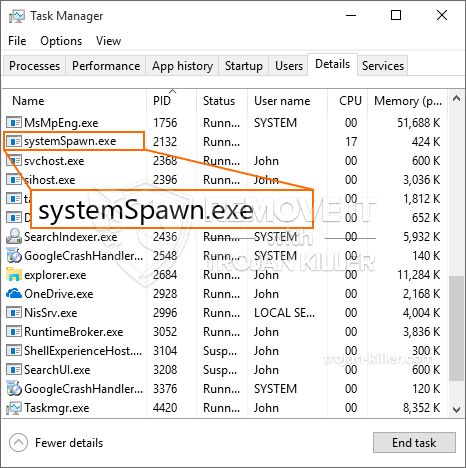
Een gloednieuw, zeer onveilige cryptocurrency-mijnwerkerinfectie is daadwerkelijk opgemerkt door beveiligingsonderzoekers. de malware, riep SystemSpawn.exe kan doelslachtoffers infecteren door gebruik te maken van een aantal manieren. Het belangrijkste idee achter de SystemSpawn.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten in te zetten op de computers van doelen om Monero-symbolen te verkrijgen tegen doelenkosten. The end result of this miner is the raised electricity expenses as well as if you leave it for longer amount of times SystemSpawn.exe may even damage your computer systems elements.
SystemSpawn.exe: distributiemethoden
De SystemSpawn.exe malware utilizes two prominent methods which are utilized to contaminate computer targets:
- Payload Levering via Prior Infecties. If an older SystemSpawn.exe malware is released on the victim systems it can immediately update itself or download and install a more recent version. This is possible through the built-in update command which obtains the release. Dit gebeurt door het koppelen van een specifieke vooraf bepaalde hacker-gecontroleerde server die de malware code voorziet. The downloaded and install infection will acquire the name of a Windows service as well as be positioned in the “%systeem% temp” Gebied. Vital residential or commercial properties and also operating system setup data are changed in order to allow a relentless as well as quiet infection.
- Software programma Kwetsbaarheid Exploits. The most current variation of the SystemSpawn.exe malware have been located to be caused by the some exploits, beroemde erkend voor wordt gebruik gemaakt van in de ransomware aanslagen. De infecties worden gedaan door zich te richten geopend diensten door middel van de TCP-poort. De slagen worden geautomatiseerd door een hacker gecontroleerd kader dat bedoeld indien de poort open. If this condition is satisfied it will certainly scan the service as well as obtain information regarding it, consisting of any type of variation and also configuration data. Ventures en ook prominente gebruikersnaam en ook wachtwoordmixen kunnen worden gedaan. Wanneer de exploit wordt geactiveerd tegen de kwetsbare code, zal de miner zeker samen met de achterdeur worden ingezet. Dit zal zeker zorgen voor de dubbele infectie.
Aside from these methods various other methods can be utilized as well. Miners can be distributed by phishing e-mails that are sent out wholesale in a SPAM-like way and rely on social design techniques in order to puzzle the sufferers right into believing that they have gotten a message from a genuine solution or firm. The infection documents can be either directly attached or put in the body materials in multimedia material or text web links.
The crooks can additionally produce harmful touchdown pages that can impersonate supplier download and install pages, software application download portals and various other regularly accessed places. When they make use of comparable seeming domain names to reputable addresses as well as security certifications the customers may be pushed right into connecting with them. Soms alleen het openen van hen kan de mijnwerker infectie veroorzaken.
Another method would certainly be to make use of haul service providers that can be spread out utilizing the above-mentioned methods or by means of file sharing networks, BitTorrent is slechts een van de meest populaire. It is regularly utilized to disperse both genuine software as well as data and also pirate content. 2 of the most popular payload carriers are the following:
Other techniques that can be taken into consideration by the bad guys consist of using browser hijackers -unsafe plugins which are made compatible with the most popular internet browsers. They are uploaded to the appropriate databases with fake user testimonials and designer credentials. In veel gevallen kunnen de beschrijvingen screenshots bevatten, videos and also fancy descriptions promising wonderful attribute improvements and efficiency optimizations. However upon setup the habits of the impacted internet browsers will certainly change- individuals will certainly discover that they will be rerouted to a hacker-controlled touchdown page and their settings could be modified – de standaard webpagina, zoekmachine evenals gloednieuwe tabs pagina.
SystemSpawn.exe: Analyse
The SystemSpawn.exe malware is a timeless case of a cryptocurrency miner which relying on its configuration can create a variety of unsafe activities. Its primary objective is to do complex mathematical tasks that will take advantage of the available system resources: processor, GPU, geheugen evenals harde schijf ruimte. De methode die ze bedienen is door het verbinden met een unieke server genaamd mijnbouw zwembad waar de opgeroepen tot code is gedownload en geïnstalleerd. Zodra een van de banen wordt gedownload zal het zeker worden gelijktijdig begonnen, meerdere omstandigheden kunnen worden gegaan voor zodra. When a given task is completed another one will certainly be downloaded and install in its location and also the loophole will certainly continue till the computer is powered off, de infectie wordt verwijderd of er vindt nog een soortgelijke gebeurtenis plaats. Cryptogeld zal beloond worden naar de correctionele controllers (hacken groep of een eenzame cyberpunk) direct naar hun portemonnee.
A hazardous characteristic of this classification of malware is that samples like this one can take all system sources and virtually make the target computer system unusable up until the threat has actually been totally removed. A lot of them feature a consistent installation which makes them truly challenging to get rid of. Deze commando's zullen zeker aanpassingen om keuzes te starten maken, configuration data and also Windows Registry values that will certainly make the SystemSpawn.exe malware begin automatically as soon as the computer system is powered on. Accessibility to recovery menus and also alternatives may be blocked which provides several hand-operated elimination overviews almost worthless.
Deze bepaalde infectie zal zeker een Windows-service voor zichzelf regelen, adhering to the performed safety evaluation ther following actions have been observed:
. During the miner procedures the linked malware can hook up to already running Windows solutions as well as third-party installed applications. By doing so the system managers might not notice that the source tons originates from a separate procedure.
| Naam | SystemSpawn.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove SystemSpawn.exe |
id =”82563″ align =”aligncenter” width =”600″]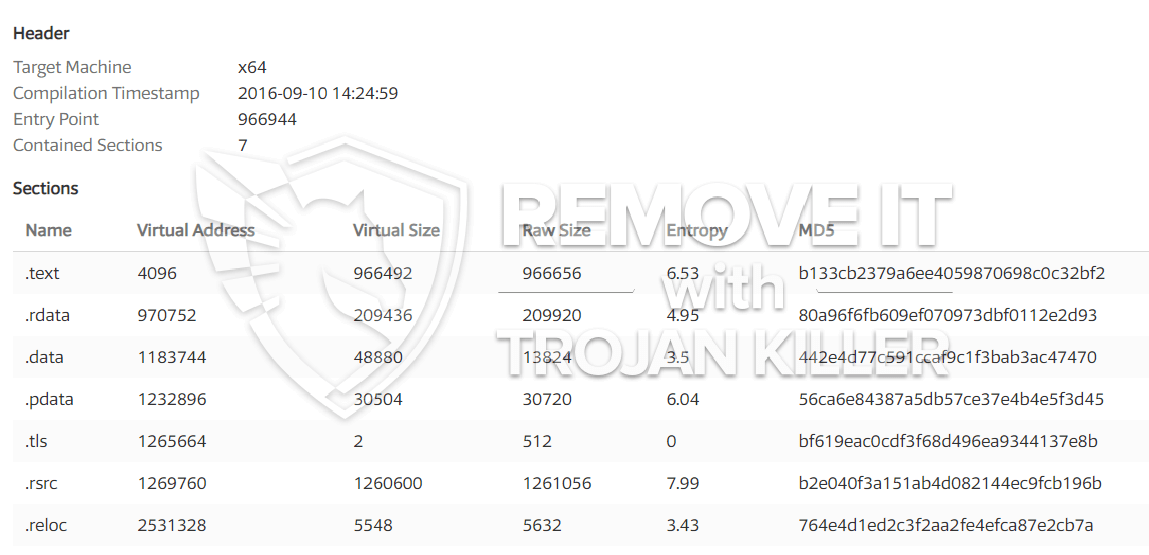 SystemSpawn.exe
SystemSpawn.exe
These kind of malware infections are especially effective at executing innovative commands if set up so. They are based on a modular structure allowing the criminal controllers to manage all sort of dangerous habits. Een van de belangrijkste voorbeelden is de wijziging van het Windows-register – adjustments strings connected by the operating system can cause serious efficiency interruptions and also the inability to gain access to Windows solutions. Relying on the extent of changes it can additionally make the computer completely pointless. On the other hand manipulation of Registry values coming from any type of third-party set up applications can undermine them. Sommige toepassingen te kort zou schieten om volledig vrij te geven, terwijl anderen onverwacht werken kan stoppen.
This specific miner in its current version is concentrated on mining the Monero cryptocurrency having a customized version of XMRig CPU mining engine. If the projects confirm effective after that future variations of the SystemSpawn.exe can be released in the future. Aangezien de malware softwarekwetsbaarheden gebruikt om doelhosts te besmetten, het kan een deel van een gevaarlijke co-infectie met ransomware zijn evenals Trojans.
Removal of SystemSpawn.exe is highly recommended, gezien het feit dat je niet zomaar een grote elektrische energierekening riskeren als het werkt op uw computer, however the miner may additionally execute other unwanted tasks on it as well as even harm your PC completely.
SystemSpawn.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove SystemSpawn.exe
STAP 5. SystemSpawn.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove SystemSpawn.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “SystemSpawn.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “SystemSpawn.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “SystemSpawn.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “SystemSpawn.exe”.