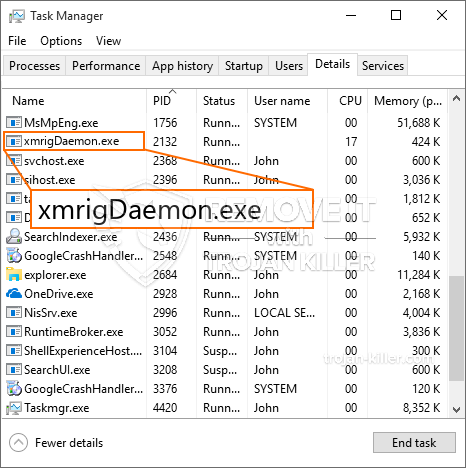
Een gloednieuw, echt onveilig cryptogeld mijnwerker infectie is geïdentificeerd door de veiligheid onderzoekers. de malware, riep XmrigDaemon.exe can infect target sufferers making use of a range of ways. Het belangrijkste punt achter de XmrigDaemon.exe miner is cryptogeld Miner taken in de computersystemen van patiënten gebruiken voor het verkrijgen Monero tokens bij patiënten uitgaven. The outcome of this miner is the raised electricity bills and if you leave it for longer periods of time XmrigDaemon.exe might also damage your computers components.
XmrigDaemon.exe: distributiemethoden
De XmrigDaemon.exe malware utilizes two popular techniques which are utilized to infect computer targets:
- Payload Delivery gebruik Prior Infecties. If an older XmrigDaemon.exe malware is deployed on the sufferer systems it can automatically update itself or download and install a newer version. This is possible through the integrated upgrade command which acquires the launch. Dit wordt gedaan door te linken naar een bepaalde vooraf gedefinieerde hacker-gecontroleerde server die de malwarecode geeft. The downloaded virus will get the name of a Windows service as well as be placed in the “%systeem% temp” Gebied. Vital buildings and operating system arrangement files are altered in order to allow a relentless and silent infection.
- Software programma Kwetsbaarheid Exploits. The most current variation of the XmrigDaemon.exe malware have been discovered to be brought on by the some ventures, algemeen bekend om te worden gebruikt bij de ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend diensten met behulp van de TCP-poort. De slagen worden geautomatiseerd door een hacker gecontroleerd kader dat bedoeld indien de poort open. If this problem is met it will scan the solution and retrieve details about it, uit elke variatie en instellingsgegevens. Exploits en populaire gebruikersnaam en wachtwoordmixen kunnen worden gedaan. When the make use of is set off against the at risk code the miner will be released in addition to the backdoor. Dit zal zeker presenteren een duale infectie.
Besides these methods other methods can be used as well. Miners can be dispersed by phishing emails that are sent in bulk in a SPAM-like way as well as depend on social design methods in order to puzzle the victims right into thinking that they have actually obtained a message from a genuine service or company. The virus data can be either straight attached or placed in the body materials in multimedia web content or message links.
The offenders can likewise produce destructive landing web pages that can impersonate supplier download and install web pages, software download sites evenals andere veelgebruikte locaties. When they use similar sounding domain to genuine addresses as well as safety certifications the individuals might be coerced into engaging with them. In sommige gevallen is ze gewoon het openen kan de mijnwerker infectie activeren.
An additional strategy would certainly be to use haul service providers that can be spread out utilizing those approaches or through file sharing networks, BitTorrent is slechts een van de meest prominente. It is frequently utilized to disperse both legit software program and data and also pirate web content. Twee van de meest populaire haul providers zijn de volgende:
Various other approaches that can be thought about by the bad guys consist of the use of internet browser hijackers -unsafe plugins which are made compatible with one of the most prominent web internet browsers. They are submitted to the appropriate repositories with phony customer reviews and also developer credentials. In de meeste gevallen zijn de samenvattingen kunnen zijn screenshots, videos as well as intricate descriptions appealing excellent feature enhancements and also efficiency optimizations. Na installatie zullen de acties van de getroffen internetbrowsers echter veranderen- individuals will certainly locate that they will certainly be redirected to a hacker-controlled touchdown web page and also their setups might be changed – de standaard startpagina, zoekmachine en nieuwe tabbladen webpagina.

XmrigDaemon.exe: Analyse
The XmrigDaemon.exe malware is a classic situation of a cryptocurrency miner which depending on its arrangement can cause a variety of unsafe activities. Its major goal is to perform complicated mathematical tasks that will certainly capitalize on the readily available system resources: processor, GPU, geheugen en ook de harde schijf ruimte. The method they work is by connecting to an unique server called mining pool from where the called for code is downloaded and install. Zo snel als een van de taken is gedownload zal worden begonnen in een keer, meerdere instanties kunnen voor een keer verdwijnen. When a given job is completed one more one will be downloaded in its location and also the loop will proceed till the computer system is powered off, de infectie wordt verwijderd of een andere vergelijkbare gebeurtenis vindt plaats. Cryptogeld zal zeker beloond worden naar de correctionele controllers (hacken groep of een eenzame cyberpunk) direct naar hun portemonnee.
A harmful quality of this classification of malware is that examples like this one can take all system sources and practically make the victim computer system unusable until the threat has been totally eliminated. A lot of them feature a consistent installation which makes them really difficult to remove. Deze commando's zullen zeker veranderingen om keuzes te starten maken, configuration data as well as Windows Registry values that will make the XmrigDaemon.exe malware beginning automatically once the computer system is powered on. Accessibility to healing food selections and options may be blocked which renders lots of hand-operated elimination guides almost ineffective.
Deze specifieke infectie zal zeker een Windows-oplossing voor zichzelf regelen, adhering to the carried out security analysis ther following actions have been observed:
. Tijdens de mijnwerker procedures kunnen de bijbehorende malware aansluiten op reeds met Windows oplossingen en ook derden geïnstalleerde toepassingen. By doing so the system administrators might not see that the source load comes from a different procedure.
| Naam | XmrigDaemon.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove XmrigDaemon.exe |

Dit soort malware-infecties zijn bijzonder efficiënt in het uitvoeren van innovatieve opdrachten als ze zo zijn ingesteld. They are based on a modular structure enabling the criminal controllers to manage all type of hazardous habits. Onder de populaire gevallen is de wijziging van het Windows-register – alterations strings associated by the operating system can create severe efficiency disturbances and the inability to accessibility Windows services. Depending upon the range of changes it can additionally make the computer system totally unusable. Aan de andere kant manipulatie van de Register-waarden afkomstig van elke vorm van derden opgezet toepassingen kan ze saboteren. Sommige toepassingen kunnen te kort schieten om volledig te lanceren, terwijl anderen plotseling kunnen stoppen met werken.
This specific miner in its current version is focused on extracting the Monero cryptocurrency including a changed variation of XMRig CPU mining engine. If the campaigns verify successful after that future versions of the XmrigDaemon.exe can be launched in the future. Als de malware maakt gebruik van software susceptabilities tot doel gastheren besmetten, het kan onderdeel van een gevaarlijke co-infectie met ransomware en ook Trojaanse paarden zijn.
Elimination of XmrigDaemon.exe is highly recommended, considering that you risk not only a large electrical energy costs if it is running on your PC, yet the miner may also carry out various other unwanted activities on it and also damage your COMPUTER permanently.
XmrigDaemon.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove XmrigDaemon.exe
STAP 5. XmrigDaemon.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove XmrigDaemon.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “XmrigDaemon.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “XmrigDaemon.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “XmrigDaemon.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “XmrigDaemon.exe”.







