En helt ny, really unsafe cryptocurrency miner infection has been detected by protection scientists. den malware, kalt Bvhost.exe kan forurense target lider ved hjelp av en rekke fremgangsmåter. The essence behind the Bvhost.exe miner is to use cryptocurrency miner activities on the computer systems of targets in order to obtain Monero symbols at sufferers expenditure. The result of this miner is the raised electrical power expenses and also if you leave it for longer amount of times Bvhost.exe might even harm your computers parts.
Bvhost.exe: distribusjonsmetoder
De Bvhost.exe malware benytter 2 preferred techniques which are made use of to infect computer targets:
- Nyttelast Levering bruke Prior Infeksjoner. If an older Bvhost.exe malware is released on the target systems it can instantly upgrade itself or download and install a newer variation. Dette er mulig ved hjelp av den integrerte oppdateringskommandoen som kjøper utgivelsen. Dette gjøres ved å feste til en spesiell forhånds hacker styrt web-server som gir den skadelige koden. The downloaded virus will acquire the name of a Windows service and be positioned in the “%Systemet% temp” område. Essential properties and running system arrangement documents are transformed in order to allow a relentless and silent infection.
- Utnytter programvare for sikkerhetsproblem. The latest variation of the Bvhost.exe malware have been located to be caused by the some ventures, kjent anerkjent for å være brukt i Ransomware streik. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt ramme som søker ut om porten er åpen. If this condition is satisfied it will scan the solution and also recover details regarding it, including any type of version and also arrangement information. Utnytter og også ønsket brukernavn og passord mikser kan gjøres. When the manipulate is set off versus the at risk code the miner will be released together with the backdoor. Dette vil gi den en dobbel infeksjon.
Apart from these approaches various other techniques can be utilized also. Miners can be dispersed by phishing emails that are sent wholesale in a SPAM-like fashion as well as rely on social design tricks in order to perplex the sufferers right into thinking that they have obtained a message from a legit solution or business. The infection documents can be either directly attached or inserted in the body components in multimedia material or text web links.
The crooks can likewise create destructive landing pages that can impersonate vendor download web pages, software program download sites and also other often accessed areas. When they use comparable seeming domain names to genuine addresses and also protection certificates the users may be pushed right into engaging with them. Noen ganger kan bare å åpne dem forårsake gruveinfeksjonen.
Another method would certainly be to utilize haul carriers that can be spread making use of those methods or by means of data sharing networks, BitTorrent er blant de mest fremtredende. It is regularly utilized to disperse both reputable software program and also documents and pirate web content. 2 av de mest fremtredende nyttelast bærere er følgende:
Various other methods that can be taken into consideration by the lawbreakers consist of the use of web browser hijackers -hazardous plugins which are made compatible with the most popular internet browsers. They are uploaded to the appropriate repositories with phony user reviews and designer credentials. I mange tilfeller kan sammendragene inneholde skjermbilder, videos and elaborate summaries encouraging excellent function improvements and performance optimizations. Nonetheless upon installment the actions of the influenced browsers will certainly transform- customers will find that they will certainly be redirected to a hacker-controlled landing page and their setups might be altered – standard nettside, online søkemotoren samt splitter nye faner nettside.

Bvhost.exe: Analyse
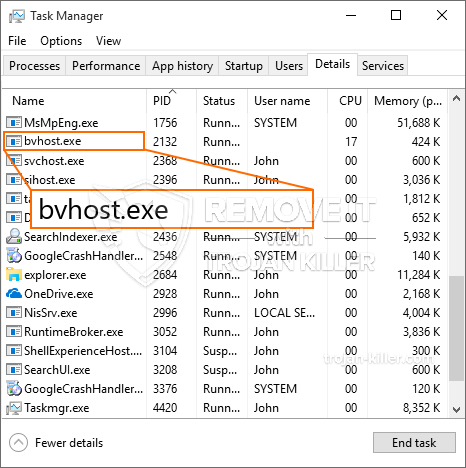
The Bvhost.exe malware is a classic case of a cryptocurrency miner which depending upon its configuration can trigger a variety of harmful actions. Det primære målet er å utføre intrikate matematiske jobber som vil dra nytte av de tilgjengelige systemkildene: prosessor, GPU, minne samt harddiskområdet. Måten de opererer på er ved å knytte seg til en spesiell server som heter mining pool hvor den nødvendige koden lastes ned. Så snart blant oppgavene blir lastet det vil bli startet på samme tid, flere forhold kan kjøres på en gang. Når en oppgave er fullført, vil en annen lastes ned på sin plassering, og løkken vil fortsette til datamaskinen er slått av, infeksjonen elimineres eller en annen sammenlignbar anledning finner sted. Kryptovaluta vil deles ut til de kriminelle kontrollerne (hacking team eller en enslig hacker) direkte til sine lommebøker.
Et farlig attributt for denne klassifiseringen av skadelig programvare er at prøver som ligner på denne kan ta alle systemressursene og praktisk talt gjøre datamaskinen til offer ubrukelig til faren er fullstendig eliminert. Mange av dem inkluderer en jevn installasjon som gjør dem faktisk vanskelig å bli kvitt. Disse kommandoene vil gjøre endringer for å starte opp alternativer, arrangement data and also Windows Registry values that will make the Bvhost.exe malware start automatically as soon as the computer system is powered on. Tilgang til valg av helbredende mat og alternativer kan blokkeres, noe som gjør at manuelle guider for manuell eliminering er praktisk talt ubrukelige.
Denne spesifikke infeksjonen vil sikkert sette opp en Windows-tjeneste for seg selv, i samsvar med den utførte sikkerhetsanalysen er følgende handlinger faktisk blitt observert:
. Under gruveprosedyrene kan den tilknyttede skadelige programvaren koble seg til Windows-tjenester som for øyeblikket kjører, og også installerte applikasjoner fra tredjepart. Ved å gjøre det kan det hende at systemadministratorene ikke observerer at ressurspartiene stammer fra en egen prosess.
| Navn | Bvhost.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Bvhost.exe |

Denne typen malware-infeksjoner er spesielt pålitelige til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på et modulært rammeverk som gjør det mulig for de kriminelle kontrollørene å orkestrere alle slags skadelige vaner. Blant de populære forekomster er endring av Windows-registeret – modifikasjonsstrenger knyttet til operativsystemet kan utløse betydelige ytelsesavbrudd samt manglende evne til å få tilgang til Windows-tjenester. Avhengig av omfanget av endringer kan det også gjøre datamaskinen helt ubrukelig. På den annen side kan manipulering av registerverdier som kommer fra alle slags tredjepartsmonterte applikasjoner sabotere dem. Noen programmer kan mislykkes i å frigis helt, mens andre plutselig kan slutte å fungere.
Denne spesifikke gruvearbeideren i sin nåværende variant er konsentrert om å utvinne Monero-kryptovalutaen, inkludert en tilpasset variant av XMRig CPU-gruvemotoren. If the projects verify successful then future variations of the Bvhost.exe can be introduced in the future. Ettersom skadelig programvare bruker sikkerhetsproblemer i programmet for å forurense målvertene, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Removal of Bvhost.exe is strongly recommended, siden du ikke bare risikerer en stor strømregning hvis den fungerer på DATAMASKINEN, men gruvearbeideren kan i tillegg utføre forskjellige andre uønskede oppgaver på den, samt skade DATAMASKINEN din fullstendig.
Bvhost.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Bvhost.exe
SKRITT 5. Bvhost.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Bvhost.exe
Hvor å forhindre din PC blir infisert med “Bvhost.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Bvhost.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Bvhost.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Bvhost.exe”.







