Een nieuw, extreem onveilige cryptocurrency-mijnwerkerinfectie is daadwerkelijk opgemerkt door veiligheids- en beveiligingsonderzoekers. de malware, riep Prnntfy.exe kan doelwitslachtoffers infecteren op verschillende manieren. Het belangrijkste idee achter de Prnntfy.exe-mijnwerker is om cryptocurrency-mijnertaken te gebruiken op de computersystemen van patiënten om Monero-symbolen te verwerven tegen de kosten van doelen. The result of this miner is the raised electrical energy expenses and also if you leave it for longer periods of time Prnntfy.exe may also harm your computers components.
Prnntfy.exe: distributiemethoden
De Prnntfy.exe malware maakt gebruik van 2 populaire benaderingen die worden gebruikt om computerdoelen te infecteren:
- Payload Levering via Prior Infecties. If an older Prnntfy.exe malware is released on the sufferer systems it can instantly update itself or download a more recent variation. Dit is mogelijk via de ingebouwde update-commando dat de release verkrijgt. Dit gebeurt door het koppelen van een speciaal vooraf bepaald hacker-gecontroleerde webserver die malware code levert. De gedownloade infectie krijgt de naam van een Windows-service en wordt ook in de “%systeem% temp” Gebied. Essentiële huizen en ook actieve systeemconfiguratiegegevens worden gewijzigd om een consistente en stille infectie mogelijk te maken.
- Software Vulnerability Exploits. The newest version of the Prnntfy.exe malware have been discovered to be caused by the some exploits, bekend om zijn gebruik in ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend diensten via de TCP-poort. De aanvallen worden geautomatiseerd door een hacker bestuurde structuur die zoekt uit of de poort open. Als dit probleem zich voordoet, wordt de service gescand en worden er ook details over opgehaald, inclusief elk type versie en arrangementinformatie. Ventures en preferente gebruikersnaam en ook met een wachtwoord mixen kan worden gedaan. Als de exploit wordt geactiveerd ten opzichte van de gevoelige code de mijnwerker zal worden ingezet in aanvulling op de achterdeur. Dit zal zeker bieden een dubbele infectie.
Afgezien van deze methoden verschillende andere methoden kunnen ook worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die op een SPAM-achtige manier in het groot worden verzonden, en zijn afhankelijk van social engineering-trucs om de patiënten te verwarren door te denken dat ze een bericht hebben ontvangen van een gerenommeerde service of firma.. De virusbestanden kunnen rechtstreeks worden aangebracht of in het lichaamsmateriaal in multimediamateriaal of tekstweblinks worden ingevoegd.
De boeven kunnen bovendien kwaadaardige touchdown-webpagina's ontwikkelen die de downloadwebpagina's van een leverancier kunnen nabootsen, websites voor het downloaden van softwareprogramma's en ook diverse andere veelgebruikte gebieden. Wanneer ze gebruik maken van een domein dat lijkt op echte adressen en ook van beschermingscertificaten, kunnen de individuen worden overgehaald om met hen om te gaan. In sommige gevallen alleen het openen van hen kan de mijnwerker infectie activeren.
Een andere strategie zou zeker zijn om ladingsdragers te gebruiken die kunnen worden verspreid met behulp van de bovengenoemde benaderingen of via netwerken voor het delen van bestanden, BitTorrent is een van de meest populaire. Het wordt vaak gebruikt om zowel gerenommeerde software als documenten en ook illegaal materiaal te verspreiden. Twee van de meest geprefereerde aanbieders van transport zijn de volgende:
Other techniques that can be taken into consideration by the bad guys consist of using browser hijackers -unsafe plugins which are made compatible with one of the most preferred web browsers. They are uploaded to the relevant databases with phony user testimonials as well as developer credentials. In de meeste gevallen kan de beschrijvingen screenshots omvatten, video clips and fancy summaries encouraging wonderful feature improvements and efficiency optimizations. However upon installation the actions of the affected internet browsers will alter- users will certainly discover that they will certainly be redirected to a hacker-controlled touchdown web page as well as their settings might be altered – de standaard webpagina, zoekmachine evenals nieuwe tabbladen webpagina.

Prnntfy.exe: Analyse
The Prnntfy.exe malware is a traditional instance of a cryptocurrency miner which relying on its arrangement can create a wide variety of hazardous actions. Het belangrijkste doel is om complexe wiskundige taken uit te voeren die zeker het meeste uit de beschikbare systeembronnen zullen halen: processor, GPU, geheugen en ook de ruimte op de harde schijf. De manier waarop ze werken, is door verbinding te maken met een speciale webserver genaamd mining-zwembad, waar de benodigde code wordt gedownload. Zodra een van de taken is gedownload, wordt deze meteen gestart, talrijke gevallen kan worden gegaan voor een keer. Wanneer een aangeboden baan is voltooid, zal er zeker een extra worden gedownload op zijn locatie en de maas in de wet zal doorgaan totdat de computer wordt uitgeschakeld, de infectie wordt verwijderd of extra vergelijkbare gebeurtenis plaatsvindt. Cryptogeld zal worden toegekend aan de criminele controllers (hacken team of een eenzame hacker) direct naar hun portemonnee.
Een schadelijk kenmerk van deze classificatie van malware is dat voorbeelden zoals deze alle systeembronnen kunnen nemen en de computer van het slachtoffer praktisch zinloos kunnen maken totdat het risico daadwerkelijk volledig is geëlimineerd. De meeste hebben een aanhoudende installatie waardoor ze eigenlijk een uitdaging zijn om er vanaf te komen. Deze commando's zullen zeker aanpassingen maken in keuzes, configuration files as well as Windows Registry values that will make the Prnntfy.exe malware beginning automatically as soon as the computer is powered on. De toegankelijkheid van voedselkeuzes en alternatieven voor recuperatie kan worden belemmerd, wat talrijke handbediende eliminatieoverzichten praktisch onbruikbaar maakt.
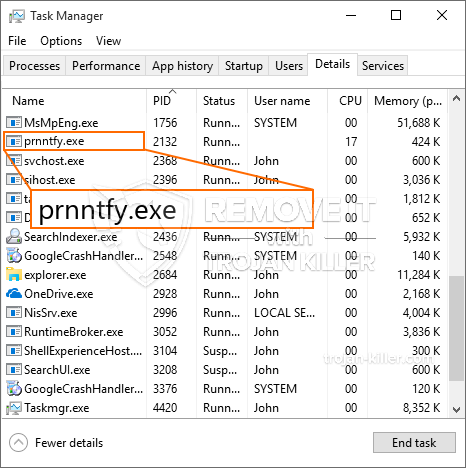
Dit bepaalde infectie zal opstelling een Windows-service voor zichzelf, na de uitgevoerde beschermingsanalyse zijn er volgende activiteiten waargenomen:
. Tijdens de mijnwerkzaamheden kan de gekoppelde malware verbinding maken met Windows-services die momenteel worden uitgevoerd en met applicaties van derden. Hierdoor merken de systeembeheerders mogelijk niet dat de bronbelasting afkomstig is van een afzonderlijke procedure.
| Naam | Prnntfy.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Prnntfy.exe |

Dit soort malware-infecties zijn bijzonder effectief bij het uitvoeren van innovatieve opdrachten, indien zo ingesteld. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controleurs allerlei gevaarlijke gewoonten kunnen orkestreren. Een van de geprefereerde voorbeelden is de wijziging van het Windows-register – alterations strings related by the os can cause significant performance disruptions and the inability to accessibility Windows services. Relying on the extent of adjustments it can additionally make the computer completely pointless. On the other hand manipulation of Registry worths coming from any kind of third-party mounted applications can undermine them. Some applications might stop working to release entirely while others can all of a sudden quit working.
This particular miner in its existing version is focused on extracting the Monero cryptocurrency having a changed variation of XMRig CPU mining engine. If the campaigns show effective then future versions of the Prnntfy.exe can be released in the future. Als de malware maakt gebruik van software programma kwetsbaarheden te besmetten doelhosts, het kan onderdeel van een gevaarlijke co-infectie met ransomware zo goed als Trojaanse paarden.
Removal of Prnntfy.exe is highly recommended, given that you run the risk of not just a huge power expense if it is running on your PC, however the miner might likewise perform various other unwanted tasks on it and also harm your COMPUTER permanently.
Prnntfy.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Prnntfy.exe
STAP 5. Prnntfy.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Prnntfy.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Prnntfy.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Prnntfy.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Prnntfy.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Prnntfy.exe”.







