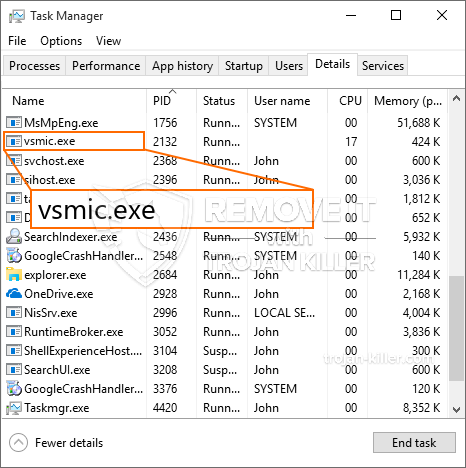
Een nieuw, zeer onveilig cryptocurrency miner virus is opgemerkt door beveiligingsonderzoekers. de malware, riep Vsmic.exe infecteren doel patiënten met behulp van verschillende methodes. De essentie achter de Vsmic.exe-mijnwerker is om cryptocurrency-mijnertaken toe te passen op de computersystemen van patiënten om Monero-symbolen te krijgen tegen streefkosten. The end result of this miner is the elevated electrical energy bills and if you leave it for longer amount of times Vsmic.exe might even damage your computer systems components.
Vsmic.exe: distributiemethoden
De Vsmic.exe malware maakt gebruik 2 populaire methoden die worden gebruikt voor het besmetten computersysteem doelen:
- Payload bezorging via Prior Infecties. If an older Vsmic.exe malware is released on the victim systems it can automatically upgrade itself or download a newer version. Dit is mogelijk door middel van de geïntegreerde upgrade commando dat de lancering verkrijgt. Dit gebeurt door het koppelen van een bepaalde vooraf gedefinieerde hacker gecontroleerde webserver die malware code geeft. De gedownloade en installeer infectie zal de naam van een Windows-oplossing te verwerven en in het worden gebracht “%systeem% temp” plaats. Essentiële eigenschappen en installeren van het besturingssysteem bestanden worden gewijzigd om een consistente en ook rustig infectie toestaan.
- Software programma Kwetsbaarheid Exploits. The newest version of the Vsmic.exe malware have been found to be brought on by the some exploits, beroemde begrepen te worden gebruik gemaakt van de ransomware strikes. De infecties worden gedaan door zich te richten geopend diensten via de TCP-poort. De aanslagen worden geautomatiseerd door een hacker gecontroleerd kader die zoekt naar als de poort open. Als aan deze voorwaarde wordt voldaan zal het zeker scan de service en informatie te verkrijgen met betrekking tot deze, bestaande uit elk type versie en installatie-informatie. Exploiteert en ook prominent gebruikersnaam en ook met een wachtwoord combinaties kunnen worden gedaan. Wanneer de exploit wordt veroorzaakt ten opzichte van de risico code mijnwerkers zeker ingezet met de achterdeur. Dit zal het een dubbele infectie.
Afgezien van deze methoden andere methoden kunnen ook worden gebruikt. Mijnwerkers kunnen worden gedistribueerd door phishing e-mails die in bulk in een worden verzonden SPAM-achtige manier evenals afhangen van social design trucs om de doelstellingen te verwarren recht te denken dat ze eigenlijk een boodschap hebben verkregen van een betrouwbare oplossing of onderneming. De infectie gegevens kunnen direct worden aangebracht of geplaatst in het lichaam componenten in multimedia-inhoud of boodschap weblinks.
De wetsovertreders kan ook de ontwikkeling van schadelijke landing webpagina's die vendor download kan opleveren en pagina's te installeren, software download websites, evenals verschillende andere vaak benaderd plaatsen. Wanneer zij gebruik maken van gelijk klinkende domeinnamen aan gerenommeerde adressen en ook certificeringen bescherming van de individuen zouden kunnen worden gedwongen tot interactie met hen. In veel gevallen alleen het openen van hen kan de mijnwerker infectie activeren.
Een andere techniek zou zijn om payload service providers die kunnen worden verspreid gebruik te maken van deze benaderingen of door middel van het delen van gegevens netwerken te gebruiken, BitTorrent behoort tot een van de meest prominente. Het wordt regelmatig gebruikt om zowel legitieme software en bestanden, alsmede piraat inhoud verspreiden. 2 van één van de meest populaire payload providers zijn de volgende::
Andere methoden die door de boeven kan worden beschouwd bestaan uit gebruik te maken van browser hijackers -unsafe plugins die verenigbaar zijn gemaakt met één van de meest prominente webbrowsers. Ze worden geüpload naar de relevante databanken met nep individuele beoordelingen en ontwikkelaar kwalificaties. In de meeste gevallen kunnen de samenvattingen uit schermafbeeldingen, video's en geavanceerde beschrijvingen aansprekende grote verbeteringen van functies evenals efficiency optimalisaties. Niettemin na het instellen van de acties van de beïnvloed browsers zal veranderen- individuen zullen merken dat ze zullen worden omgeleid naar een hacker gecontroleerde landing page evenals hun opstellingen kunnen worden gewijzigd – de standaard webpagina, zoekmachine en nieuwe tabbladen pagina.

Vsmic.exe: Analyse
The Vsmic.exe malware is a classic instance of a cryptocurrency miner which depending on its setup can trigger a wide array of unsafe actions. Its major objective is to carry out complicated mathematical tasks that will certainly make the most of the offered system resources: processor, GPU, geheugen en ook de harde schijf ruimte. The way they function is by linking to an unique web server called mining swimming pool where the needed code is downloaded and install. Zodra een van de banen wordt gedownload zal het zeker worden begonnen op hetzelfde moment, meerdere omstandigheden kunnen worden uitgevoerd op wanneer. When a given job is finished an additional one will be downloaded and install in its location as well as the loophole will proceed till the computer system is powered off, de infectie is geëlimineerd of andere vergelijkbare gebeurtenis plaatsvindt. Cryptogeld zal worden gecompenseerd voor de criminele controllers (hacken groep of een eenzame cyberpunk) direct naar hun portemonnee.
A harmful feature of this group of malware is that samples like this one can take all system resources and practically make the target computer unusable until the risk has actually been completely gotten rid of. The majority of them feature a consistent installation which makes them actually tough to remove. Deze opdrachten zullen wijzigingen ook alternatieven, configuration files as well as Windows Registry values that will certainly make the Vsmic.exe malware beginning automatically as soon as the computer is powered on. Access to recuperation menus and alternatives might be blocked which makes numerous hands-on removal overviews virtually ineffective.
Dit bepaalde infectie zal zeker de configuratie van een Windows-service voor zichzelf, following the performed protection evaluation ther adhering to actions have actually been observed:
. During the miner procedures the associated malware can link to already running Windows services and also third-party set up applications. By doing so the system administrators may not see that the source lots originates from a different process.
| Naam | Vsmic.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Vsmic.exe |

Dit soort malware-infecties zijn vooral efficiënt bij het vervullen van geavanceerde commando's als zo opgezet. They are based on a modular framework enabling the criminal controllers to coordinate all sort of hazardous habits. Onder de prominente gevallen is de aanpassing van het Windows-register – alterations strings connected by the os can cause major performance disruptions and the inability to access Windows services. Depending upon the range of changes it can likewise make the computer totally unusable. On the various other hand manipulation of Registry worths coming from any kind of third-party set up applications can sabotage them. Some applications may fail to release completely while others can all of a sudden quit working.
This certain miner in its present version is focused on extracting the Monero cryptocurrency consisting of a modified variation of XMRig CPU mining engine. If the projects show successful then future versions of the Vsmic.exe can be introduced in the future. Als de malware gebruik maakt van de zwakke plekken in software om de beoogde gastheer te infecteren, het kan zijn onderdeel van een schadelijke co-infectie met ransomware en ook Trojaanse paarden.
Elimination of Vsmic.exe is strongly suggested, given that you run the risk of not just a large electrical energy bill if it’s operating on your PC, however the miner might likewise carry out other undesirable activities on it and also even damage your PC permanently.
Vsmic.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Vsmic.exe
STAP 5. Vsmic.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Vsmic.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Vsmic.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Vsmic.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Vsmic.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Vsmic.exe”.







