Een gloednieuw, zeer schadelijk cryptogeld mijnwerker infectie daadwerkelijk is geïdentificeerd door de veiligheid van wetenschappers. de malware, riep Scesrv.exe kunnen besmetten doel patiënten gebruik te maken van een reeks van manieren. De essentie achter de Scesrv.exe mijnwerker is om cryptogeld mijnwerker activiteiten te gebruiken op de computersystemen van het slachtoffer in om Monero verkrijgen tokens op doelen kosten. Het eindresultaat van deze mijnwerker is de verhoogde elektrische energierekening en ook als je laat het voor een langere aantal keren Scesrv.exe wellicht ook uw computer systemen onderdelen beschadigt.
Scesrv.exe: distributiemethoden
De Scesrv.exe malware maakt gebruik van twee geprefereerde methoden die worden gebruikt voor het computersysteem doelen infecteren:
- Payload Levering via Prior Infecties. Als een oudere Scesrv.exe malware wordt vrijgegeven op het doel systemen kunnen het zich direct bij te werken of download een recentere versie. Dit is mogelijk door de geïntegreerde upgrade commando dat de lancering krijgt. Dit gebeurt door het koppelen van een speciaal vooraf bepaald hacker-gecontroleerde server die de malware code levert. De gedownloade virus zal de naam van een Windows-oplossing verwerven en worden geplaatst in de “%systeem% temp” plaats. Cruciaal residentiële of commerciële onroerend goed en installeren van het besturingssysteem documenten worden veranderd om een blijvende en stille infectie toestaan.
- Software programma Kwetsbaarheid Exploits. De nieuwste variant van de Scesrv.exe malware daadwerkelijk zijn gevonden door het aantal ondernemingen te worden gebracht, algemeen begrepen te worden gebruikt in de ransomware aanslagen. De infecties worden gedaan door zich te richten geopend oplossingen met behulp van de TCP-poort. De aanvallen worden geautomatiseerd door een hacker bestuurde structuur die opgezocht als de poort open. Als aan deze voorwaarde wordt voldaan zal het zeker scant de service en ook informatie te herstellen erover, bestaande uit elk type versie en ook de installatie-informatie. Exploits en ook de voorkeur gebruikersnaam en wachtwoord mixen zou kunnen worden gedaan. Wanneer de exploit geactiveerd tegen buikligging code mijnwerkers zeker tezamen ook worden bediend via de achterdeur. Dit zal het een dubbele infectie bieden.
Afgezien van deze methoden andere strategieën kunnen ook worden gebruikt. Mijnwerkers kan worden verspreid door phishing e-mails in bulk in een SPAM-achtige wijze worden verzonden en afhankelijk sociale ontwerptechnieken om de patiënten puzzel te geloven dat zij een boodschap hebben verkregen van een betrouwbare oplossing of firma. De infectie gegevens kunnen direct worden bevestigd of geplaatst in het lichaam stoffen in multimediaal materiaal of bericht weblinks.
De criminelen kunnen produceren daarbij kwaadaardige landing pages die leverancier download kan opleveren en pagina's te installeren, softwareprogramma downloaden portals en ook andere regelmatig benaderd plaatsen. Wanneer zij gebruik maken van gelijk klinkende domein gerenommeerde adressen en veiligheid en beveiligingscertificaten de gebruikers kan worden overgehaald tot in contact met ze hebben. Soms alleen het openen van hen kan de mijnwerker infectie veroorzaken.
Een andere benadering zou zijn om gebruik te maken van de payload service providers die kunnen worden verspreid met behulp van deze technieken of door middel van het delen van gegevens netwerken, BitTorrent is slechts een van de meest geprefereerde. Het wordt vaak gebruikt om zowel legale software te verspreiden en ook bestanden evenals piraat web content. 2 van de meest geprefereerde haul service providers zijn de volgende:
Diverse andere benaderingen die in aanmerking door de criminelen kunnen worden gehouden met het gebruik van browser hijackers -Schadelijk plugins die verenigbaar zijn gemaakt met één van de meest prominente internet browsers. Ze zijn gepubliceerd om de relevante databases met nep individuele evaluaties, alsmede de ontwikkelaar kwalificaties. In de meeste gevallen zijn de samenvattingen kunnen zijn screenshots, videos evenals geavanceerde samenvattingen aantrekkelijk grote functie verbeteringen en prestaties optimalisaties. Niettemin na het instellen van de acties van de getroffen browsers zal veranderen- gebruikers zal zeker merken dat ze zeker zullen worden omgeleid naar een hacker gecontroleerde touchdown pagina en hun instellingen kunnen worden gewijzigd – de standaard webpagina, internet zoekmachine en gloednieuwe tabs pagina.

Scesrv.exe: Analyse
De Scesrv.exe malware is een klassieke situatie van een cryptogeld miner die afhankelijk van de configuratie uiteenlopende onveilige activiteiten kunnen leiden. De belangrijkste doelstelling is complexe wiskundige banen die zullen profiteren van de direct beschikbare systeembronnen uit te voeren: processor, GPU, geheugen en ook de harde schijf ruimte. De methode die ze werken is door het aan te sluiten op een speciale webserver genaamd mining zwembad waar de benodigde code wordt gedownload. Zodra één van de taken is gedownload zal het zeker worden gestart op hetzelfde moment, meerdere omstandigheden kunnen zo snel worden uitgevoerd bij. Wanneer een voorwaarde opdracht is voltooid een extra zal zeker worden gedownload en geïnstalleerd in zijn gebied, evenals de maas in de wet zeker zal doorgaan totdat de computer is uitgeschakeld, de infectie wordt weggedaan of één meer vergelijkbare gelegenheid gebeurt. Cryptogeld zal worden gecompenseerd voor de criminele controllers (hacken groep of een eenzame hacker) rechtstreeks naar hun begrotingen.
Een schadelijke kenmerk van deze groep van malware is dat monsters als deze alle systeem bronnen kan nemen en ook praktisch maken de doelcomputer systeem zinloos tot het risico volledig is verwijderd. De meerderheid van hen zijn onder andere een hardnekkige setup waardoor ze echt uitdagend om te verwijderen. Deze commando's zullen veranderingen ook opties maken, setup-bestanden en ook Windows-register waarden die zeker zal maken van de Scesrv.exe malware direct aan de slag zodra de computer wordt ingeschakeld. Toegang tot recuperatie menu's en keuzes kunnen worden belemmerd worden verleend, wegens verschillende handmatige verwijdering begeleidt bijna waardeloos.
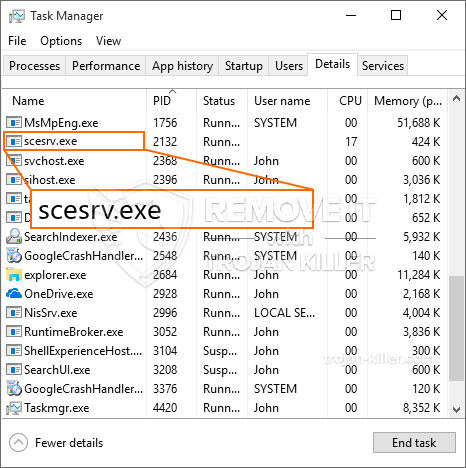
Dit bepaalde infectie zal zeker de configuratie van een Windows-service voor zichzelf, naar aanleiding van de uitgevoerde veiligheid en de beoordeling beveiliging ther volgende activiteiten daadwerkelijk zijn waargenomen:
. Tijdens de mijnwerker procedures kunnen de aangesloten malware hechten aan al met Windows oplossingen, alsmede van derden geïnstalleerde toepassingen. Door dit te doen zodat het systeem managers misschien niet zien dat de bron belasting afkomstig is van een afzonderlijke procedure.
| Naam | Scesrv.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware op te sporen en te verwijderen Scesrv.exe |

Dit soort malware-infecties zijn vooral betrouwbaar bij het uitvoeren van geavanceerde commando's, indien zo ingesteld. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controllers om allerlei gevaarlijke gedrag te coördineren. Onder de prominente gevallen is de wijziging van het Windows-register – wijzigingen strings met elkaar verbonden door de os kan aanzienlijke efficiëntie storingen en ook het onvermogen om Windows services toegankelijkheid te creëren. Afhankelijk van de omvang van de wijzigingen die zij kan eveneens maken van de computer volledig onbruikbaar. Aan de andere kant de controle over Registry waardes afkomstig van elke vorm van derden opgezet toepassingen kan ze saboteren. Sommige toepassingen kunnen stoppen met werken om volledig vrij te geven, terwijl anderen kan plotseling gestopt met werken.
Dit bepaalde miner in zijn huidige variant is gericht op de mijnbouw Monero cryptogeld met een veranderde variatie van XMRig CPU mining engine. Als het project succesvol controleren na dat toekomstige variaties van de Scesrv.exe kan in de toekomst worden ingevoerd. Als de malware maakt gebruik van softwareprogramma susceptabilities tot doel gastheren besmetten, het kan een deel van een gevaarlijke co-infectie met ransomware zijn evenals Trojans.
Verwijdering van Scesrv.exe is sterk aangeraden, omdat je de kans niet alleen een grote energierekening te nemen als het werkt op uw computer, maar de mijnwerker zou hetzelfde doen diverse andere ongewenste taken op het zo goed als ook schade toebrengen aan uw computer permanent.
Scesrv.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Scesrv.exe verwijderen
STAP 5. Scesrv.exe verwijderd!
video Guide: Hoe wordt GridinSoft Anti-Malware gebruiken voor het verwijderen Scesrv.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Scesrv.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Scesrv.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Scesrv.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Scesrv.exe”.







