksjonen er blitt kvitt eller annen tilsvarende hendelse finner sted. Kryptovaluta vil sikkert deles ut til de kriminelle kontrollerne (hacking gruppe eller en enslig hacker) direkte til sine lommebøker.
En usikker egenskap ved denne klassifiseringen av skadelig programvare er at eksempler som dette kan ta alle systemkilder og nesten gjøre måldatasystemet meningsløst inntil faren er fullstendig eliminert. De fleste av dem har en konsekvent installasjon som gjør dem veldig vanskelige å fjerne. Disse kommandoene vil gjøre endringer for å starte opp alternativer, arrangement documents and also Windows Registry values that will certainly make the Cli.exe malware begin automatically when the computer system is powered on. Tilgang til utvalg og alternativer for rekreasjonsmat kan bli hindret, noe som gjør mange praktiske elimineringsoversikter praktisk talt ubrukelige.
Denne bestemt infeksjon vil sette opp en Windows-tjeneste for seg selv, i samsvar med den utførte beskyttelsesevalueringen, er følgende aktiviteter faktisk observert:
. Under gruveoperasjonene kan den tilkoblede skadevare koble til Windows-løsninger som kjører for øyeblikket og også installerte tredjepartsapplikasjoner. Ved å gjøre det kan det hende at systemansvarlige ikke oppdager at ressursbelastningen kommer fra en annen prosess.
| Navn | Cli.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Cli.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på et modulært rammeverk som gjør det mulig for kriminelle kontrollører å orkestrere alle typer farlige vaner. Blant de populære tilfellene er endringen av Windows-registeret – modifikasjonsstrenger knyttet til operativsystemet kan utløse alvorlige effektivitetsavbrudd og manglende evne til å få tilgang til Windows-løsninger. Avhengig av omfanget av justeringer kan det også gjøre datamaskinen helt meningsløs. På den annen side kan manipulering av registerverdier som kommer fra alle slags tredjepartsoppsettprogrammer sabotere dem. Noen applikasjoner kan komme til å slippe helt ut, mens andre plutselig kan slutte å fungere.
Denne bestemte gruvearbeideren i sin nåværende variant er fokusert på å trekke ut Monero-kryptovalutaen inkludert en modifisert versjon av XMRig CPU-gruvemotoren. If the projects prove effective then future versions of the Cli.exe can be introduced in the future. Siden skadelig programvare bruker programvaresårbarheter for å infisere målverter, det kan være en del av en skadelig samtidig infeksjon med ransomware og også trojanere.
Elimination of Cli.exe is highly recommended, siden du risikerer ikke bare store strømkostnader hvis den kjører på DATAMASKINEN, men gruvearbeideren kan også gjøre andre uønskede oppgaver på den og også skade PC-en din fullstendig.
Cli.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Cli.exe
SKRITT 5. Cli.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Cli.exe
Hvor å forhindre din PC blir infisert med “Cli.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Cli.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Cli.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Cli.exe”.







