En ny, virkelig usikre kryptovaluta miner infeksjonen har faktisk blitt funnet av sikkerhetsforskere. den malware, kalt BRTSvc.exe kan forurense mållidende ved å bruke en rekke metoder. Essensen bak BRTSvc.exe-gruvearbeideren er å bruke kryptovaluta-gruvearbeideroppgaver på datamaskinsystemene til mål for å få Monero-symboler til syke kostnad. The end result of this miner is the raised electrical power expenses and also if you leave it for longer time periods BRTSvc.exe might even damage your computer systems components.
BRTSvc.exe: distribusjonsmetoder
De BRTSvc.exe malware gjør bruk av 2 foretrukne fremgangsmåter som anvendes til å forurense data mål:
- Nyttelast Levering via Tidligere infeksjoner. If an older BRTSvc.exe malware is deployed on the sufferer systems it can automatically update itself or download a more recent variation. Dette er mulig gjennom den innebygde oppgradering kommando som får utgivelsen. Dette gjøres ved å koble til en bestemt forhåndsdefinert hacker styrt web-server som gir den skadelige koden. Den lastet ned og installere infeksjon vil sikkert skaffe navnet på en Windows-løsning og også være plassert i “%Systemet% temp” område. Vitale boliger samt operativsystem arrangement dataene blir transformert for å gi en vedvarende samt stille infeksjon.
- Programvare Utnytter Søknad om sikkerhetsproblemene. The latest version of the BRTSvc.exe malware have actually been found to be caused by the some ventures, allmenn kjent for å bli anvendt i Ransomware angrepene. Infeksjoner er gjort ved å målrette åpne løsninger gjennom TCP-port. Angrepene er automatiserte av hackere styrt rammeverk som søker etter om porten er åpen. Hvis dette problemet er oppfylt det vil skanne løsningen og også få informasjon om det, inkludert hvilken som helst type av variasjon, så vel som konfigurasjonsinformasjon. Ventures og populær brukernavn og også passord kombinasjoner kan gjøres. Når gjøre bruk av er forårsaket versus den sårbare koden miner vil bli lansert sammen med bakdør. Dette vil sikkert tilby en dual-smitte.
Foruten disse metodene diverse andre tilnærminger kan gjøres bruk av for. Gruvearbeidere kan bli distribuert av phishing e-poster som er sendt ut engros i en spam-aktig måte, så vel som avhenger av sosiale design teknikker for å forvirre målene rett inn å tenke at de har mottatt en melding fra en ekte tjeneste eller selskap. De virus filer kan enten rett festet eller innført i kroppen komponentene i multimedie materiale eller meldingsforbindelser.
Skurkene kan også produsere skadelige touchdown websider som kan etterligne leverandør laste ned nettsider, programvare applikasjonsnedlastingsportaler samt diverse andre ofte brukte steder. Når de bruker likelydende domene til ekte adresser samt sikkerhetssertifikater kundene kan bli presset til å engasjere med dem. I noen tilfeller bare åpne dem kan utløse miner infeksjon.
En metode vil være å bruke hale leverandører som kan spres ut ved hjelp av de ovennevnte teknikker eller via dokumenter som deler nettverk, BitTorrent er bare ett av de mest foretrukne seg. Det er ofte brukt til å distribuere både anerkjente program samt dokumenter samt piratmateriale. 2 av en av de mest foretrukne nyttelast tjenesteleverandører er følgende:
Diverse andre teknikker som kan tas i betraktning ved de kriminelle består av å gjøre bruk av nettleserkaprere -hazardous plugins som er laget kompatibel med de mest foretrukne web nettlesere. De er lagt ut til de riktige databaser med falske bruker attester og også designer legitimasjon. I mange tilfeller beskrivelsene kan inkludere skjermbilder, videoer samt forseggjorte sammendrag lovende fantastiske funksjonsforbedringer og ytelsesoptimaliseringer. Likevel ved installasjon handlingene til de berørte nettlesere vil sikkert forandre- brukere vil finne at de vil bli omdirigert til en hacker-kontrollert landing nettside og deres oppsett kan endres – standard nettside, søkemotor samt helt nye faner nettside.

BRTSvc.exe: Analyse
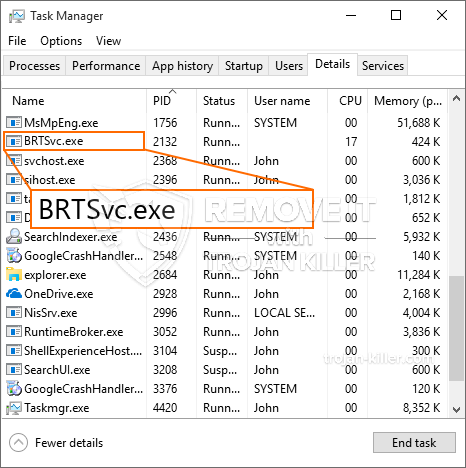
The BRTSvc.exe malware is a timeless situation of a cryptocurrency miner which depending on its arrangement can cause a wide range of hazardous activities. Its main goal is to carry out intricate mathematical tasks that will certainly make use of the offered system sources: prosessor, GPU, minne og harddiskområde. The method they work is by linking to a special web server called mining pool from where the called for code is downloaded and install. Så snart en av jobbene er lastet ned, vil den absolutt bli startet samtidig, mange tilfeller kan kjøres på når. When a provided job is finished another one will be downloaded in its area as well as the loop will continue till the computer is powered off, infeksjonen elimineres eller det oppstår en annen sammenlignbar hendelse. Kryptovaluta vil bli kompensert for den kriminelle kontrollerne (hacking gruppe eller en enkelt cyberpunk) direkte til sine lommebøker.
A harmful attribute of this group of malware is that examples like this one can take all system sources and also almost make the sufferer computer pointless till the threat has actually been completely removed. A lot of them include a consistent installation that makes them truly challenging to remove. Disse kommandoene vil selvfølgelig gjøre endringer også opsjoner, setup data and Windows Registry values that will certainly make the BRTSvc.exe malware start automatically when the computer is powered on. Accessibility to healing menus and choices might be blocked which makes numerous manual elimination guides almost worthless.
Denne infeksjonen vil sikkert arrangement en Windows-løsning for seg selv, adhering to the performed safety analysis ther adhering to actions have been observed:
. During the miner operations the linked malware can attach to currently running Windows services and third-party set up applications. By doing so the system administrators may not observe that the source lots originates from a different procedure.
| Navn | BRTSvc.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove BRTSvc.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på et modulært rammeverk som gjør det mulig for kriminelle kontrollører å koordinere alle typer farlige vaner. En av de foretrukne eksempler er modifiseringen av Windows-registret – justeringer strenger relatert av operativsystemet kan utløse alvorlige forstyrrelser i effektiviteten og manglende evne til å få tilgang til Windows-tjenester. Avhengig av omfanget av justeringer kan det i tillegg gjøre datamaskinen helt meningsløs. På den annen side kan justering av registerverdier som tilhører tredjeparts konfigurerte applikasjoner undergrave dem. Noen applikasjoner kan ikke komme til å starte helt, mens andre uventet kan slutte å fungere.
Denne spesifikke gruvearbeideren i sin nåværende variant er konsentrert om gruvedrift av Monero cryptocurrency som består av en modifisert versjon av XMRig CPU gruvemotor. If the projects confirm successful then future variations of the BRTSvc.exe can be launched in the future. Ettersom skadelig programvare bruker sikkerhetsproblemer i programmet for å forurense målvertene, det kan være en del av en farlig saminfeksjon med ransomware og trojanere.
Removal of BRTSvc.exe is highly suggested, siden du ikke bare risikerer en stor strømkostnad hvis den fungerer på DATAMASKINEN, men gruvearbeideren kan i tillegg utføre forskjellige andre uønskede oppgaver på den og også skade datamaskinen din permanent.
BRTSvc.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove BRTSvc.exe
SKRITT 5. BRTSvc.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove BRTSvc.exe
Hvor å forhindre din PC blir infisert med “BRTSvc.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “BRTSvc.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “BRTSvc.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “BRTSvc.exe”.







