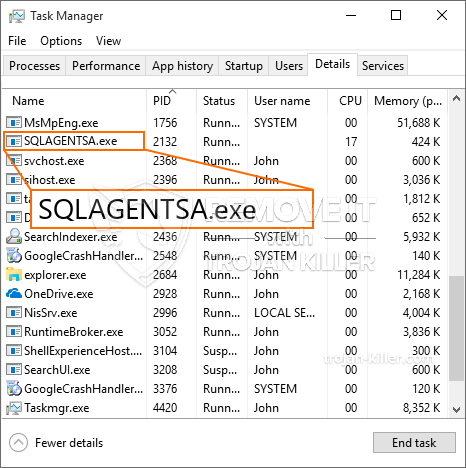
Een nieuw, zeer onveilig cryptogeld mijnwerker virus is geïdentificeerd door de veiligheid van wetenschappers. de malware, riep SQLAGENTSA.exe infecteren doel slachtoffers gebruikmaking van een selectie van middelen. The main point behind the SQLAGENTSA.exe miner is to utilize cryptocurrency miner tasks on the computer systems of sufferers in order to obtain Monero tokens at victims expenditure. The outcome of this miner is the elevated electricity expenses and also if you leave it for longer periods of time SQLAGENTSA.exe may even harm your computer systems parts.
SQLAGENTSA.exe: distributiemethoden
De SQLAGENTSA.exe malware gebruikt twee belangrijke technieken die gebruik maken van de computer doelen infecteren gemaakt:
- Payload Levering via Prior Infecties. If an older SQLAGENTSA.exe malware is deployed on the victim systems it can instantly update itself or download and install a newer version. This is feasible using the built-in update command which acquires the launch. Dit gebeurt door aan een bepaald vooraf-hacker gecontroleerde server die de malware code biedt. The downloaded and install infection will certainly obtain the name of a Windows service as well as be put in the “%systeem% temp” plaats. Vital residential or commercial properties and operating system setup documents are changed in order to allow a persistent and also quiet infection.
- Software Application Vulnerability Exploits. The most recent version of the SQLAGENTSA.exe malware have actually been found to be triggered by the some exploits, bekend om te worden gebruikt bij de ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De aanslagen worden geautomatiseerd door een hacker bestuurde structuur die zoekt uit of de poort open. If this condition is satisfied it will check the service and recover details about it, consisting of any type of version and configuration data. Ventures and prominent username as well as password combinations may be done. When the make use of is triggered versus the susceptible code the miner will be released together with the backdoor. Dit zal zeker zorgen voor de dubbele infectie.
Apart from these approaches various other strategies can be utilized too. Miners can be distributed by phishing emails that are sent out in bulk in a SPAM-like way as well as depend upon social design techniques in order to confuse the victims into thinking that they have actually received a message from a genuine solution or firm. The infection files can be either straight attached or put in the body contents in multimedia material or message links.
The criminals can additionally produce destructive landing web pages that can pose vendor download pages, software program download sites and also other frequently accessed areas. When they make use of comparable sounding domain names to genuine addresses and safety certifications the individuals might be coerced right into communicating with them. In sommige gevallen kan het simpelweg openen ervan de mijnwerker-infectie veroorzaken.
An additional approach would be to use haul service providers that can be spread out making use of the above-mentioned techniques or by means of documents sharing networks, BitTorrent behoort tot een van de meest prominente. It is often utilized to disperse both legit software program and also files and pirate material. 2 van een van de meest populaire payload-serviceproviders zijn de volgende::
Other techniques that can be considered by the bad guys include using internet browser hijackers -dangerous plugins which are made compatible with the most popular web browsers. They are published to the pertinent repositories with phony customer reviews and also programmer qualifications. Vaak bevatten de samenvattingen schermafbeeldingen, video clips and also fancy descriptions appealing excellent attribute improvements and also efficiency optimizations. Maar bij aflevering van de acties van de getroffen browsers zal zeker transformeren- individuals will certainly discover that they will certainly be redirected to a hacker-controlled landing web page and their settings may be changed – de standaard webpagina, zoekmachine en ook gloednieuwe tabs webpagina.

SQLAGENTSA.exe: Analyse
The SQLAGENTSA.exe malware is a traditional instance of a cryptocurrency miner which depending on its setup can create a variety of dangerous activities. Its primary objective is to carry out complicated mathematical jobs that will make the most of the readily available system sources: processor, GPU, geheugen en harde schijf ruimte. The means they function is by attaching to an unique web server called mining pool where the called for code is downloaded. Zodra een van de taken wordt gedownload, wordt deze meteen gestart, verschillende gevallen kunnen worden uitgevoerd tegelijkertijd. When a provided task is finished an additional one will be downloaded and install in its location and the loop will proceed until the computer is powered off, de infectie wordt verwijderd of er gebeurt een andere vergelijkbare gebeurtenis. Cryptogeld zal zeker worden gecompenseerd naar de correctionele controllers (hacken groep of een eenzame cyberpunk) direct naar hun portemonnee.
A dangerous characteristic of this classification of malware is that samples such as this one can take all system sources and also virtually make the victim computer system pointless till the threat has actually been totally eliminated. A lot of them include a relentless installment that makes them truly tough to remove. Deze opdrachten zullen wijzigingen ook alternatieven, configuration documents and also Windows Registry values that will make the SQLAGENTSA.exe malware beginning automatically as soon as the computer is powered on. Accessibility to healing menus and options might be obstructed which renders lots of hands-on elimination overviews practically worthless.
Deze specifieke infectie zal zeker arrangement een Windows-service voor zichzelf, following the conducted protection evaluation ther following actions have actually been observed:
. During the miner operations the associated malware can link to currently running Windows solutions as well as third-party mounted applications. By doing so the system administrators might not see that the resource load comes from a separate procedure.
| Naam | SQLAGENTSA.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove SQLAGENTSA.exe |

These kind of malware infections are especially reliable at carrying out sophisticated commands if configured so. Ze zijn gebaseerd op een modulaire structuur die de criminele controleurs in staat stelt om allerlei soorten onveilige gewoonten te orkestreren. Onder de populaire gevallen is de aanpassing van het Windows-register – adjustments strings related by the os can cause severe efficiency disturbances as well as the lack of ability to gain access to Windows services. Depending on the scope of changes it can likewise make the computer system entirely pointless. On the other hand manipulation of Registry values belonging to any kind of third-party set up applications can undermine them. Some applications might fall short to introduce altogether while others can suddenly quit working.
This certain miner in its existing variation is concentrated on extracting the Monero cryptocurrency having a changed version of XMRig CPU mining engine. If the projects show successful then future variations of the SQLAGENTSA.exe can be introduced in the future. Als de malware maakt gebruik van software susceptabilities te infecteren doelhosts, Het kan deel uitmaken van een onveilige co-infectie met ransomware en Trojaanse paarden.
Elimination of SQLAGENTSA.exe is highly advised, because you take the chance of not just a large power bill if it is operating on your PC, but the miner might likewise execute other unwanted tasks on it and also damage your PC permanently.
SQLAGENTSA.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove SQLAGENTSA.exe
STAP 5. SQLAGENTSA.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove SQLAGENTSA.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “SQLAGENTSA.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “SQLAGENTSA.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “SQLAGENTSA.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “SQLAGENTSA.exe”.







