Een nieuw, echt gevaarlijk cryptocurrency mijnwerkervirus is geïdentificeerd door veiligheidswetenschappers. de malware, riep Wmpps.exe kan infecteren doel slachtoffers met behulp van diverse manieren. Het belangrijkste punt achter de Wmpps.exe-mijnwerker is het gebruik van cryptocurrency-mijnwerkeractiviteiten op de computersystemen van patiënten om Monero-tokens te verkrijgen tegen de kosten van de patiënt.. The end result of this miner is the raised power expenses and also if you leave it for longer periods of time Wmpps.exe may also harm your computers elements.
Wmpps.exe: distributiemethoden
De Wmpps.exe malware uses two popular methods which are made use of to contaminate computer targets:
- Payload Delivery gebruik Prior Infecties. If an older Wmpps.exe malware is released on the victim systems it can immediately upgrade itself or download a newer version. This is feasible using the integrated upgrade command which obtains the launch. Dit gebeurt door het koppelen van een specifieke vooraf bepaalde hacker-gecontroleerde server die de malware code voorziet. De gedownloade infectie zal zeker de naam van een Windows-service te verwerven en in het worden gebracht “%systeem% temp” plaats. Essential residential or commercial properties and also running system configuration documents are altered in order to allow a consistent and quiet infection.
- Software Application Vulnerability Exploits. The newest variation of the Wmpps.exe malware have actually been located to be triggered by the some ventures, commonly recognized for being used in the ransomware assaults. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De aanslagen worden geautomatiseerd door een hacker gecontroleerd kader die zoekt naar als de poort open. If this problem is satisfied it will certainly check the solution and retrieve info concerning it, inclusief elke versie en ook configuratiegegevens. Exploits en geprefereerde gebruikersnaam ook wachtwoordcombinaties kan worden gedaan. When the manipulate is caused versus the at risk code the miner will be released along with the backdoor. Dit zal zeker presenteren een duale infectie.
Aside from these approaches other strategies can be utilized also. Miners can be distributed by phishing e-mails that are sent in bulk in a SPAM-like fashion and also depend on social engineering methods in order to puzzle the targets right into thinking that they have obtained a message from a genuine solution or firm. The virus data can be either straight attached or inserted in the body contents in multimedia web content or text web links.
The bad guys can likewise create destructive touchdown pages that can impersonate vendor download and install pages, software application download portals and other frequently accessed areas. When they utilize similar appearing domain to genuine addresses and also security certifications the individuals may be persuaded right into communicating with them. In sommige gevallen is ze gewoon het openen kan de mijnwerker infectie activeren.
One more strategy would be to utilize haul service providers that can be spread out making use of those methods or using documents sharing networks, BitTorrent is een van de meest geprefereerde. It is regularly used to disperse both legit software application as well as documents and pirate content. Twee van de meest geprefereerde transporteurs zijn de volgende:
Other methods that can be thought about by the offenders include using browser hijackers -hazardous plugins which are made compatible with the most prominent internet browsers. They are uploaded to the appropriate repositories with fake user reviews and developer qualifications. In de meeste gevallen zijn de samenvattingen zou kunnen bestaan uit screenshots, videos and also intricate descriptions appealing wonderful feature enhancements and also performance optimizations. Nevertheless upon installment the behavior of the influenced browsers will certainly transform- users will certainly find that they will certainly be rerouted to a hacker-controlled landing web page and their settings may be changed – de standaard startpagina, zoekmachine evenals gloednieuwe tabs pagina.

Wmpps.exe: Analyse
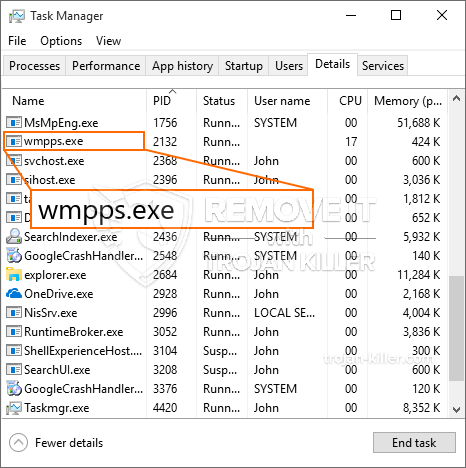
The Wmpps.exe malware is a classic situation of a cryptocurrency miner which depending on its configuration can create a wide array of dangerous actions. Its main objective is to perform complex mathematical jobs that will certainly make use of the readily available system resources: processor, GPU, geheugen en harde schijf ruimte. The way they function is by linking to a special web server called mining pool from where the called for code is downloaded and install. Zodra een van de taken is gedownload, wordt deze meteen gestart, tal van omstandigheden kan worden uitgevoerd bij zodra. When a given task is finished another one will certainly be downloaded and install in its place and also the loop will proceed until the computer is powered off, de infectie is verdwenen of er vindt nog een vergelijkbare gelegenheid plaats. Cryptogeld zal zeker worden toegekend aan de criminele controllers (hacken team of een enkele cyberpunk) rechtstreeks naar hun portemonnee.
A dangerous characteristic of this group of malware is that samples such as this one can take all system sources and practically make the target computer system pointless up until the danger has actually been totally gotten rid of. A lot of them include a relentless installment which makes them truly challenging to remove. Deze opdrachten zullen aanpassingen te keuzes te maken, arrangement documents as well as Windows Registry values that will certainly make the Wmpps.exe malware start immediately once the computer system is powered on. Access to recovery food selections and alternatives might be obstructed which makes lots of manual removal guides almost useless.
Dit bepaalde infectie zal een Windows-service configuratie voor zichzelf, naar aanleiding van de uitgevoerde veiligheidsanalyse zijn andere volgende activiteiten daadwerkelijk geobserveerd:
. During the miner procedures the linked malware can hook up to already running Windows services and third-party installed applications. Hierdoor zien de systeembeheerders mogelijk niet dat de bronbelasting afkomstig is van een andere procedure.
| Naam | Wmpps.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Wmpps.exe |

Dit soort malware-infecties zijn vooral betrouwbaar bij het vervullen van geavanceerde commando's als zo opgezet. They are based on a modular framework allowing the criminal controllers to orchestrate all sort of hazardous behavior. Among the popular examples is the alteration of the Windows Registry – adjustments strings connected by the os can cause severe efficiency interruptions and the failure to gain access to Windows services. Depending on the extent of adjustments it can also make the computer entirely pointless. Aan de andere kant kan controle over registerwaarden afkomstig van elk type geïnstalleerde applicaties van derden deze ondermijnen. Some applications may fail to launch entirely while others can suddenly quit working.
This certain miner in its present variation is concentrated on mining the Monero cryptocurrency consisting of a customized version of XMRig CPU mining engine. If the projects confirm successful then future variations of the Wmpps.exe can be introduced in the future. Als de malware maakt gebruik van software programma kwetsbaarheden te besmetten doelhosts, het kan deel uitmaken van een gevaarlijke co-infectie met ransomware en ook Trojaanse paarden.
Elimination of Wmpps.exe is strongly advised, because you run the risk of not only a huge power costs if it is running on your COMPUTER, but the miner may likewise carry out various other undesirable activities on it as well as also harm your COMPUTER permanently.
Wmpps.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Wmpps.exe
STAP 5. Wmpps.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Wmpps.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Wmpps.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Wmpps.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Wmpps.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Wmpps.exe”.







