Selskapet sier at en ukjent gruppe nettkriminelle i reelle angrep er allerede aktivt å utnytte dette sikkerhets problem.
The vulnerability received an identifier CVE-2019-27296, Og, i henhold til CVSS målestokk, det mottatt 9.8 påpeker av 10.“På grunn av alvorlighetsgraden av dette sikkerhetsproblemet, Oracle anbefaler sterkt kunder til å installere oppdateringer så snart som mulig”, - advarer i Oracle.
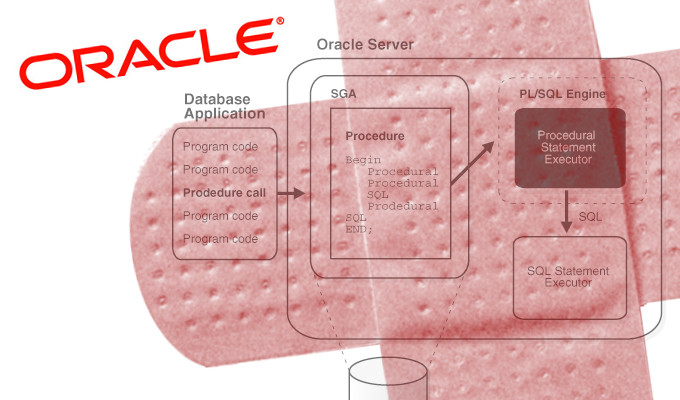
The breach is described as a deserialization problem in Oracle WebLogic Server Web Services via XMLDecoder, allowing a remote unauthorized attacker to execute arbitrary code on the victim’s server. This results in complete control over the attacked server.
Les også: Angripere aktivt utnytte tidligere oppdaget sårbarhet i Oracle WebLogic
“The vulnerability of remote code execution can be exploited without having to go through the authentication process. Og dermed, an attacker can use a security problem without having username or password,” – said in the Oracle notification.
Company also noted connection of this vulnerability with a previously unmentioned problem of deserialization under the identifier CVE-2019-2725. She was also present at Oracle WebLogic Server, Men was patched in April of this year.
Kilde: https://www.oracle.com
