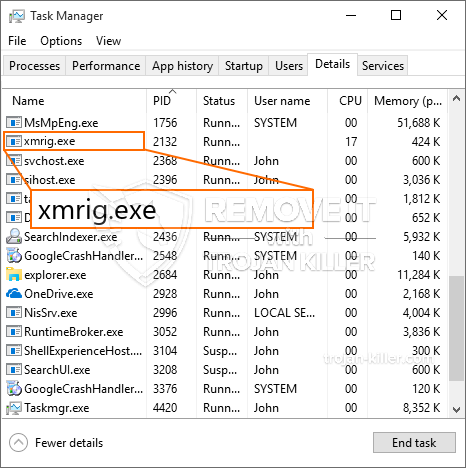
Een gloednieuw, zeer schadelijk cryptogeld mijnwerker besmetting is vastgesteld door onderzoekers bescherming. de malware, riep xmrig kunnen besmetten doel patiënten met behulp van een selectie van methoden. De essentie achter de XMRig mijnwerker is in dienst te nemen cryptogeld mijnwerker taken op de computers van de patiënten met het oog op Monero symbolen op doelen kosten te verwerven. Het resultaat van deze mijnwerker is de verhoogde energiekosten en als je het laten voor langere tijd XMRig kan zelfs schade toebrengen aan uw computer systemen onderdelen.
xmrig: distributiemethoden
De xmrig malware toepassingen 2 voorkeurstechnieken waarbij gebruik wordt gemaakt aan te besmetten computersysteem doelen:
- Payload Delivery gebruik Prior Infecties. Als een oudere XMRig malware wordt ingezet op de lijder systemen kunnen zij zelf of download direct bij te werken en installeer een recentere versie. Dit is mogelijk door middel van de ingebouwde upgrade commando dat de lancering verkrijgt. Dit wordt gedaan door te koppelen aan een specifieke vooraf gedefinieerde hacker gecontroleerde server die de malware code geeft. De gedownloade infectie zal de naam van een Windows-service te krijgen en ook worden gepositioneerd in de “%systeem% temp” plaats. Essentiële eigenschappen alsmede besturingssysteem inrichting data getransformeerd om een consistente maken en latente besmetting.
- Software Vulnerability Exploits. De nieuwste versie van de XMRig malware daadwerkelijk zijn ontdekt te worden veroorzaakt door het aantal exploits, beroemde begrepen te worden gebruik gemaakt van de ransomware aanslagen. De infecties worden gedaan door zich te richten geopend oplossingen met behulp van de TCP-poort. De aanslagen worden geautomatiseerd door een hacker gecontroleerd kader dat bedoeld indien de poort open. Als dit probleem wordt voldaan zal het zeker controleren de service en krijgen informatie over, bestaande uit een versie en rangschikking data. Exploits en preferente gebruikersnaam en wachtwoord combinaties kan worden gedaan. Als het gebruik maken van wordt verrekend met de kwetsbare code mijnwerkers zeker mee wordt vrijgegeven met de achterdeur. Dit zal zeker presenteren een duale infectie.
Afgezien van deze benaderingen andere benaderingen kunnen ook worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing e-mails die in bulk in een SPAM-achtige manier worden verzonden en ook afhankelijk van social engineering trucs om de slachtoffers verwarren recht te denken dat ze daadwerkelijk hebben gekregen een bericht van een echte dienst of onderneming. Het virus documenten kunnen ofwel direct worden aangesloten of geplaatst in het lichaam stoffen in multimediaal materiaal of bericht weblinks.
De overtreders kunnen ook de ontwikkeling van kwaadaardige landing webpagina's die vendor download kan imiteren en installeren van webpagina's, softwaretoepassing download sites en ook andere regelmatig benaderd gebieden. Wanneer zij gebruik maken van vergelijkbare klinkende domeinnamen aan legit adressen en certificaten bescherming van de gebruikers kan worden geduwd in contact met ze hebben. In sommige gevallen alleen het openen van hen kan de mijnwerker infectie activeren.
Een aanvullende strategie zou zeker gebruik te maken van haul service providers die kunnen worden verspreid met behulp van deze methoden of door documenten te delen netwerken, BitTorrent is een van de meest prominente. Het wordt vaak gebruik gemaakt van zowel gerenommeerde software en documenten en ook piraten inhoud verspreiden. Twee van de meest prominente payload providers zijn de volgende:
Andere technieken die door de daders kan worden beschouwd onder meer gebruik te maken van internet browser hijackers -Schadelijk plugins die verenigbaar zijn met de meest geprefereerde internet browsers worden gemaakt. Ze worden geüpload naar de juiste databases met valse beoordelingen van klanten evenals designer kwalificaties. In veel gevallen kan de beschrijvingen screenshots omvatten, video's en ingewikkelde samenvattingen aantrekkelijk prachtige functie verbeteringen en ook de prestaties optimalisaties. Niettemin na het instellen van de gewoonten van de getroffen internet browsers zal veranderen- gebruikers zullen vinden dat ze zullen worden doorgestuurd naar een-hacker gecontroleerde touchdown pagina en de instellingen kunnen worden gewijzigd – de standaard startpagina, internet zoekmachine en ook gloednieuwe tabs webpagina.

xmrig: Analyse
De XMRig malware is een tijdloos voorbeeld van een cryptogeld mijnwerker die, afhankelijk van de opstelling kan een breed scala aan onveilige activiteiten veroorzaken. Zijn primaire doel is om ingewikkelde wiskundige taken die zeker het meest van de aangeboden systeembronnen zal presteren: processor, GPU, geheugen en harde schijf area. De methode die ze functie wordt door het aanbrengen van een unieke server genaamd mijnbouw zwembad waar de vereiste code is gedownload en geïnstalleerd. Zo snel als een van de banen wordt gedownload zal het zeker worden gelijktijdig gestart, tal van omstandigheden kan worden gegaan voor zodra. Wanneer een voorwaarde taak voltooid één meer men zal zeker op zijn plaats gedownload evenals de maas in de wet zal zeker doorgaan totdat de computer is uitgeschakeld, de infectie wordt verwijderd of extra vergelijkbare gebeurtenis voordoet. Cryptogeld zal zeker worden gecompenseerd naar de correctionele controllers (hacken groep of een eenzame cyberpunk) rechtstreeks naar hun portemonnee.
Een gevaarlijke eigenschap van deze categorie van malware is dat monsters zoals deze een overzicht van alle systeem bronnen te nemen, evenals vrijwel de lijder computer onbruikbaar maken, totdat de dreiging daadwerkelijk is volledig ontdoen van gekregen. De meerderheid van hen zijn onder andere een meedogenloze setup die hen eigenlijk moeilijk te verwijderen maakt. Deze commando's zullen zeker aanpassingen aan keuzes te starten maken, setup-bestanden en ook Windows-register waarden die zeker zal maken van de XMRig malware automatisch beginnen zodra het computersysteem is ingeschakeld. De toegankelijkheid van het helen van voedsel selecties evenals keuzes zou kunnen worden belemmerd, waardoor een groot aantal hands-on overzichten verwijdering praktisch waardeloos.
Deze specifieke infectie zal zeker het opzetten van een Windows-oplossing voor zichzelf, vast te houden aan het gevoerde veiligheid en beveiliging analyse ther voldoen aan acties daadwerkelijk waargenomen:
. Tijdens de mijnwerker procedures de bijbehorende malware verbinding kan maken met al met Windows diensten, alsmede van derden gemonteerd toepassingen. Door dit te doen zodat het systeem beheerders mogen niet in de gaten dat de bron veel komt uit een apart proces.
| Naam | xmrig |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware op te sporen en te verwijderen XMRig |

Dit soort malware-infecties zijn bijzonder efficiënt bij het vervullen van geavanceerde commando's als zo opgezet. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controllers om allerlei gevaarlijke acties te beheren. Onder de populaire gevallen is de aanpassing van het Windows-register – wijzigingen strings geassocieerd door het besturingssysteem kan leiden tot ernstige prestaties onderbrekingen en ook het gebrek aan toegankelijkheid Windows oplossingen te creëren. Afhankelijk van de omvang van de wijzigingen die zij kan bovendien maken de computer volledig zinloos. Aan de andere kant aanpassing registerwaarden behoren tot een type derde partij bevestigd toepassingen wordt ondermijnd. Sommige toepassingen kunnen stoppen met werken volledig in te voeren, terwijl anderen onverwacht kan stoppen met werken.
Deze bijzondere mijnwerker in de bestaande versie is gericht op het extraheren van de Monero cryptogeld waaronder een aangepaste variant van XMRig CPU mijnbouw motor. Als de projecten effectief controleren na dat toekomstige varianten van het XMRig kan worden gelanceerd in de toekomst. Als de malware maakt gebruik van software kwetsbaarheden te misbruiken doelhosts infecteren, het kan een deel van een gevaarlijke co-infectie met ransomware zijn evenals Trojans.
Eliminatie van XMRig wordt sterk aanbevolen, gezien het feit dat je de kans om niet alleen een groot elektriciteitsrekening te nemen als deze wordt uitgevoerd op uw computer, maar de mijnwerker kan bovendien andere ongewenste taken uit te voeren op en ook uw computer volledig beschadigen.
XMRig verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om XMRig verwijderen
STAP 5. XMRig verwijderd!
video Guide: Hoe wordt GridinSoft Anti-Malware gebruiken voor het verwijderen XMRig
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “xmrig” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “xmrig”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “xmrig”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “xmrig”.







