Een gloednieuw, echt schadelijk cryptogeld mijnwerker virus daadwerkelijk is ontdekt door wetenschappers bescherming. de malware, riep Lsma.exe kunnen besmetten doel patiënten gebruik van een selectie van middelen. De essentie achter de Lsma.exe-mijnwerker is het gebruik van cryptocurrency-mijnwerkeractiviteiten op de computersystemen van patiënten om Monero-tokens te verwerven op kosten van de patiënt.. The result of this miner is the raised power costs and also if you leave it for longer amount of times Lsma.exe may even damage your computer systems parts.
Lsma.exe: distributiemethoden
De Lsma.exe malware maakt gebruik van 2 voorkeurstechnieken die worden gebruikt om doelen computersysteem infecteren:
- Payload Delivery gebruik Prior Infecties. If an older Lsma.exe malware is released on the target systems it can immediately upgrade itself or download and install a more recent version. Dit is mogelijk met behulp van de ingebouwde update-commando dat de release verwerft. Dit wordt gedaan door aansluiting op een speciaal vooraf bepaald hacker-gecontroleerde server die de malware code biedt. The downloaded and install virus will certainly obtain the name of a Windows solution as well as be put in the “%systeem% temp” plaats. Vital buildings and running system arrangement files are changed in order to allow a persistent and also quiet infection.
- Software Vulnerability Exploits. The most recent version of the Lsma.exe malware have been located to be caused by the some exploits, algemeen begrepen omdat het werd gebruikt bij de ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend diensten met behulp van de TCP-poort. De aanslagen worden geautomatiseerd door een hacker bestuurde structuur die opgezocht als de poort open. If this problem is met it will certainly check the service as well as obtain info concerning it, inclusief alle soorten versies en instellingsgegevens. Ventures evenals populaire gebruikersnaam en ook met een wachtwoord combinaties kunnen worden gedaan. When the exploit is activated versus the vulnerable code the miner will be released along with the backdoor. Dit zal het een dubbele infectie.
Naast deze technieken kunnen ook verschillende andere benaderingen worden gebruikt. Miners can be distributed by phishing emails that are sent wholesale in a SPAM-like manner and depend upon social design tricks in order to confuse the victims into thinking that they have obtained a message from a reputable service or firm. The virus data can be either straight attached or put in the body contents in multimedia material or text web links.
The bad guys can additionally produce harmful landing web pages that can pose vendor download and install web pages, websites voor het downloaden van softwareapplicaties en andere vaak bezochte locaties. When they use comparable sounding domain to reputable addresses and also security certificates the individuals may be coerced right into engaging with them. Soms zijn ze gewoon te openen kan de mijnwerker een infectie veroorzaken.
One more approach would be to utilize haul service providers that can be spread out making use of those methods or through documents sharing networks, BitTorrent behoort tot een van de meest populaire. It is often utilized to distribute both genuine software application and data and pirate web content. 2 van de meest prominente vervoerders zijn de volgende::
Various other techniques that can be taken into consideration by the offenders consist of making use of internet browser hijackers -harmful plugins which are made suitable with the most preferred internet browsers. They are published to the relevant repositories with phony customer reviews and programmer qualifications. In veel gevallen kan de beschrijvingen bestaan uit screenshots, videos and fancy summaries appealing great function enhancements and performance optimizations. However upon installation the habits of the affected web browsers will change- individuals will find that they will certainly be rerouted to a hacker-controlled touchdown page and also their setups may be modified – de standaard startpagina, internet zoekmachine en ook nieuwe tabbladen webpagina.

Lsma.exe: Analyse
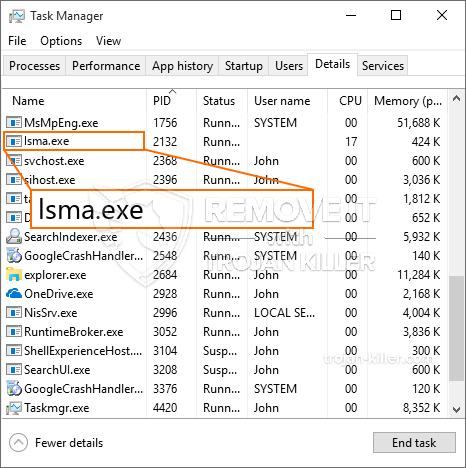
The Lsma.exe malware is a traditional instance of a cryptocurrency miner which depending upon its arrangement can create a wide variety of hazardous activities. Het belangrijkste doel is om ingewikkelde wiskundige taken uit te voeren die zeker zullen profiteren van de aangeboden systeembronnen: processor, GPU, geheugen evenals harde schijf ruimte. De methode die ze gebruiken, is door verbinding te maken met een unieke server genaamd mining pool van waaruit de vereiste code wordt gedownload. Zodra een van de banen wordt gedownload zal worden gestart op hetzelfde moment, meerdere instanties kunnen tegelijkertijd worden uitgevoerd. Wanneer een bepaalde taak is voltooid, wordt er nog één op zijn locatie gedownload en loopt de lus door totdat het computersysteem is uitgeschakeld, de infectie wordt verwijderd of een andere vergelijkbare gebeurtenis vindt plaats. Cryptogeld zal zeker beloond worden naar de correctionele controllers (hacken groep of een enkele cyberpunk) rechtstreeks naar hun begrotingen.
Een onveilige kwaliteit van deze categorie malware is dat voorbeelden zoals deze alle systeembronnen kunnen gebruiken en het doelcomputersysteem praktisch zinloos kunnen maken totdat de bedreiging volledig is geëlimineerd. De meeste hebben een permanente installatie waardoor ze moeilijk te verwijderen zijn. Deze opdrachten zullen aanpassingen aan alternatieven te starten maken, arrangement files as well as Windows Registry values that will certainly make the Lsma.exe malware begin immediately as soon as the computer is powered on. De toegang tot herstelmenu's en ook keuzes kunnen worden belemmerd, waardoor talloze handmatige verwijderingsoverzichten praktisch nutteloos zijn.
Deze specifieke infectie zal opstelling een Windows-service voor zichzelf, Door te voldoen aan de uitgevoerde veiligheids- en beveiligingsevaluatie zijn de volgende acties daadwerkelijk nageleefd:
. Tijdens de miner-procedures kan de aangesloten malware linken naar reeds lopende Windows-oplossingen en door derden geïnstalleerde applicaties. Hierdoor zien de systeembeheerders mogelijk niet dat de bronbelasting afkomstig is van een andere procedure.
| Naam | Lsma.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Lsma.exe |

Dit soort malware-infecties zijn bijzonder effectief bij het uitvoeren van geavanceerde opdrachten als ze zo zijn geconfigureerd. Ze zijn gebaseerd op een modulaire structuur die de criminele controleurs in staat stelt om allerlei gevaarlijke acties te orkestreren. Onder de geprefereerde voorbeelden is de wijziging van het Windows-register – wijzigingsreeksen die verband houden met het besturingssysteem kunnen aanzienlijke efficiëntieonderbrekingen veroorzaken en het onvermogen om toegang te krijgen tot Windows-oplossingen. Afhankelijk van de omvang van de wijzigingen kan het de computer ook volledig onbruikbaar maken. Aan de andere kant kan manipulatie van registerwaarden die behoren tot elke vorm van geïnstalleerde applicaties van derden, deze saboteren. Sommige toepassingen worden mogelijk helemaal niet vrijgegeven, terwijl andere onverwacht kunnen stoppen met werken.
Deze specifieke mijnwerker in zijn huidige versie is gericht op het minen van de Monero-cryptocurrency met een aangepaste versie van de XMRig CPU-mijnengine. If the campaigns verify effective then future variations of the Lsma.exe can be launched in the future. Als de malware maakt gebruik van software kwetsbaarheden te misbruiken doelhosts besmetten, het kan zijn onderdeel van een schadelijke co-infectie met ransomware en Trojaanse paarden.
Elimination of Lsma.exe is strongly recommended, aangezien u niet alleen het risico loopt van hoge stroomkosten als deze aan uw COMPUTER werkt, maar de mijnwerker kan er ook verschillende andere ongewenste taken op uitvoeren en ook uw pc permanent beschadigen.
Lsma.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Lsma.exe
STAP 5. Lsma.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Lsma.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Lsma.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Lsma.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Lsma.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Lsma.exe”.







