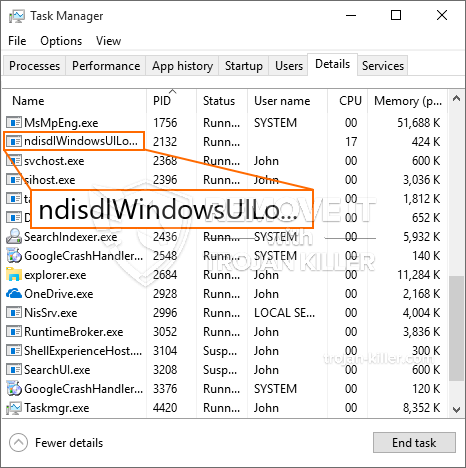
Een gloednieuw, really unsafe cryptocurrency miner virus has been detected by protection researchers. de malware, riep NdisdlWindowsUILogon.exe infecteren doel patiënten gebruik van een selectie van middelen. The essence behind the NdisdlWindowsUILogon.exe miner is to use cryptocurrency miner tasks on the computer systems of sufferers in order to acquire Monero tokens at sufferers expenditure. The outcome of this miner is the raised power costs as well as if you leave it for longer time periods NdisdlWindowsUILogon.exe may also damage your computers parts.
NdisdlWindowsUILogon.exe: distributiemethoden
De NdisdlWindowsUILogon.exe malware uses two preferred techniques which are made use of to contaminate computer system targets:
- Payload Delivery gebruik Prior Infecties. If an older NdisdlWindowsUILogon.exe malware is released on the victim systems it can instantly upgrade itself or download a newer version. This is possible via the built-in update command which acquires the launch. Dit gebeurt door aan een bepaald vooraf gedefinieerd hacker-gecontroleerde server die de malware code levert. De gedownloade en geïnstalleerde infectie krijgt zeker de naam van een Windows-service en wordt in de “%systeem% temp” plaats. Essential buildings and also operating system arrangement data are changed in order to allow a relentless and silent infection.
- Software programma Kwetsbaarheid Exploits. The newest variation of the NdisdlWindowsUILogon.exe malware have actually been discovered to be brought on by the some exploits, volksmond erkend te worden gebruikt in de ransomware strikes. De infecties worden gedaan door zich te richten geopend diensten door middel van de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die opgezocht als de poort open. If this problem is met it will check the service as well as fetch information regarding it, bestaande uit elk type variatie en informatie over de arrangementen. Exploits en populaire gebruikersnaam en wachtwoord mixen kan worden gedaan. When the manipulate is triggered versus the susceptible code the miner will certainly be deployed along with the backdoor. Dit zal een dubbele infectie presenteren.
Apart from these methods other strategies can be used too. Miners can be distributed by phishing emails that are sent wholesale in a SPAM-like fashion and depend upon social design methods in order to perplex the targets into believing that they have actually received a message from a legitimate solution or company. The infection data can be either directly connected or inserted in the body components in multimedia web content or text web links.
The crooks can likewise develop malicious touchdown pages that can pose vendor download web pages, software program download sites and also various other regularly accessed areas. When they utilize comparable sounding domain to genuine addresses and security certifications the individuals might be persuaded into engaging with them. In sommige gevallen alleen het openen van hen kan de mijnwerker een infectie veroorzaken.
One more technique would be to use haul carriers that can be spread out using those techniques or using data sharing networks, BitTorrent behoort tot een van de meest prominente. It is regularly utilized to disperse both genuine software program and also data as well as pirate material. Two of the most prominent haul providers are the following:
Other approaches that can be considered by the bad guys consist of the use of web browser hijackers -unsafe plugins which are made compatible with the most preferred web internet browsers. They are posted to the appropriate repositories with phony user reviews and also designer qualifications. In de meeste gevallen kan de beschrijvingen uit schermafbeeldingen, videos as well as sophisticated summaries encouraging wonderful function improvements and efficiency optimizations. Nonetheless upon setup the habits of the influenced internet browsers will certainly change- customers will certainly discover that they will be redirected to a hacker-controlled touchdown page and their settings could be modified – de standaard startpagina, zoekmachine evenals nieuwe tabbladen webpagina.

NdisdlWindowsUILogon.exe: Analyse
The NdisdlWindowsUILogon.exe malware is a timeless case of a cryptocurrency miner which depending upon its configuration can cause a wide range of dangerous actions. Its main objective is to carry out complex mathematical tasks that will make the most of the offered system resources: processor, GPU, geheugen en harde schijf ruimte. The means they operate is by attaching to a special web server called mining pool from where the required code is downloaded. Zodra één van de taken is gedownload zal worden gestart op hetzelfde moment, tal van omstandigheden kan worden gegaan voor zodra. When an offered task is completed another one will certainly be downloaded and install in its location and the loophole will certainly continue till the computer system is powered off, de infectie wordt verwijderd of extra vergelijkbare gebeurtenis plaatsvindt. Cryptogeld zal zeker beloond worden naar de correctionele controllers (hacken groep of een enkele hacker) rechtstreeks naar hun begrotingen.
A harmful quality of this category of malware is that samples like this one can take all system sources and virtually make the victim computer unusable till the hazard has actually been completely eliminated. A lot of them feature a relentless installment that makes them actually hard to get rid of. Deze opdrachten zullen zeker wijzigingen aanbrengen in opstartalternatieven, configuration documents and Windows Registry values that will certainly make the NdisdlWindowsUILogon.exe malware start immediately once the computer is powered on. Access to recovery food selections as well as choices may be blocked which renders several hand-operated removal overviews almost worthless.
Deze specifieke infectie zal zeker het opzetten van een Windows-service voor zichzelf, complying with the performed safety and security evaluation ther adhering to activities have actually been observed:
. During the miner operations the connected malware can hook up to currently running Windows solutions as well as third-party mounted applications. By doing so the system administrators might not discover that the source lots originates from a different procedure.
| Naam | NdisdlWindowsUILogon.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove NdisdlWindowsUILogon.exe |

These sort of malware infections are particularly effective at accomplishing sophisticated commands if configured so. They are based upon a modular structure permitting the criminal controllers to manage all sort of harmful habits. Een van de belangrijkste voorbeelden is de wijziging van het Windows-register – alterations strings related by the operating system can trigger significant efficiency interruptions and the inability to accessibility Windows solutions. Depending upon the extent of changes it can likewise make the computer totally unusable. Aan de andere kant aanpassing van de Register-waardes die behoren tot elke vorm van derden opgezet toepassingen kan ze saboteren. Some applications may fail to introduce entirely while others can unexpectedly stop working.
This particular miner in its present version is concentrated on mining the Monero cryptocurrency containing a customized version of XMRig CPU mining engine. If the campaigns show successful after that future versions of the NdisdlWindowsUILogon.exe can be launched in the future. Als de malware maakt gebruik van software susceptabilities tot doel gastheren besmetten, het kan onderdeel van een gevaarlijke co-infectie met ransomware zo goed als Trojaanse paarden.
Removal of NdisdlWindowsUILogon.exe is strongly recommended, since you run the risk of not only a huge electricity expense if it is working on your COMPUTER, but the miner might likewise perform other unwanted activities on it as well as even harm your PC completely.
NdisdlWindowsUILogon.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove NdisdlWindowsUILogon.exe
STAP 5. NdisdlWindowsUILogon.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove NdisdlWindowsUILogon.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “NdisdlWindowsUILogon.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “NdisdlWindowsUILogon.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “NdisdlWindowsUILogon.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “NdisdlWindowsUILogon.exe”.







