
RIG exploit pak begon het verspreiden van een voorheen onbekende versie van Vega ransomware.
Buran encoder versleutelt gebruikersbestanden en nodigt het slachtoffer uit om via e-mail contact op te nemen met cybercriminelen voor gegevensherstel. De security analisten zijn nog niet in staat om een decoder te creëren voor de nieuwe malware geweest en adviseren slachtoffers kopiëren losgeld documenten, evenals registry entries die door de malware.Het onderzoeksteam heeft een nieuwe payload van de RIG-malwarekit ontdekt geen_sec, die gespecialiseerd is in het volgen van exploit packs. Dat hebben internetbeveiligingsspecialisten ontdekt, RIG maakt misbruik van kwetsbaarheden in de Internet Explorer-browser om cryptograaf naar doelapparaten te sturen. Eenmaal op de automaat, Buran kopieert zichzelf naar de map met %APPDATA%microsoftwindowsctfmon.exe, en gaat vervolgens verder met het coderen van de informatie van het slachtoffer.
Volgens analisten, de nieuwe malware verwijdert geen schaduwkopieën van de volumes, schakelt het automatische herstelmechanisme van Windows niet uit, en maakt de gebeurtenislogboeken niet schoon.
Ransomware codeert alle bestanden op de schijf, met uitzondering van de objecten die op de stoplijst staan. Versleuteling heeft geen invloed op bestanden met de extensie COM, exe, dll, SYS, evenals enkele andere formaten. In aanvulling op, ransomware mist ongeveer veertig mappen, waarvan de inhoud de werking van het apparaat kan verstoren.
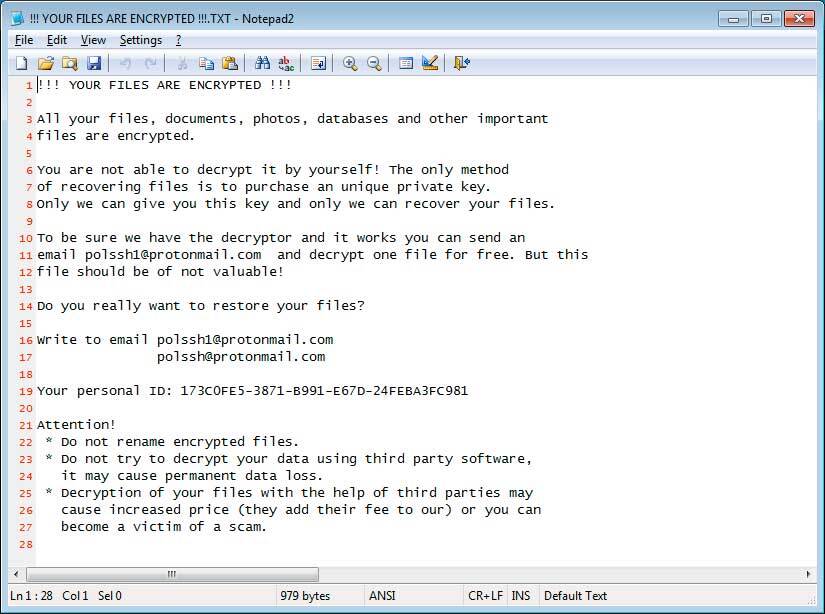
Voor de geïnfecteerde computer, er wordt een unieke computer-ID aangemaakt, die Buran ook gebruikt als extensie van de gewijzigde bestanden. Bericht aan het slachtoffer is vervat in een tekstdocument met de naam !!! UW bestanden worden versleuteld !!!. tekst. Aanvallers bieden het slachtoffer aan om per e-mail contact met hen op te nemen om de SLEUTEL te krijgen, en waarschuwen tegen pogingen om de gegevens zelf te herstellen.
Onderzoekers merken op dat malware in het register wordt aangemaakt HKEY_CURRENT_USERSoftwareBuran vermeldingen die vergelijkbaar zijn met de openbare en persoonlijke coderingssleutel, maar het is niet bekend of het mogelijk is om gecodeerde informatie te herstellen door ze te gebruiken.
RIG is momenteel een van de meest actieve exploitpacks. Hij verving de Visser, Nucleair En Neutrino zet in 2016. RIG-operators gaan vaak contracten aan om ransomware te verspreiden en worden op verschillende tijdstippen afgeleverd Matrix, Vergrendeld, CryptoShield En GANDCRAB ernaar toe met behulp van coderingssoftware.
Ondanks de algemene daling van het aandeel kant-en-klare kits, RIG verschijnt regelmatig in het gezichtsveld van informatiebeveiligingsspecialisten. Zo, vorige zomer, hij werd gespot in de CEIDPageLock rootkit-campagne.
- Back-up, Back-up, Back-up!
- Open geen bijlagen als u niet weet wie ze heeft verzonden.
- Open geen bijlagen totdat u bevestigt dat de persoon u deze daadwerkelijk heeft gestuurd.
- Scan bijlagen met tools zoals VirusTotal.
- Zorg ervoor dat alle Windows-updates worden geïnstalleerd zodra ze uitkomen! Zorg er ook voor dat u alle programma's bijwerkt, vooral java, Flash, en Adobe Reader. Oudere programma's bevatten beveiligingsproblemen die vaak worden uitgebuit door malwaredistributeurs. Daarom is het belangrijk om ze up-to-date te houden.
- Zorg ervoor dat u een soort beveiligingssoftware hebt geïnstalleerd.
- Gebruik harde wachtwoorden en hergebruik nooit hetzelfde wachtwoord op meerdere sites.
- Als u Remote Desktop Services gebruikt, verbind het niet rechtstreeks met internet. Maak het in plaats daarvan alleen toegankelijk via een VPN.
