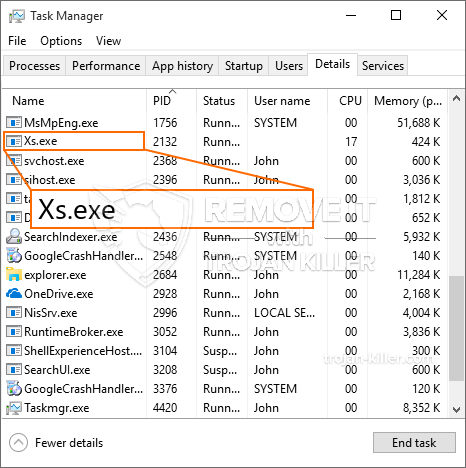
Een gloednieuw, door veiligheidsonderzoekers is een zeer schadelijk cryptocurrency miner-virus gevonden. de malware, riep Xs.exe kan doelpatiënten besmetten door gebruik te maken van een reeks methoden. De essentie achter de Xs.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten in te zetten op de computers van patiënten om Monero-symbolen te verwerven op kosten van de slachtoffers. Het eindresultaat van deze mijnwerker zijn de verhoogde elektriciteitskosten en als u het voor langere tijd verlaat, kan Xs.exe zelfs uw computersysteemelementen beschadigen.
Xs.exe: distributiemethoden
De Xs.exe malware toepassingen 2 prominente technieken die worden gebruikt om computersysteemdoelen te infecteren:
- Payload Levering door middel van Prior Infecties. Als een oudere Xs.exe-malware op de systemen van het slachtoffer wordt vrijgegeven, kan deze zichzelf onmiddellijk bijwerken of een recentere versie downloaden en installeren. Dit is mogelijk via de ingebouwde update-commando dat de lancering verwerft. Dit gebeurt door het verbinden van een bepaalde vooraf gedefinieerde hacker gecontroleerde webserver die malware code voorziet. De gedownloade infectie krijgt zeker de naam van een Windows-service en wordt ook in de “%systeem% temp” plaats. Belangrijke huizen en configuratiegegevens van het besturingssysteem worden gewijzigd om een meedogenloze en ook stille infectie mogelijk te maken.
- Software Vulnerability Exploits. Er is ontdekt dat de nieuwste variant van de Xs.exe-malware wordt veroorzaakt door enkele exploits, volksmond bekend om te worden gebruikt in de ransomware aanvallen. De infecties worden gedaan door zich te richten geopend diensten met behulp van de TCP-poort. De aanslagen worden geautomatiseerd door een hacker gecontroleerd kader die zoekt naar als de poort open. Als aan deze voorwaarde is voldaan, zal het de service controleren en details erover herstellen, inclusief elk type versie en configuratiegegevens. Exploits evenals populaire gebruikersnaam en wachtwoord mixen kan worden gedaan. Wanneer de exploit wordt veroorzaakt versus de risicocode, zal de mijnwerker zeker naast de achterdeur worden ingezet. Dit zal zeker zorgen voor de dubbele infectie.
Naast deze technieken kunnen ook andere benaderingen worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die op een SPAM-achtige manier in het groot worden verzonden en vertrouwen op social engineering-technieken om de slachtoffers in de war te brengen door te geloven dat ze een bericht hebben ontvangen van een echte dienst of bedrijf. De virusdocumenten kunnen rechtstreeks worden aangebracht of in de hoofdcomponenten worden geplaatst in multimedia-inhoud of tekstweblinks.
De boeven kunnen ook destructieve landingspagina's produceren die webpagina's van leveranciers kunnen downloaden en installeren, software download portals en ook andere vaak benaderd locaties. Wanneer ze een domein gebruiken dat lijkt op echte adressen en beveiligingscertificaten, kunnen de gebruikers worden overgehaald om met hen te communiceren. In sommige gevallen is ze gewoon het openen kan de mijnwerker infectie activeren.
Een andere strategie zou zeker zijn om payload-dragers te gebruiken die kunnen worden verspreid met behulp van die technieken of via netwerken voor het delen van gegevens, BitTorrent behoort tot een van de meest populaire. Het wordt vaak gebruikt om zowel legitieme software als bestanden en illegale inhoud te verspreiden. Twee van de meest geprefereerde aanbieders van transport zijn de volgende:
Verschillende andere benaderingen die door de overtreders kunnen worden overwogen, zijn onder meer het gebruik van browserkapers - gevaarlijke plug-ins die geschikt zijn gemaakt voor de meest prominente webbrowsers. Ze worden in de relevante repositories geplaatst met valse getuigenissen van klanten en ook kwalificaties van programmeurs. In veel gevallen is de samenvattingen kunnen zijn screenshots, video's en uitgebreide samenvattingen die prachtige attribuutverbeteringen en ook efficiëntie-optimalisaties aanmoedigen. Desalniettemin zullen na installatie de gewoonten van de getroffen browsers veranderen- individuen zullen merken dat ze zeker zullen worden omgeleid naar een door een hacker gecontroleerde touchdown-webpagina en dat hun instellingen kunnen worden gewijzigd – de standaard startpagina, zoekmachine op internet, alsmede nieuwe tabbladen webpagina.

Xs.exe: Analyse
De Xs.exe-malware is een tijdloos geval van een cryptocurrency-mijnwerker die, afhankelijk van de opstelling, een breed scala aan schadelijke activiteiten kan veroorzaken. Het belangrijkste doel is om gecompliceerde wiskundige taken uit te voeren die zeker gebruik zullen maken van de beschikbare systeembronnen: processor, GPU, geheugen evenals harde schijf ruimte. De manier waarop ze werken is door verbinding te maken met een unieke server genaamd mining pool van waaruit de vereiste code wordt gedownload en geïnstalleerd. Zodra een van de banen is gedownload, wordt tegelijkertijd gestart, meerdere instanties kunnen voor een keer verdwijnen. Wanneer een aangeboden taak is voltooid, zal er zeker nog een in zijn plaats worden gedownload en de lus zal zeker doorgaan totdat de computer wordt uitgeschakeld, de infectie is geëlimineerd of er doet zich een andere vergelijkbare gelegenheid voor. Cryptogeld zal worden gecompenseerd voor de criminele controllers (hacken groep of een enkele cyberpunk) direct naar hun portemonnee.
Een gevaarlijke eigenschap van deze classificatie van malware is dat voorbeelden zoals deze alle systeembronnen kunnen gebruiken en het computersysteem van het slachtoffer virtueel onbruikbaar kunnen maken totdat de dreiging volledig is geëlimineerd. De meeste van hen bevatten een meedogenloze aflevering waardoor ze eigenlijk moeilijk te elimineren zijn. Deze commando's zullen wijzigingen in keuzes maken, configuratiedocumenten en Windows-registerwaarden die ervoor zorgen dat de Xs.exe-malware automatisch start wanneer het computersysteem wordt ingeschakeld. Toegankelijkheid tot herstelmenu's en -opties kan worden geblokkeerd, waardoor veel handmatige verwijderingsgidsen vrijwel ondoeltreffend zijn.
Dit bepaalde infectie zal een Windows-service configuratie voor zichzelf, zich houden aan de uitgevoerde beschermingsevaluatie zijn de volgende acties in acht genomen:
. Tijdens de mijnwerkeroperaties kan de bijbehorende malware zich hechten aan reeds draaiende Windows-services en geïnstalleerde applicaties van derden. Door dit te doen, zien de systeembeheerders mogelijk niet dat de resource tonnen uit een afzonderlijk proces komen.
| Naam | Xs.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware om Xs.exe te detecteren en te verwijderen |

Dit soort malware-infecties zijn vooral betrouwbaar bij het uitvoeren van geavanceerde opdrachten als ze zo zijn geconfigureerd. Ze zijn gebaseerd op een modulaire structuur die de criminele controleurs in staat stelt om allerlei soorten gevaarlijke acties te orkestreren. Onder de prominente voorbeelden is het aanpassen van het Windows-register – aanpassingsstrings die door het besturingssysteem zijn verbonden, kunnen grote prestatieverstoringen en het gebrek aan toegang tot Windows-services veroorzaken. Vertrouwend op het bereik van aanpassingen kan het het computersysteem ook volkomen zinloos maken. Aan de andere kant aanpassing van de Register-waarden afkomstig van elke vorm van derden opgezet toepassingen kan ze saboteren. Sommige applicaties werken mogelijk niet meer en worden helemaal niet meer vrijgegeven, terwijl andere ineens kunnen stoppen met werken.
Deze bepaalde miner in zijn bestaande variant is geconcentreerd op het minen van de Monero-cryptocurrency, bestaande uit een gewijzigde versie van de XMRig CPU-mining-engine. Als de campagnes effectief blijken te zijn, kunnen toekomstige versies van Xs.exe in de toekomst worden geïntroduceerd. Als de malware gebruik maakt van de zwakke plekken in software om de beoogde gastheer te infecteren, het kan deel uitmaken van een schadelijke co-infectie met ransomware en ook Trojaanse paarden.
Eliminatie van Xs.exe wordt ten zeerste aanbevolen, aangezien u de kans loopt niet alleen grote elektriciteitskosten te betalen als het op uw COMPUTER werkt, maar de mijnwerker kan er ook verschillende andere ongewenste activiteiten op uitvoeren en zelfs uw pc permanent beschadigen.
Xs.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Xs.exe te verwijderen
STAP 5. Xs.exe verwijderd!
video Guide: Hoe GridinSoft Anti-Malware te gebruiken voor het verwijderen van Xs.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Xs.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Xs.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Xs.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Xs.exe”.







